Tag: Cryptography
-

Quantum Threat: Can Quantum Computers Break Bitcoin?
Explore how quantum computing could disrupt Bitcoin by breaking SHA-256 and cracking private keys, and what can be done to prevent this.
-
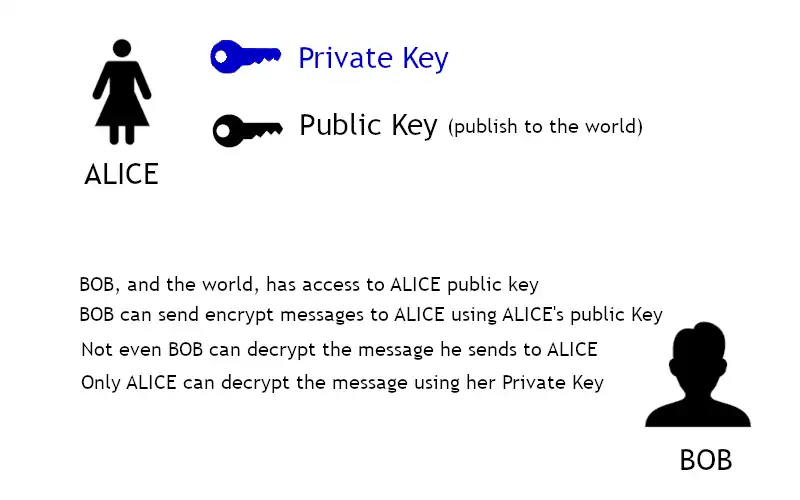
Asymmetric Encryption
Asymmetric encryption requires the use of two keys: a private key that is known only by its owner and a public key that is readily available to those who need to use it.
-

CryptoAPI
CryptoAPI is a core component of the latest versions of Microsoft Windows that provides application programming interfaces (APIs) for cryptographic security services that provide secure channels and code signing for communication between applications.