Welcome to our comprehensive guide on “Active Directory Domains and Trusts.” In any robust network environment, the way different domains interact with each other plays a pivotal role. These interactions are often facilitated through a mechanism known as “Trusts,” and managing these trusts efficiently is crucial for seamless access to resources and heightened security.
In this article, we will dissect what domains and trusts in Active Directory are, how to set them up, and how to manage them effectively. We’ll also delve into various use cases and best practices that will help you navigate the complexities of your network’s domain architecture. So, let’s begin our journey into the intricate world of Active Directory Domains and Trusts.
Jump to:
- Understanding Domains and Trusts in Active Directory
- Setting Up and Managing Trusts
- Use Cases and Benefits
- Best Practices and Security Considerations
1. Understanding Domains and Trusts in Active Directory
Navigating through the labyrinthine architecture of modern networks requires a thorough understanding of its foundational elements. Among these, domains and trusts stand out as central pillars for the organization and security of your network. So, let’s delve into these key concepts to better understand their roles and functionalities.
Definition of Domains
Firstly, a domain in the context of Active Directory is essentially a logical unit of organization within a network, providing a structured method of organizing, managing, and securing a set of network resources. It can include anything from user accounts and printers to servers and databases. A domain is controlled by a domain controller, which authenticates user access to resources within that specific domain.
Definition of Trusts
Next, trusts. In the realm of network management, a trust is a relationship established between two domains where one domain (known as the “trusting” domain) allows users from another domain (the “trusted” domain) to access resources. Trusts serve as bridges between distinct domain boundaries, allowing for controlled access and resource sharing while maintaining security policies.
Types of Trust Relationships
To add an extra layer of complexity, trusts aren’t a one-size-fits-all solution. There are several types of trust relationships designed to meet specific needs:
- Explicit Trusts: Manually configured by an administrator; these are not automatically created during domain setup.
- Implicit Trusts: Automatically created when domains are created or joined to a tree; these trusts are transitive in nature.
- Transitive Trusts: If Domain A trusts Domain B and Domain B trusts Domain C, then Domain A automatically trusts Domain C.
- Non-Transitive Trusts: These are one-way trusts that do not extend beyond two domains.
- Bidirectional Trusts: Trusts that allow users in both domains to access resources in the other domain.
- One-way Trusts: One domain allows access to users from another domain, but not vice versa.
- Forest Trusts: Established between forests, these trusts allow users from any domain in the forest to access resources in any domain of the other forest.
- Shortcut Trusts: These are manually created trusts within a forest that shorten the trust path to improve user logon times.
- Cross-Link Trusts: These are manually created trusts that optimize authentication requests between domains in different trees within the same forest.
- Realm Trusts: These connect an Active Directory domain to a UNIX realm.
By understanding these fundamental components and their various types, administrators can better design, implement, and manage their network environments. Domains and trusts act as the backbone for orchestrating a symphony of interactions among networked resources, enabling both security and functionality to coexist in harmony.
See also: Active Directory Sites and Services
2. Setting Up and Managing Trusts
So, you’ve gotten to grips with the definitions and types of trusts in Active Directory. Now, you might wonder, how do we go about establishing these trust relationships? Moreover, once they’re set up, how do we manage, verify, or even remove them? Well, you’re in luck. This chapter aims to guide you through these essential administrative tasks, making the process as seamless as possible.
