Unveil the world of cryptographic hash functions as we break down SHA-256. Understand its vital role in ensuring data integrity and security in the digital realm.
In this article:
- Introduction
- What is SHA-256?
- The SHA-2 Family: Understanding the Context of SHA-256
- Cracking the Code: How Does SHA-256 Work?
- Vital Properties of SHA-256: Determinism, Avalanche Effect, and Resistance
- Applications of SHA-256: Beyond Just Encryption
- SHA-256 in Blockchain and Bitcoin: A Special Relationship
- Critiques and Limitations of SHA-256
- The Future of Cryptographic Hash Functions: From SHA-2 to SHA-3
- Conclusion
- Additional Resources
Introduction
In the cryptic realm of cryptography, one encounters an array of algorithms, each serving a unique purpose in safeguarding our digital transactions and communications. Among them, SHA-256, a popular cryptographic hash function, holds a significant position. It forms the bedrock of various security protocols and systems, ensuring data integrity and authenticity in an increasingly interconnected world.
As we delve into the mysteries of SHA-256, it’s important to understand that this isn’t just an abstract concept exclusive to data scientists or cryptography enthusiasts. Whether you’re sending an email, transacting online, or even mining Bitcoin, SHA-256 is silently working behind the scenes, protecting your data from corruption and prying eyes. This article aims to explain what SHA-256 is, dissecting its inner workings, and unveiling its significance in our digital lives.
What is SHA-256?
SHA-256, an acronym for Secure Hash Algorithm 256-bit, is a member of the SHA-2 (Secure Hash Algorithm 2) family, a collection of cryptographic hash functions designed by the National Security Agency (NSA) and published by the National Institute of Standards and Technology (NIST). It’s designed to take an input (or ‘message’) and return a fixed-size string of bytes, typically a ‘digest’ that is 256 bits long. The magic of SHA-256 lies in the unique properties of this output.
Firstly, it’s deterministic, meaning that the same input will always produce the same output. However, even the slightest modification to the input – as minuscule as changing a single character – results in a drastically different output, a phenomenon known as the ‘avalanche effect’. Secondly, it’s practically impossible to generate the original input value from the hash output, a characteristic known as ‘pre-image resistance’. Lastly, it’s infeasible to find two different inputs that hash to the same output (‘collision resistance’).
In essence, SHA-256 serves as a digital fingerprinting tool for data. It’s leveraged across various applications ranging from password security and digital signatures to blockchain technology, where it forms the foundation of Bitcoin’s proof-of-work system.
The SHA-2 Family: Understanding the Context of SHA-256
As we journey into the dense thicket of modern cryptographic hash functions, it becomes crucial to understand that SHA-256 doesn’t exist in isolation. It is a member of a larger family, appropriately named the SHA-2 family. Comprehending SHA-256 requires us to first unravel its broader context, to comprehend the genetic material, so to speak, from which it’s derived.

The Secure Hash Algorithm 2, or SHA-2, is a set of cryptographic hash functions, codified in six unique hash values that range from 224 to 512 bits: SHA-224, SHA-256, SHA-384, SHA-512, SHA-512/224, and SHA-512/256. The number trailing the acronym refers to the length of the hash digest produced by the respective algorithm. For instance, SHA-256 produces a digest that is 256 bits long. The NSA designed this family, while the NIST published it as a Federal Information Processing Standard.
SHA-2 core characteristics
The SHA-2 family members share some core characteristics. They are all deterministic, producing the same hash value for the same input. They are all designed to deliver pre-image resistance, making it computationally infeasible to deduce the original input from the hash value. Finally, they are all structured to provide collision resistance, making it virtually impossible to find two distinct inputs that result in the same hash output.
Yet, the siblings within this family are not identical twins. They exhibit differences, primarily in their digest sizes and computational requirements. Larger digest sizes generally offer greater security, making them resistant to potential attacks, but they demand more computational resources. For example, SHA-512 provides higher security levels than SHA-256, but it’s more resource-intensive. On the other hand, SHA-256 strikes a balance between security and efficiency, making it a popular choice for many applications.
SHA-256’s place in the SHA-2 family
Understanding SHA-256’s place in the SHA-2 family allows us to appreciate its unique position within this set of cryptographic tools. It’s neither the strongest nor the most lightweight, yet it serves as a powerful middle-ground solution, providing substantial security without being overly resource-intensive. It is this delicate balance that has cemented SHA-256’s status as an indispensable tool in the cryptography toolbox.
