Beaconing, in the context of computer networking, is a vital protocol mechanism primarily utilized in token-passing networks to maintain network integrity and performance. As technology has evolved, the term has also found relevance in wireless networking, with slightly different connotations. This article aims to elucidate the traditional use of beaconing in token-passing networks, like Token Ring and FDDI, and explore its modern adaptations in wireless protocols.
Jump to:
- Introduction to Beaconing
- Beaconing in Token-Passing Networks
- Beaconing in Wireless Networks
- Challenges and Limitations
- Conclusion
- References
1. Introduction to Beaconing
Definition and Historical Context in Token-Passing Networks
Beaconing, as a network term, primarily refers to the process of sending a series of signals to convey information about the status of various network operations. Historically, in token-passing networks such as Token Ring and Fiber Distributed Data Interface (FDDI), beaconing played a pivotal role. These networks, which dominated enterprise environments in the late 20th century, relied on a token—a small data packet—to grant devices the right to transmit data. Beaconing was the network’s intrinsic protocol response to disruptions, designed to maintain the seamless flow of communication and safeguard against data loss or collision.
Beaconing’s Dual Significance in Wireless Networks
In contemporary wireless networks, the term beaconing has been adapted to describe the transmission of beacon frames by wireless access points (APs). These frames serve as announcements that broadcast essential network details necessary for devices to connect and communicate effectively. Unlike its use in token-passing networks, where it primarily signaled an error or a status, in wireless networks, beaconing is a constant and standard part of network communication, critical for the initiation and maintenance of wireless links.
2. Beaconing in Token-Passing Networks
The Mechanism of Beaconing
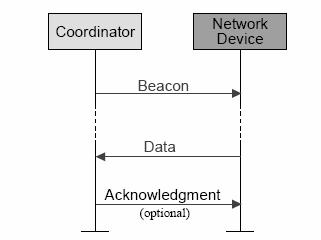
- How Beaconing Monitors the Token-Passing Process: In token-passing networks, the integrity of data transmission hinges on the token’s unimpeded travel. Beaconing comes into play when this critical passage is interrupted. The affected station emits a beacon signal to alert the network of the anomaly. This signal allows other stations to identify a problem within the network without having to wait for a timeout period, thus speeding up the fault identification and recovery processes.
- Beacon Frames and Their Structure: A beacon frame is a particular type of frame distinguished by its structure, which contains information identifying the station that detected the problem, the nature of the fault, and the domain in which the fault was detected. It acts as a red flag in the network’s ongoing data stream, distinct from regular data packets, ensuring immediate recognition.
Fault Isolation with Beaconing
- Detecting and Responding to Network Faults: Upon detecting a fault, a station begins to beacon, sending out a signal that prompts adjacent stations to enter a bypass state or to propagate the beacon further, thereby allowing the network to trace and isolate the fault.
- The Process of Fault Identification Using Beacons: As beacons are propagated, they help delineate the boundaries of the fault. This is achieved by analyzing the sequence and source of beacon frames, enabling network administrators to pinpoint the fault’s location accurately and swiftly initiate recovery actions.
Case Studies: Token Ring and FDDI
- Specifics of Beaconing in Token Ring Networks: In a Token Ring network, if a station does not receive the token within a specified time, it will issue a beacon frame. These frames contain the station’s address and a specific beacon type indicating the nature of the issue, which is critical information for fault analysis and rectification.
- Beaconing’s Application in FDDI Networks: FDDI networks, designed for higher-speed operations, adopted beaconing with enhancements suitable for their dual-ring infrastructure. When a primary ring fault was detected, the beaconing helped switch operations to the secondary ring, thereby ensuring network resilience and continuity.
The detailed explanation of beaconing’s role in maintaining network stability in both token-passing and wireless networks not only emphasizes its fundamental importance in historical networking protocols but also highlights its adaptability and relevance in the current technological landscape.
3. Beaconing in Wireless Networks
Beacon Frames in Wi-Fi Networking
- Functionality and Structure of Wi-Fi Beacon Frames: In Wi-Fi networking, beacon frames are periodically transmitted by wireless access points to announce the presence of a wireless LAN and to synchronize the members of the service set. These frames are pivotal to network discovery and configuration as they contain essential information such as the Service Set Identifier (SSID), supported data rates, and information about the network topology.