Creating Trusts
First on the agenda is creating trusts. Before diving in, ensure you have administrative rights, as you’ll need them to carry out these tasks. Follow the steps below to set up a trust:
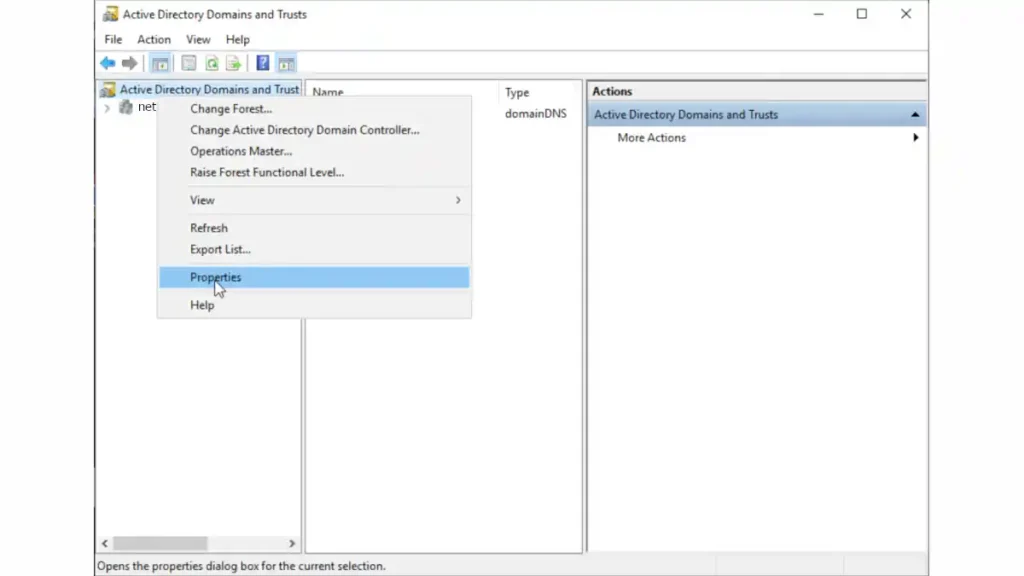
- Open Active Directory Domains and Trusts: Navigate to the Administrative Tools and launch the ‘Active Directory Domains and Trusts’ console.
- Select Domain: In the console tree, right-click the domain for which you want to establish a trust, then choose ‘Properties’.
- Access Trusts Tab: Switch to the ‘Trusts’ tab in the Properties dialog box.
- New Trust Wizard: Click on ‘New Trust’ and the New Trust Wizard will appear.
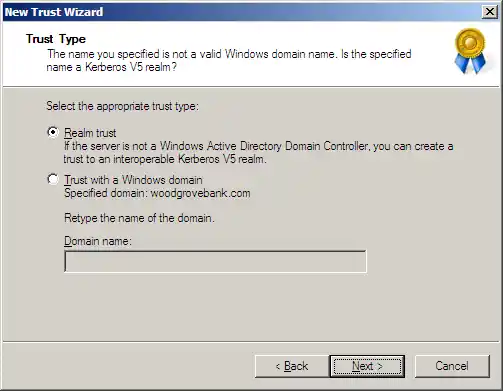
- Specify Trust Parameters: Follow the wizard’s prompts to specify the trust name, type, direction, and other attributes.
- Finalize: Review the settings and click ‘Finish’ to create the trust.
Voila, you’ve created a trust. But we’re not done yet.
Verifying Trusts
Once a trust is established, it’s prudent to verify its operational status. You can do so through the Active Directory Domains and Trusts console:
- Navigate to Trusts Tab: Just like when you were creating a trust, go to the ‘Trusts’ tab for the domain in question.
- Select Trust to Verify: Highlight the trust relationship you want to verify.
- Click on ‘Properties’: This opens a window detailing the trust attributes.
- Verification: Click on ‘Validate’, and you might be prompted to enter administrative credentials.
The system will run a verification check and confirm if the trust is active and operational.
Removing or Modifying Trusts
Now, let’s talk about altering or ending a trust relationship:
- Go to Trusts Tab: Head back to the ‘Trusts’ tab in the domain properties dialog box.
- Select Trust: Highlight the trust you want to modify or remove.
- Modify or Remove: Click ‘Properties’ to modify the trust attributes or ‘Remove’ to delete the trust altogether.
- Confirmation: You’ll be prompted for confirmation and possibly administrator credentials. Confirm to finalize the action.
There you have it—a comprehensive look at creating, verifying, and managing trust relationships in Active Directory. Armed with this knowledge, you can create a more secure, well-organized, and efficient network environment.