In the grand tapestry of cryptographic hash functions, the SHA-2 family forms a crucial thread, and within this family, SHA-256 shines as a bright star, offering a potent mix of security and efficiency. It’s this context that allows us to appreciate the role and relevance of SHA-256 in our digital ecosystem. As we proceed to dissect SHA-256’s workings in the subsequent chapters, keep in mind this broader context—SHA-256 is but one player in a larger ensemble, each contributing to the symphony of secure digital communication.
» To read next: What is a Hackathon?
Cracking the Code: How Does SHA-256 Work?
Embarking on an expedition to decipher how SHA-256 works is akin to venturing into a labyrinth of algorithms and mathematical operations, armed with the desire to unveil the intricate symphony of steps that convert raw data into a unique digital fingerprint. Our journey traverses binary arithmetic, logical functions, and number theory, ultimately revealing the mathematical genius that powers SHA-256.
512 bits data blocks
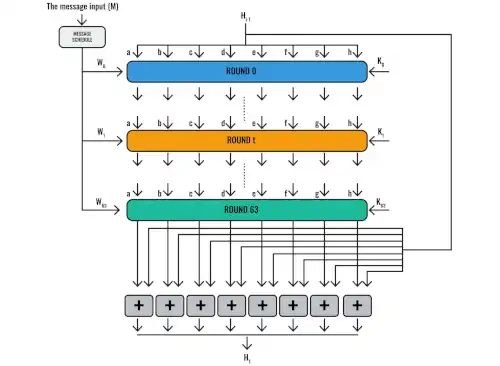
SHA-256 operates on data blocks of 512 bits each, running them through a series of well-orchestrated steps. Initially, the input message is preprocessed, which includes padding the message to fit the required block size and appending the message length. The process continues with dividing the input into 512-bit blocks, initializing hash values (derived from the fractional parts of the square roots of the first eight prime numbers), and setting up a sequence of constant values (derived similarly from the cube roots of the first sixty-four prime numbers).
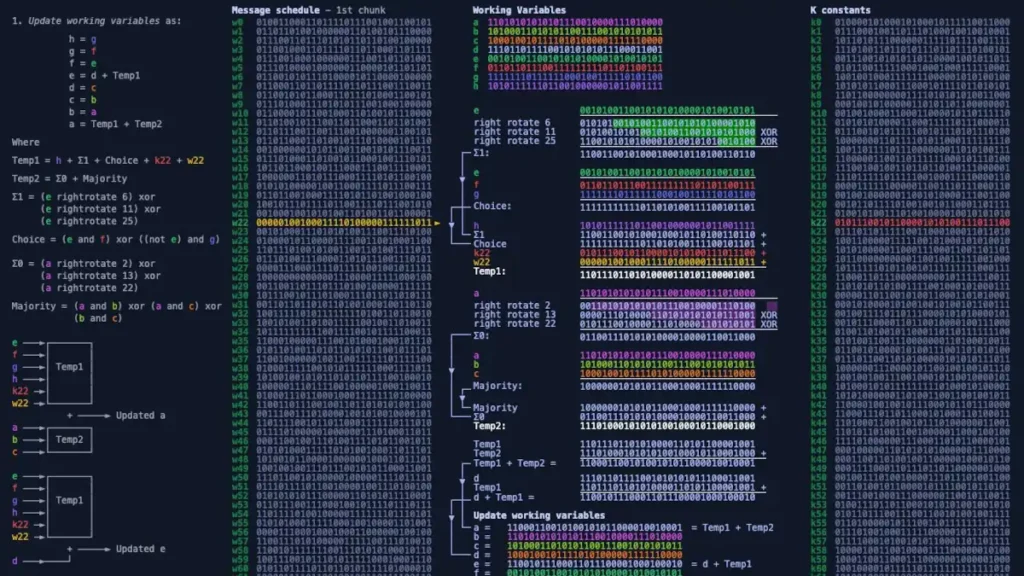
The message schedule
Then comes the heart of the SHA-256 algorithm, the message schedule, and the main loop. The 512-bit block is divided into sixteen 32-bit words. Through a series of bitwise operations and logical functions, these words are expanded into sixty-four words. This expansion is called the message schedule.
In the main loop, each of these sixty-four words goes through a sequence of operations. These include logical functions known as Majority (Maj), Sigma (Σ), and Ch (short for ‘choose’), bitwise operations, and modular arithmetic, all interwoven in a complex, yet precise, sequence. The hash values undergo permutations influenced by the words, the constants, and the results of these operations.
