An Application Gateway is more than just a network node; it serves as a gatekeeper, ensuring that only secure, compliant traffic can access network resources. This technology plays a crucial role in contemporary network architectures, particularly as threats become more sophisticated and targeted at application vulnerabilities.
This article delves into the intricate world of Application Gateways. We start by defining what an Application Gateway is and its fundamental concepts, tracing its evolution over time and its growing importance in modern network infrastructures. We then explore the operational mechanisms, dissecting how these gateways control and secure traffic. A comparative analysis with other network security solutions will provide a broader context, followed by practical insights into their implementation. Finally, concluding with a comprehensive roundup and a curated list of references for further reading.
Table of Contents:
- What is an Application Gateway Firewall?
- How Application Gateways Work
- Key Features of Application Gateways
- Application Gateway vs. Other Network Security Solutions
- Challenges and Limitations
- Conclusion
- References

1. What is an Application Gateway?
Application Gateway is a type of firewall that provides application-level control over network traffic. Application gateways can be used to deny access to the resources of private networks to distrusted users over the Internet.
Unlike traditional firewalls that operate at lower levels of the OSI model, Application Gateways function at the application layer (Layer 7). This advanced positioning allows them to inspect, filter, and route traffic based on the content of the data packets, rather than just the source and destination addresses. They are adept at understanding the specifics of web application protocols like HTTP/HTTPS and implementing policies that ensure secure communication.
Historical Evolution and Relevance in Modern Networks
The concept of Application Gateways emerged as internet usage proliferated and web applications became central to business operations. Initially, network security was predominantly focused on perimeter defenses, like packet-filtering firewalls. However, as cyber threats evolved, it became evident that deeper inspection and more granular control of traffic were necessary.
Application Gateways marked a significant shift in this landscape. They brought about the ability to scrutinize the payload of packets, looking for malicious content or non-compliance with protocol standards. This level of inspection became invaluable as attacks became more sophisticated, targeting application vulnerabilities directly.
In modern network environments, the relevance of Application Gateways has only intensified. With the advent of cloud computing, the Internet of Things (IoT), and an increasingly mobile workforce, network perimeters have become more fluid and less defined. Application Gateways offer a solution that adapts to these changes, providing a robust, flexible method of securing network traffic that aligns with the dynamic nature of today’s digital interactions.
Their ability to integrate with modern technologies, like cloud services and virtualized network environments, further cements their role as a cornerstone of contemporary network security strategies. As networks continue to evolve, Application Gateways will remain at the forefront, adapting to new challenges and safeguarding the integrity and availability of network resources.
2. How Application Gateways Work
Application gateways examine incoming packets at the application level and use proxies to create secure sessions with remote users. For example, when an external user with a Web browser tries to access the company’s internal web server, the application gateway runs a proxy application that simulates the internal web server.
A session is established between the remote user and the proxy application, while a separate, independent session is established between the proxy application and the internal web server. The remote user makes a request to the proxy, the proxy acts as a go-between and obtains the information from the internal web server, and then the proxy returns the result to the remote user.
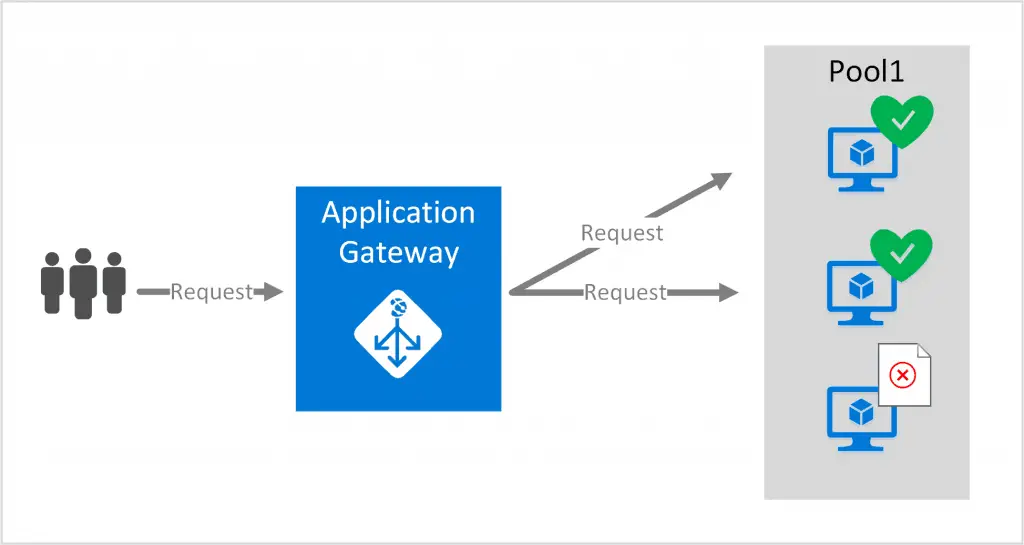
The advantage of using application gateways over packet-filtering routers is that in packet filtering, a direct network connection still exists between the remote user and the internal network resource, while an application gateway prevents the remote user from directly accessing the internal network resource.
