An “Anonymous User” is any user who accesses network resources without providing a username or password. This seemingly simple concept has broad applications and implications, especially when considered within diverse contexts like web services, server configurations, and even anonymous web browsing. In this article, we will delve into these contexts to provide you with a comprehensive understanding of what an anonymous user really is and what you should be aware of regarding network security and data access.
In this article:
- What is an Anonymous User?
- Anonymous Users in Microsoft Windows Server Applications
- Anonymous Users in Web Services
- Anonymous Users in E-commerce
- Anonymous Users in Forums and Social Media
- Anonymity vs. Pseudonymity
- Security Implications of Allowing Anonymous Users
- Legal and Ethical Considerations
- Best Practices for Managing Anonymous Users
- Conclusion
- References
1. What is an Anonymous User?
An “Anonymous User” is essentially any individual who gains access to network resources without the necessity of providing a username or password. In layman’s terms, these users are not required to identify themselves before they interact with the system. This is not merely a tech buzzword but a critical component of network architecture and security protocols.
Now, why does this matter? First, it’s important for resource allocation. In many systems, identified users are given personalized content and experiences, while anonymous users receive a generic version. Moreover, network administrators often need to manage permissions and restrictions differently for anonymous users. Without a thorough understanding of this user type, you risk either restricting access unnecessarily or exposing sensitive data.
2. Anonymous Users in Microsoft Windows Server Applications
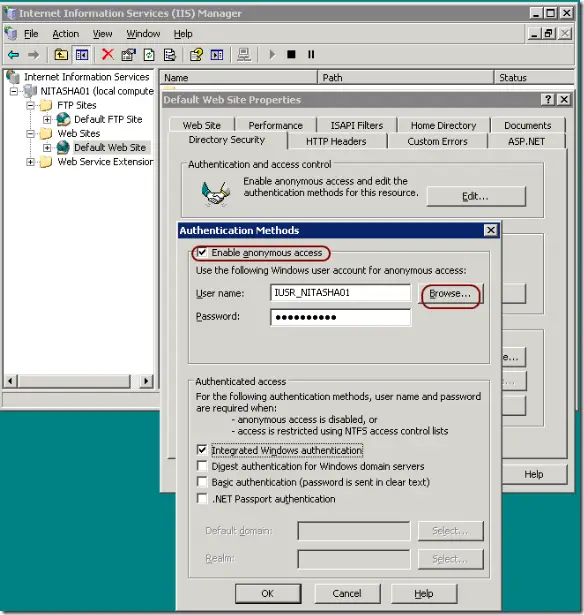
Microsoft Internet Information Services (IIS)
In the context of Microsoft’s Internet Information Services, or IIS, anonymous users play a pivotal role. IIS, a flexible and manageable web server, often serves content that is publicly accessible. To enable this, administrators may configure the server to allow anonymous access. Here, the anonymous user is predefined as “IUSR” and is generally given limited permissions. This approach ensures that public content is accessible while more sensitive data remains protected.
Active Directory
When we shift our gaze to Active Directory, the narrative changes a bit. Typically, Active Directory necessitates authentication for resource access. However, there are exceptions, particularly when it comes to public shared folders or printers. In these cases, the directory can be configured to recognize anonymous logons, effectively enabling access to a broader audience. Yet, it’s crucial to note that allowing such access can expose the network to various vulnerabilities. Hence, the decision to enable anonymous access should be made cautiously.
The Role of Anonymous Users in Accessing Public Resources
Broadly speaking, anonymous users facilitate the open dissemination of public resources. This accessibility serves to lower barriers for users who are either unfamiliar with the system or don’t require extensive interaction. For instance, public documentation, downloadable forms, and informational web pages are often set to allow anonymous access. This way, essential resources can be distributed widely without requiring a laborious login process.
In summary, the notion of an anonymous user may seem straightforward, but its implications are far-reaching. Especially in server configurations like IIS and directory services like Active Directory, understanding the roles and permissions of anonymous users is pivotal for both accessibility and security. Therefore, it’s not just about ease of use but also about implementing a rigorous security protocol that strikes the right balance.