A chain of hash values
After all, sixty-four words have been processed in this manner, the resultant hash values are added to the initial hash values from the start of the block. This sum forms the hash of the block. Each block undergoes this process, with the final hash values from one block becoming the initial values for the next, forming a chain.
Once all blocks have been processed, the eight 32-bit hash values are concatenated, producing the final 256-bit hash output. This output, a unique identifier, is the digital fingerprint of the original message.
The elegance of mathematical logic in action
In sum, the process of SHA-256 is a labyrinth of precise steps and calculations. Every character, every bit of the input, is taken into account in the production of the output hash, reinforcing the fact that even the slightest change in the input creates a drastically different output. The result is a robust, secure, and highly efficient cryptographic hash function, a testament to the power and elegance of mathematical logic and number theory in the realm of digital security.
This complex process underpins SHA-256’s deterministic nature and resistance to collisions and pre-image attacks. It is the intricate dance of logical and arithmetic operations that fortify the wall of security SHA-256 offers to the data we send into the digital ether every day.
Vital Properties of SHA-256: Determinism, Avalanche Effect, and Resistance
As we delve deeper into the realm of SHA-256, we find ourselves standing before a trio of cardinal properties that constitute the fortress of its security and reliability. This triad – determinism, the avalanche effect, and various resistances – is the core around which SHA-256’s strength and value orbit.
Determinism
SHA-256 is deterministic, meaning that it produces the same hash output for the same input, no matter how many times the operation is repeated. In an ocean of possible inputs, from a single character to the complete works of Shakespeare, each unique input navigates unerringly to its singular hash output. This consistent mapping, unfazed by the volume or frequency of computations, is foundational to SHA-256’s utility in verifying data integrity. Even the smallest mutation in the input – a single bit flipped, a single character altered – will yield a radically different hash. Therefore, even infinitesimal data corruption or tampering will echo loudly in the hash output, signaling data integrity issues with the subtlety of a foghorn.
Avalanche Effect
Closely related to determinism is the avalanche effect, a property that ensures even a minuscule change in input creates a significant, cascading effect on the output. In the SHA-256 algorithmic avalanche, a single bit change in the input doesn’t merely alter a corresponding bit in the output. Instead, it triggers a landslide of change across the output hash, rendering it virtually unrecognizable from the original. This dramatic transformation in the face of minor input tweaks amplifies SHA-256’s sensitivity to data tampering, making it a trustworthy sentry of data integrity.
Resistance
The final vertex of this trinity is SHA-256’s resistance to common threats that lurk in the cryptographic shadows. Its preimage resistance ensures that it’s computationally infeasible to reverse-engineer the input from its hash output, safeguarding the original data. Its second preimage resistance asserts that given an input and its hash, it’s near impossible to find a different input with the same hash, reinforcing the reliability of SHA-256 in verifying data integrity. Lastly, its collision resistance protects against the possibility of finding two distinct inputs that hash to the same output, further buttressing its role in data integrity and authentication.
In this cryptographic triptych of determinism, the avalanche effect, and various resistances, SHA-256 finds its strength and utility. These properties underpin its indispensability in numerous applications, from digital signatures and certificates to blockchain technologies. Each property, like a thread in a complex tapestry, interweaves to form the resilient fabric of SHA-256, providing us with a reliable, secure, and efficient tool in the realm of digital data management. As we move forward in this digital age, these characteristics will continue to cement SHA-256’s place in our growing array of cryptographic tools.
Applications of SHA-256: Beyond Just Encryption
In the sprawling panorama of the digital domain, the influence of SHA-256 stretches beyond the conventional precincts of encryption, casting its significant shadow over a myriad of applications. It is more than just a cryptographic jigsaw piece; it is a technological touchstone that reinforces the integrity of digital landscapes, from the glistening peaks of blockchain technology to the fertile plains of digital signatures and file integrity checks. In this chapter, we will explore the multitude of realms where SHA-256 is not just a participant but a pivotal player.
Digital signatures
In the digital signatures realm, SHA-256 operates as a custodian of authenticity and non-repudiation. When a document is signed digitally, the original document is hashed using SHA-256, and this hash is then encrypted using the signer’s private key. The resulting digital signature is a testament to the document’s integrity and the signer’s identity.