This layer of additional security comes at some cost, namely that application gateways are generally slower and require a separate proxy application for each internal network service you want to make available through the firewall.
Types of Traffic and Protocols Managed
Application Gateways are particularly adept at managing traffic related to web applications. They primarily handle protocols like HTTP and HTTPS, the fundamental protocols of the World Wide Web. However, their capabilities extend to other application-level protocols as well, such as FTP (File Transfer Protocol), SMTP (Simple Mail Transfer Protocol), and DNS (Domain Name System).
These Gateways can also manage encrypted traffic, which is increasingly prevalent in modern networks. They have the ability to decrypt SSL/TLS traffic, inspect it for security threats, and then re-encrypt it before forwarding it to the intended recipient. This ability is crucial in a landscape where encryption is commonly used by both legitimate entities and attackers.
3. Key Features of Application Gateways
Traffic Control Capabilities
Application Gateways provide an advanced level of traffic control, enabling network administrators to implement granular policies for data transmission. This control extends to:
- URL Filtering: Restricting or allowing access to specific websites or paths based on URLs.
- Bandwidth Management: Allocating network resources by controlling the amount of bandwidth available to different types of traffic.
- Session Management: Controlling and monitoring active sessions to ensure secure and efficient use of network resources.
These capabilities are vital in managing network traffic flow, prioritizing essential services, and mitigating the risks of network congestion.
Security Features and Benefits
One of the primary advantages of Application Gateways is their enhanced security features, which include:
- Deep Packet Inspection: The ability to inspect the payload of packets, providing protection against application-level attacks such as SQL injection, cross-site scripting (XSS), and other common exploits.
- Anti-Malware and Virus Scanning: Scanning incoming traffic for known malware and viruses, thereby preventing the spread of infections within the network.
- Intrusion Prevention and Detection: Detecting and preventing intrusion attempts by monitoring traffic for suspicious patterns and behaviors.
- SSL/TLS Inspection: Decrypting, inspecting, and re-encrypting SSL/TLS traffic to identify hidden threats within encrypted data streams.
By leveraging these features, Application Gateways provide a robust security layer, protecting the network from a wide array of cyber threats, and ensuring the integrity and confidentiality of sensitive data. This enhanced security posture is essential in today’s increasingly complex and threat-prone digital landscape.
4. Application Gateway vs. Other Network Security Solutions
Comparative Analysis with Traditional Firewalls
- Layer of Operation: Traditional firewalls primarily operate at the network layer (Layer 3) and transport layer (Layer 4) of the OSI model, focusing on IP addresses and port numbers. Application Gateways, in contrast, work at the application layer (Layer 7), providing deeper insight into the content of the data packets.
- Traffic Inspection: Traditional firewalls conduct basic packet filtering, which checks the header information of data packets. Application Gateways offer deep packet inspection, scrutinizing the actual data within packets for more sophisticated threat detection.
- Protection Against Attacks: While traditional firewalls are effective against standard network threats, Application Gateways provide enhanced security against application-level attacks such as SQL injections, cross-site scripting, and other exploits targeting specific applications.
- Configuration Complexity: Application Gateways require more complex configuration and management compared to traditional firewalls, due to their advanced capabilities and detailed policy settings.
Comparative Analysis with Other Security Measures
- Intrusion Detection/Prevention Systems (IDS/IPS): These systems are designed to detect and possibly prevent known threats. Application Gateways, while also providing these functionalities, are more focused on regulating application-specific traffic and protecting against application-based vulnerabilities.
- Network Address Translation (NAT) Gateways: NAT Gateways provide IP address and port number translation services. They don’t offer the same level of security and traffic inspection as Application Gateways, which manage and secure application-level traffic.
5. Challenges and Limitations
Despite their advantages, Application Gateways come with certain challenges and limitations:
- Performance Impact: The deep packet inspection and detailed analysis of data can lead to increased latency, impacting network performance, especially in high-traffic environments.
- Complexity in Management: Due to their sophisticated nature, Application Gateways require skilled administrators for proper configuration and management. Incorrect configurations can lead to security gaps or network disruptions.
- Cost Considerations: Implementing and maintaining an Application Gateway can be more costly than traditional firewalls, both in terms of hardware/software expenses and the need for specialized personnel.
- Encryption Challenges: While they can inspect encrypted traffic, handling large volumes of SSL/TLS encrypted data can be resource-intensive, sometimes leading to bottlenecks.
6. Conclusion
Application Gateways represent a significant advancement in network security, offering a robust solution against sophisticated application-level threats. Their ability to perform deep packet inspection and enforce specific security policies at the application layer sets them apart from traditional firewalls and other security measures. However, considerations like performance impact, management complexity, and cost must be taken into account. Understanding these aspects is crucial for organizations looking to integrate Application Gateways into their security infrastructure effectively.
7References
- Books
- “Network Security Essentials” by William Stallings – Offers insights into various aspects of network security, including application gateways.
- “Computer Networking: A Top-Down Approach” by James Kurose and Keith Ross – Provides a comprehensive overview of networking principles, including application layer protocols and security measures.
- RFCs