- Managing Network Connectivity and Synchronization: Wi-Fi beacon frames facilitate the connectivity management process by enabling devices to locate a network and tune to the correct channel for communication. They are crucial for time synchronization within the network, allowing client devices to align their internal clocks with the timing of the access point’s transmissions. This is essential for maintaining order in the shared wireless medium and scheduling time-sensitive communications.
Role in Other Wireless Protocols
- Bluetooth and Zigbee: Beaconing in Bluetooth technology, especially within Bluetooth Low Energy (BLE), serves primarily for proximity detection and broadcasting information to nearby devices, commonly used in location-based services and advertising. Zigbee, utilized for its low-power digital radios, employs beaconing for network organization and maintenance, particularly in establishing and maintaining device roles within its mesh network.
- Proximity Detection and Advertising: The utility of beaconing in both Bluetooth and Zigbee protocols extends beyond mere connectivity; it is instrumental for proximity services, which enable contextual awareness for devices. In marketing, beacons are used to push advertisements to users based on location, significantly enhancing customer engagement strategies.
4. Challenges and Limitations
Issues in Token-Passing Networks
- Latency and Network Traffic Considerations: Token-passing networks inherently faced challenges of latency, particularly as network size and utilization increased. The process of beaconing, while essential for fault isolation, introduced additional overhead and could exacerbate latency if not managed efficiently. Additionally, heavy network traffic could lead to token collisions and the need for more frequent beaconing, complicating the maintenance of network performance.
Concerns in Wireless Beaconing
- Collision, Interference, and Security Vulnerabilities: In wireless networks, beaconing must be carefully coordinated to minimize collisions due to the shared nature of the wireless medium. Interference from multiple networks can corrupt beacon frames, leading to connectivity issues. Security is also a significant concern, as beacon frames are unencrypted, making them susceptible to spoofing and unauthorized access, which could compromise network security.
5. Conclusion
The practice of beaconing in networking, whether in the historical context of token-passing networks or the modern arena of wireless communication, represents a fundamental technique essential for the maintenance, organization, and efficiency of network operations. In token-passing networks, beaconing provided a robust method for fault isolation, critical for network reliability. Transitioning to wireless networks, beaconing assumes a new role, facilitating network discovery and management, as well as enabling advanced services like location-based advertising and context-aware services.
Despite its undeniable utility, beaconing is not without challenges. Latency, network traffic, collision, and security vulnerabilities remain areas requiring ongoing attention. As networking technology evolves, so too must the methodologies for beaconing, with a constant push towards enhancing efficiency, reducing overhead, and fortifying security.
6. References
To corroborate the information presented and provide further reading for those interested, the following references have been selected:
- Stallings, W. (2005). “Wireless Communications & Networks.” Prentice Hall. This text provides insights into the wireless networks’ structure and the role of beacon frames in these environments.
- IEEE Standards Association. (2002). “IEEE Std 802.11-2007: Wireless LAN Medium Access Control (MAC) and Physical Layer (PHY) Specifications.” This standard outlines the technical specifications for Wi-Fi beacon frames.
- Zimmerman, H. (1980). “OSI Reference Model—The ISO Model of Architecture for Open Systems Interconnection.” IEEE Transactions on Communications. This paper, while not directly about beaconing, provides foundational understanding of network protocols and architecture.
- Comer, D. E. (2000). “Internetworking with TCP/IP Vol. I: Principles, Protocols, and Architecture.” Prentice Hall. Comer’s work is seminal in understanding network protocols and includes discussions on network maintenance techniques like beaconing.
- Bluetooth SIG. (2010). “Bluetooth Core Specification.” This document details the Bluetooth technology where beaconing is used for proximity detection.
- The Zigbee Alliance. (2015). “Zigbee Specification.” This outlines Zigbee’s application of beaconing for network organization.
- Chlamtac, I., Conti, M., & Liu, J. J. N. (2003). “Mobile ad hoc networking: imperatives and challenges.” Ad Hoc Networks, 1(1), 13-64. This research offers insight into challenges faced in mobile ad hoc networks, including beaconing-related issues.
- RFC 675 – Specification of Internet Transmission Control Program. This foundational document, while historic, helps understand the evolution of network protocols to which beaconing is integral.
These references provide a thorough backdrop against which the past, present, and future of beaconing can be understood. Whether for academic study, professional reference, or personal curiosity, they offer a pathway to a deeper understanding of the principles and practices of networking beaconing.