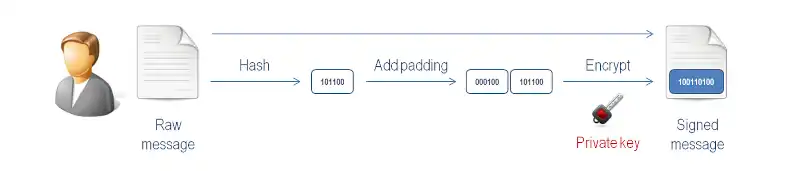
Any alteration, however slight, to the document after it has been signed will result in a different hash when verified with the signer’s public key, revealing the tampering attempt. Here, SHA-256’s determinism and sensitivity to input changes ensure the credibility of the digital signature, thereby securing the sanctity of the document and the accountability of the signer.
File integrity
SHA-256 also dons the mantle of a guardian in the realm of file and system integrity checks. Software applications, operating systems, and digital media often come with a published sha256 hash. After downloading such files, users can compute the SHA-256 hash of the downloaded file and compare it with the published hash. If they match, the integrity of the file is assured. Any discrepancy points to data corruption or malicious modification during transmission, alerting the user to potential risks. This application leans heavily on SHA-256’s determinism and preimage resistance properties, providing a reliable mechanism for file integrity verification.
Blockchain technology
Perhaps the most resounding echo of SHA-256’s influence is in the cavernous hall of blockchain technology, the bedrock of cryptocurrencies like Bitcoin. Blockchain uses SHA-256 not only for creating transactional checksums but also in the process of mining new blocks. Here, miners must solve complex mathematical problems that involve finding an input (or nonce) that, when hashed with the transaction data, produces a hash output that meets certain conditions. This ‘proof-of-work’ mechanism, reliant on SHA-256’s computational complexity and preimage resistance, discourages fraudulent transactions and secures the blockchain network against attacks.
These applications of SHA-256, among others, illustrate its versatility and indispensability in the digital realm. As we continue our march into an increasingly digital future, the importance and influence of SHA-256 are only likely to grow, continuing to shape and secure the digital landscapes we inhabit. Its multiple resistances, the avalanche effect, and determinism are not just mathematical curiosities; they are the pillars that uphold the integrity of our digital interactions and transactions.
SHA-256 in Blockchain and Bitcoin: A Special Relationship
When we delve into the cryptographic cornerstone of Bitcoin and other cryptocurrencies, we find that the stately fortress of Blockchain technology stands firmly on the bedrock of SHA-256. This cryptographic algorithm, with its confluence of determinism, the avalanche effect, and a trifecta of resistances, forms a special bond with Blockchain, one that has been instrumental in the surge of cryptocurrencies into the zeitgeist of the digital age.
Bitcoin
Blockchain, at its heart, is a public, decentralized ledger of all transactions that ever happened in a given cryptocurrency, the most famous of which is Bitcoin. The ‘chain’ in Blockchain refers to the sequential chain of blocks, each containing a set of transactions. When a block is ‘mined’ and added to the chain, it includes a hash of all the transactions it encapsulates, the hash of the previous block in the chain, and a unique value called a nonce. In Bitcoin, the nonce is a value that miners must find such that when it’s hashed with the transaction data using SHA-256, the resulting hash meets certain conditions, a process known as ‘proof-of-work.’
This ‘proof-of-work’ mechanism is a puzzle at the heart of Bitcoin mining, one that leans heavily on the SHA-256 hash function. This puzzle is computationally intensive to solve, thanks to the preimage resistance of SHA-256, but easy for others to verify. The miner who solves this puzzle first adds the new block to the chain and reaps a reward in Bitcoin, thus incentivizing miners to participate in maintaining the blockchain’s integrity.
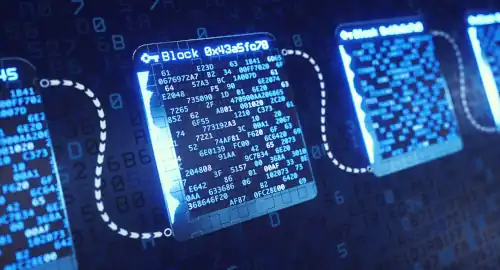
Furthermore, SHA-256’s determinism and the avalanche effect play pivotal roles in ensuring the immutability of the blockchain. Once a block has been added to the chain, altering the data in the block would change its hash. Because each block contains the hash of the previous block, changing one block would necessitate changes in all succeeding blocks to keep the hashes consistent, a computational feat near impossible due to the avalanche effect and the computational complexity of SHA-256.