3. Anonymous Users in Web Services
API Access
In the context of Web Services, the role of anonymous users is particularly complex. One area where they emerge is in the use of Application Programming Interfaces (APIs). Some web services offer public APIs that can be accessed without authentication. This is beneficial for encouraging the broad use and testing of the service, but it also poses significant risks. Unrestricted API access can lead to abuse, including data theft and Denial of Service (DoS) attacks. Therefore, even for anonymous access, rate limiting and other throttling techniques are often used to control the load and potential misuse.
Data Scraping
Data scraping is another domain where anonymous users can have both positive and negative impacts. On one hand, allowing anonymous scraping can facilitate the free flow of publicly available information. On the other, it can also lead to unauthorized data extraction and potential copyright infringement. Web services often have to deploy sophisticated mechanisms like CAPTCHA or user-agent analysis to deter or manage scraping activities.
Role-Based Access Control
One of the effective ways to manage anonymous users in web services is through Role-Based Access Control (RBAC). In this model, permissions aren’t given to specific users, but to specific roles. Anonymous users can be assigned a “guest” or “anonymous” role, with minimal permissions, just enough to browse public resources or utilize basic functionalities. This provides a balanced approach to maintaining functionality while mitigating risk, ensuring that anonymous users can access only what they are intended to see or use.
By employing techniques like API rate limiting, anti-scraping mechanisms, and role-based access control, web services can offer a level of openness and availability without compromising on security or functionality. It’s all about instituting the right checks and balances, so that anonymous users can be accommodated within a controlled, secure environment.
4. Anonymous Users in E-commerce
Guest Checkout
In the e-commerce landscape, the term “anonymous user” often manifests in the form of guest checkouts. This feature allows customers to make purchases without creating an account or providing exhaustive personal information. Essentially, this streamlines the buying process, potentially increasing conversion rates. However, it comes at the cost of less data collection, which can be vital for targeted marketing and customer relationship management.
Tracking and Data Analytics
While guest checkouts may limit the direct information an e-commerce platform can gather, tracking and analytics tools can still collect valuable data. Through cookies or session IDs, businesses can monitor the behavior of anonymous users—what they click, how long they stay, and what they abandon in their carts. Though not as rich as the data gathered from registered accounts, this information remains crucial for improving user experience and optimizing sales funnels. Thus, even when allowing anonymous transactions, strategic data collection is still very much on the table.
5. Anonymous Users in Forums and Social Media
Benefits and Drawbacks
Anonymous users have a mixed reputation in the realm of forums and social media. On one hand, anonymity allows for unfiltered, honest discussion and enables whistle-blowers or those in oppressive regimes to speak freely. On the other hand, it can also pave the way for online harassment, disinformation, and the propagation of extremist views. Therefore, the presence of anonymous users is a double-edged sword, providing both the freedom of expression and the potential for abuse.
Real-life Examples (Reddit, 4chan)
Take Reddit, for instance. Users can create pseudonymous accounts without providing real names or email addresses. This has led to rich subcultures and in-depth discussions on niche topics. However, it’s also given rise to controversial communities and the sharing of explicit or harmful content.
4chan takes this a step further by not requiring any form of account creation for posting. This model fosters a rapid, uninhibited flow of ideas but also serves as a breeding ground for extreme opinions and volatile behavior.
To summarize, anonymous users play nuanced roles depending on the platform they are part of. In e-commerce, they simplify transactions but pose challenges for data analytics. In forums and social media, they offer a platform for unrestrained dialogue but also create vectors for online misconduct. Balancing the pros and cons in each setting requires a nuanced understanding of the anonymous user’s impact on network resources and social interactions.
6. Anonymity vs. Pseudonymity
Differences and Similarities
At first glance, anonymity and pseudonymity might appear synonymous, but they serve different functions in the realm of online interactions. Anonymity refers to the state of being completely nameless, with no attached identifiers. Pseudonymity, on the other hand, involves the use of a fictitious name or alias that can be consistently linked to a particular user, though not necessarily to their real-world identity.