3. Use Cases and Benefits
So far, we’ve delved deep into the technical aspects of setting up and managing trusts in Active Directory. You might now be asking, “Why go through all this trouble? What are the real-world benefits?” Well, let’s pivot to the practical side of things. This chapter focuses on the compelling use cases and the undeniable advantages of using trusts in an Active Directory environment.
Interoperability Between Different Windows Versions
Firstly, let’s address a common scenario: you have different domains running on diverse versions of Windows Server. This situation could easily become an administrative nightmare. However, trusts in Active Directory bridge the gap effortlessly. By establishing trust relationships, you can ensure seamless interoperability between domains, irrespective of their underlying Windows Server versions. This compatibility is not just convenient; it’s a lifesaver for organizations that rely on legacy systems for critical operations.
Simplifying Resource Management
Next up is resource management, an often daunting task for administrators. Imagine you have users in one domain who need access to resources in another. Traditionally, you’d have to create multiple accounts and juggle numerous permissions, a recipe for complexity and errors. Trusts simplify this process substantially. By defining a trust relationship between the domains, you can grant permissions at an organizational level. This approach streamlines access, reducing the administrative burden and margin for error. In other words, trusts make your life easier—plain and simple.
Security Benefits
Lastly, let’s talk security. While it might seem counterintuitive, establishing trusts can enhance your network’s security posture. How so? Well, trusts enable you to centralize authentication and authorization procedures. This centralization allows for more stringent control over who gets access to what. Plus, it aids in easier monitoring of security events across interconnected domains. Furthermore, trusts can be one-way and non-transitive, giving you granular control over the level of access you grant, which is a massive win for security.
In conclusion, trusts in Active Directory are not just a technical prerequisite; they’re a tool for smarter, more secure management of your IT environment. From interoperability to streamlined administration and bolstered security, the benefits are far-reaching and impactful. So, the next time you question the utility of setting up trusts, remember: the advantages far outweigh the effort involved.
4. Best Practices and Security Considerations
Having navigated the intricate landscape of domains and trusts, you may wonder, “What now? How do I keep everything running smoothly while maintaining security?” Your concerns are absolutely valid. In this chapter, we aim to guide you through the best practices and essential security considerations for managing your Active Directory trusts.
Security Implications
First and foremost, let’s delve into the security implications of setting up trusts. Indeed, while trusts offer various benefits, they can also open up potential avenues for security breaches if not managed correctly. For instance, a poorly configured trust could inadvertently give users access to resources they shouldn’t have access to. Therefore, understanding the security ramifications is not a luxury; it’s a necessity. Adopt the principle of least privilege: grant only the level of access absolutely necessary for users to complete their tasks. Furthermore, ensure regular audits to spot any anomalies before they turn into security incidents.
Managing Trust Policies
Transitioning to the next critical area, managing trust policies can feel like walking a tightrope. The key is balance—striking the right equilibrium between accessibility and security. The use of Group Policy Objects (GPOs) in Active Directory can be immensely helpful here. Through GPOs, you can enforce security settings across your domains, ensuring uniform compliance. However, tread carefully. Over-restrictive policies could lead to loss of functionality, while lax policies could pose significant risks. Therefore, it’s advisable to periodically review and adjust trust policies, taking into account any changes in your IT landscape or business needs.
Recommended Tools for Management
Finally, let’s talk tools. In the ever-evolving world of IT, having the right tools in your arsenal can make or break your management strategy. There are multiple tools available for managing Active Directory trusts—both built into Windows and from third-party vendors. Microsoft’s Active Directory Administrative Center and the classic Active Directory Domains and Trusts MMC snap-in are solid starting points. For more advanced capabilities, third-party solutions like ManageEngine ADManager Plus or Quest ActiveRoles offer comprehensive trust management features. These tools not only simplify your day-to-day tasks but also provide advanced reporting capabilities, which can be invaluable for audit purposes.
To sum it all up, managing Active Directory trusts is a dynamic process that demands ongoing attention and adjustment. But with a keen understanding of the security implications, a balanced approach to policy management, and the right tools, you can maximize both the effectiveness and security of your trust relationships. By following these best practices and keeping security considerations at the forefront, you position yourself—and your organization—for success.