The use of SHA-256 also imparts to Bitcoin its crucial feature of transparency. Every transaction can be verified by computing the hash, making it almost impossible for fraudulent transactions to go undetected. Yet, thanks to the one-way nature of SHA-256, the details of the transaction can remain private, ensuring confidentiality while maintaining transparency.
Thus, the SHA-256 hash function is more than just an algorithm in the world of Bitcoin and blockchain; it is the cryptographic linchpin that holds the entire system together. Its distinctive properties ensure the security, transparency, and integrity of transactions, providing the robustness that has allowed Bitcoin to flourish. It’s no exaggeration to say that without SHA-256, the landscape of cryptocurrencies, as we know it today, would be vastly different. In this regard, the relationship between SHA-256 and blockchain is indeed special; one might even say, it is the ‘cryptographic currency’ that fuels the engine of Bitcoin and other cryptocurrencies.
Critiques and Limitations of SHA-256
As we find ourselves standing in the august presence of SHA-256, it is tempting to be wholly awed by its cryptographic prowess and versatility. Yet, it is equally essential to delve into the shadows that trail behind the beacon of this formidable hash function. In this chapter, we will soberly scrutinize the critiques and limitations of SHA-256, reminding ourselves that even the most seemingly indomitable of cryptographic mechanisms is not without its Achilles’ heel.
Efficiency
The most significant critique levied against SHA-256 resides in the realm of computational efficiency, particularly with large data sets. SHA-256, by virtue of being a member of the SHA-2 family, follows a Merkle–Damgård structure. This structure requires the entire message to be processed for the hash computation. As data size grows, so does the time and computational resources needed to generate the hash. In an era where data is a ceaselessly flowing river, this time complexity becomes a noticeable limitation, particularly for systems that are either processing large volumes of data or are limited in computational resources.
Complexity
This computational complexity also contributes to what is known as the ‘blockchain trilemma’, particularly within the context of proof-of-work blockchains like Bitcoin. The trilemma posits that blockchain systems can only ever optimize two out of the three aspects simultaneously: decentralization, security, and scalability. The computationally intensive nature of the SHA-256 proof-of-work mechanism used in Bitcoin mining presents a barrier to scalability while also promoting centralization, as those with more computational resources are more likely to solve the hash problem and mine the block.
Quantum computing threat
Lastly, we should consider the advances in quantum computing. While still in its infancy, quantum computing possesses the potential to pose a significant threat to hash functions like SHA-256. Quantum computers operate on quantum bits or ‘qubits’, which, unlike classical bits, can exist in multiple states at once thanks to a quantum phenomenon known as superposition. This property could allow quantum computers to compute hashes at a speed exponentially faster than classical computers, potentially making brute-force attacks against SHA-256 feasible.
Despite these limitations, it is essential to remember that as of my knowledge, no practical attacks against SHA-256 have been successful. Its structure and complexity continue to provide robust security in the face of evolving computational capabilities. However, keeping these critiques in mind is vital for the continued evolution and enhancement of cryptographic methods. By acknowledging the limitations of SHA-256, we can continue the perpetual quest for cryptographic mechanisms that provide increased efficiency, scalability, and quantum resistance while ensuring the level of security that has made SHA-256 the titan it is today.
The Future of Cryptographic Hash Functions: From SHA-2 to SHA-3
As we traverse the realm of cryptography, the course is ever-evolving, shaped by the relentless tide of technological progress and the shifting sands of security needs. Amidst this landscape, one landmark has risen in recent years, promising to be the next beacon in cryptographic hash functions — SHA-3. This chapter, dear reader, is our forward gaze into the future, our exploration of this new horizon in the cryptographic odyssey.
Introduced as the victor of the NIST hash function competition in 2012, SHA-3, despite sharing its name with its SHA-2 predecessors like SHA-256, is a breed apart. It introduces a novel cryptographic structure known as the Keccak sponge construction, a departure from the Merkle–Damgård structure of SHA-2. This structure has a significant implication for SHA-3’s resistance against length-extension attacks, a vulnerability present in SHA-2 functions. In simpler terms, where an attacker might exploit the Merkle-Damgård construction to append additional data to a hash function’s input without knowing the original data, the sponge construction of SHA-3 provides immunity against such intrusions.