In terms of similarities, both anonymity and pseudonymity provide a layer of privacy, shielding the user’s true identity from public view. However, the key difference lies in traceability. While anonymous actions are designed to be unlinkable to any one individual, pseudonymous actions can be traced back to a single, albeit masked, entity.
Use-cases for Each
Anonymity is often sought in situations that require a single or short-term action where the identity of the user is unimportant or could be detrimental if revealed. Voting in online polls, providing candid feedback, or whistleblowing are examples where anonymity is beneficial.
Pseudonymity finds its place in scenarios where users may want to build a reputation or social standing without revealing their real-world identity. Online gaming, social media platforms, or professional forums like GitHub or Stack Overflow often benefit from pseudonymous interactions.
7. Security Implications of Allowing Anonymous Users
Allowing anonymous users into your network or platform isn’t without its security risks. The most glaring concern is the lack of accountability. With no identifying information, it becomes exceedingly difficult to track or moderate malicious behavior, including spam, data breaches, and other forms of abuse.
Furthermore, anonymous users can place an additional burden on system resources. Since these users aren’t easily trackable, rate limiting and other forms of abuse prevention can become more challenging to implement effectively.
That said, the risk is not insurmountable. Employing a robust security framework can mitigate these risks. Techniques like CAPTCHA, session tracking, and IP address flagging can add layers of security that deter abuse while still allowing for anonymous access.
In sum, while permitting anonymous users brings forth certain advantages in terms of accessibility and user-friendliness, it also opens up an array of security vulnerabilities. Striking a balance between openness and security is a crucial task, one that necessitates a deep understanding of both your platform’s needs and the potential risks involved.
8. Legal and Ethical Considerations
GDPR, CCPA, and Other Data Protection Laws
The advent of regulations like the General Data Protection Regulation (GDPR) in the European Union and the California Consumer Privacy Act (CCPA) in the United States has fundamentally altered the landscape of data collection and storage, even for anonymous users. These laws require explicit consent for data collection and provide users with the right to access or delete their data, among other protections. Therefore, even if a user is anonymous in the sense of not providing a username or password, any data collected about their behavior or preferences must still comply with these legal frameworks.
Ethical Implications of Data Collection
Beyond the letter of the law, ethical considerations also come into play. The mere act of allowing anonymous access should not serve as an excuse to collect data indiscriminately. Ethical best practices dictate transparency about what data is being collected and for what purpose. Ensuring that anonymous users have the option to opt-out of tracking mechanisms, like cookies, underscores a commitment to ethical data handling.
9. Best Practices for Managing Anonymous Users
Monitoring and Auditing
For the sake of both security and functionality, active monitoring and auditing are imperative when allowing anonymous users. Employ tools that can analyze user behavior in real-time and flag unusual activities, such as multiple failed login attempts or suspicious navigation patterns. Auditing should also be a routine exercise to ascertain the effectiveness of the existing security protocols.
Guidelines for Administrators and Webmasters
- Rate Limiting: Implement rate limiting on your services to mitigate potential abuse from anonymous users.
- CAPTCHA: Use CAPTCHA systems for forms and sensitive features to deter bots.
- Session Timeouts: Enforce automatic session timeouts to minimize the risk associated with unattended sessions.
- Logs and Alerts: Maintain detailed logs and set up alerts for specific activities such as bulk downloads, which could indicate scraping or data theft.
10. Conclusion
Understanding the multifaceted roles and implications of anonymous users is essential for anyone dealing with network resources, online platforms, or data security. While anonymity can offer freedom and accessibility, it is fraught with challenges that range from security concerns to legal obligations. Striking the right balance requires a nuanced understanding, comprehensive monitoring, and an ethical approach to data collection and user management.
11. References
- Books
- “Computer Networking: A Top-Down Approach” by James F. Kurose and Keith W. Ross
- “Network Security Essentials” by William Stallings
- “Data Protection and Privacy” by Ronald Leenes, Rosamunde van Brakel, Serge Gutwirth, and Paul De Hert
- Websites