But the distinctions between SHA-3 and SHA-2 don’t stop at structural deviations. SHA-3 also offers greater flexibility compared to SHA-2. Its variable output length allows it to function as both a hash function and a stream cipher. It also exhibits increased efficiency when implemented in hardware, a boon for devices with limited computational resources. It’s important to note, however, that SHA-3 hadn’t yet been widely adopted. That said, these features provide compelling incentives for future adoption as the computational landscape continues to evolve.
Quantum computing, again
In the face of quantum computing’s potential threat to cryptographic hash functions, SHA-3 holds no inherent advantage over SHA-2. Both remain susceptible to Grover’s algorithm, a quantum algorithm that could halve the bit security of hash functions. However, in recognition of the looming quantum era, NIST has already initiated a process to standardize quantum-resistant cryptographic algorithms. It is not inconceivable that future iterations of SHA or entirely new hash function families might integrate quantum resistance as a core feature.
As we step into the future, the SHA-2 functions, including SHA-256, continue to hold their ground, fortified by their time-tested security and widespread adoption. However, the winds of change are stirring. As SHA-3’s adoption increases, we may find it, and other yet-undiscovered hash functions, reshaping the cryptographic landscape. As we navigate this evolving domain, our understanding of SHA-256 and its critiques and limitations will serve as a valuable compass, guiding our assessment of new hash functions and our pursuit of a secure digital future.
Conclusion
In conclusion, our journey through the world of SHA-256 has illuminated not only its formidable cryptographic capabilities but also its intricate ties to the technological fabric of our society, from safeguarding passwords to underpinning cryptocurrencies. We’ve dissected its properties, marveled at its applications, and pondered its critiques and limitations. We have also glimpsed the potential future of cryptographic hash functions, embodied in the emergence of SHA-3.
SHA-256, a star in the constellation of SHA-2, stands tall in the pantheon of cryptographic hash functions. Its impressive resistance against preimage, second preimage, and collision attacks, its deterministic yet avalanche-inducing behavior, and its broad applications highlight its critical role in our digital lives. However, we have also seen that it is not without its limitations, most notably its computational complexity, vulnerability to length-extension attacks, and the potential threat posed by quantum computing.
Yet, the presence of these limitations is not a testament to SHA-256’s weakness but rather to the relentless march of technological and computational progress. It is this very progress that has birthed SHA-3, with its novel Keccak sponge construction and increased flexibility and efficiency. As we look to the future, it is clear that the saga of cryptographic hash functions is far from over.
While this article serves as a comprehensive exploration of SHA-256, it is but a single thread in the vast tapestry of cryptography. The fascinating world of cryptographic hash functions continues to evolve and grow, with existing algorithms being continually tested and new ones being developed. As we navigate this ever-changing landscape, may our understanding of SHA-256 serve as both an anchor and a compass, a testament to how far we’ve come and a guide to the exciting cryptographic horizons that lie ahead.
Additional Resources
There are several resources that delve into the world of cryptographic hash functions, including SHA-256. Here are some books that can offer an extensive understanding of this subject:
- “Understanding Cryptography: A Textbook for Students and Practitioners” by Christof Paar and Jan Pelzl – While not exclusively about SHA-256, this book provides a solid understanding of cryptographic algorithms, which includes a deep dive into SHA-256.
- “Applied Cryptography: Protocols, Algorithms and Source Code in C” by Bruce Schneier – Known as one of the best practical guides to cryptography, it offers a detailed view on cryptographic hash functions.
- “Cryptography Engineering: Design Principles and Practical Applications” by Niels Ferguson, Bruce Schneier, and Tadayoshi Kohno – This book explains the principles needed to understand hash functions like SHA-256 and provides real-world examples of their applications.
- “Introduction to Modern Cryptography” by Jonathan Katz and Yehuda Lindell – A more academic approach to the subject but very complete. It offers a strong theoretical foundation of cryptographic hash functions.
- “Modern Cryptography: Theory and Practice” by Wenbo Mao – This book presents a robust explanation of the cryptographic systems used today, including SHA-256, with a focus on real-world implementation.
- “Handbook of Applied Cryptography” by Alfred J. Menezes, Paul C. van Oorschot, and Scott A. Vanstone – A comprehensive guide to modern cryptography, including a detailed exploration of hash functions like SHA-256.
Remember, understanding SHA-256 and hash functions thoroughly requires a good grasp of some complex mathematical concepts. These books should provide a strong foundation, but it’s important to approach them with patience and a readiness to delve into the details.