In an age where the internet has become a backbone of virtually every aspect of our lives, it’s critical to understand the key technologies that drive our communications infrastructure. The realm of voice communication has seen a paradigm shift with the advent of Voice over Internet Protocol (VoIP). This technology, often shrouded in mystery for those not in the know, has significantly altered the way businesses, and indeed individuals, communicate. This article aims to pull back the veil, offering a comprehensive understanding of VoIP, comparing it to traditional cellular technology, and shedding light on potential challenges associated with its use.
In this article:
- What is VoIP?
- How Does VoIP Work?
- What is the Difference between VoIP and a Cellular Phone?
- Benefits and Disadvantages of VoIP
- VoIP Applications and Use Cases
- Conclusion
- Recommended books
- VoIP explained in a video
While cellular technology was the mainstay for a long time, the digital revolution brought along VoIP, quietly infiltrating and subsequently transforming the sphere of communication. Often considered as simply “internet calling,” VoIP is far more nuanced and impactful. But what exactly is VoIP? How does it differ from our age-old friend, the cellular phone? And, crucially, are there any drawbacks we need to be aware of? Buckle up for an enlightening journey into the world of VoIP.

What is VoIP?
VoIP, or Voice over Internet Protocol, is a technology that facilitates the transmission of voice and multimedia content over the Internet. Unlike traditional phone systems that use circuit-switched networks, VoIP transmits voice data via packet-switched networks. In simpler terms, it converts your voice into digital data, sends it over the internet, and reassembles it at the receiving end, all in real-time. This technology isn’t constrained to voice calls alone; it also caters to video calls, multimedia sessions, and even fax transmissions.
The beauty of VoIP lies in its ability to take a traditional service – telephony, strip it of its dependency on dedicated, fixed-line networks, and merge it with the expansive realm of the internet. As a result, VoIP offers a host of benefits such as cost efficiency, flexibility, and integrative capabilities that have made it a preferred choice for individuals and businesses alike. However, it’s not without its set of challenges.
How Does VoIP Work?
Voice over Internet Protocol, or VoIP, is underpinned by a blend of mature and innovative technologies that enable the seamless transmission of voice data over the Internet. At its core, VoIP leverages a concept known as packet-switching. Unlike circuit-switching used in traditional telephony, where a dedicated path is maintained between callers for the entire duration of the call, packet-switching fragments data into packets, each transmitted individually, possibly via different routes, and reassembled at the destination.
The process begins with an Analog-to-Digital Converter (ADC) transforming your voice, an analog signal, into digital data. These digital snippets are then segmented into small packets, each stamped with crucial information such as the destination IP address and packet sequencing details. These packets navigate their way through the vast labyrinth of the Internet, guided by the Internet Protocol. Upon reaching their destination, another critical piece of VoIP technology comes into play, the Digital-to-Analog Converter (DAC), which reassembles the data packets and converts them back into analog sound waves, thereby completing the circle of transmission.
Yet, Voice over IP is not merely a technology of conversion and transmission. It’s an amalgam of protocols and standards working in unison. Session Initiation Protocol (SIP) and Real-Time Transport Protocol (RTP) are two fundamental elements that manage connections and data delivery. SIP controls the communication sessions—be it voice call, video call, or a multimedia conference, while RTP ensures real-time transfer of audio and video.
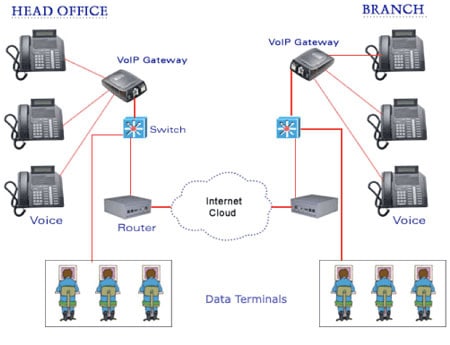
There are primarily three types of VoIP services that users can opt for: ATA (Analog Telephone Adaptor), IP Phones, and Computer-to-Computer. ATA allows you to connect a standard phone to your computer or Internet connection for use with VoIP. IP Phones look just like normal phones but have an Ethernet connector instead of a phone connector. Computer-to-Computer is the easiest method, needing only the software, a microphone, speakers, sound card, and an internet connection.
What is the Difference between VoIP and Cellular Phone?
Drawing the lines of distinction between VoIP and cellular phones is critical in comprehending the strengths and weaknesses of both. Cellular phones, for decades, have been our stalwart companions, providing voice services through a vast network of interconnected cell towers and base stations. The primary basis of cellular communication is circuit-switching, a system in which a dedicated channel is established for the duration of a call.
VoIP, on the other hand, is a product of the digital age. It leverages the power of the Internet to transmit voice data, as explained in the previous chapter. This fundamental difference in data transmission technology results in significant variations in cost, functionality, and quality of service between the two.
From a cost perspective, VoIP often has a clear advantage. While cellular service providers typically charge based on minutes used, VoIP services usually offer unlimited calling for a fixed monthly fee. Also, long-distance or international calls are generally cheaper with VoIP due to the elimination of expensive interconnection fees.

In terms of functionality, VoIP excels with its ability to integrate with other digital services. Features such as voicemail to email transcription, call forwarding, and integration with CRM software are commonplace with VoIP. Cellular phones, while improving with the introduction of smartphones and associated apps, are inherently limited in their ability to offer such integrated digital services.
However, quality of service can be a critical differentiator. Cellular networks, being mature, dedicated voice infrastructures, often deliver superior voice quality and reliability. VoIP, in contrast, is dependent on the quality of your Internet connection. Factors such as bandwidth, latency, and packet loss can negatively impact VoIP call quality.
Finally, it’s worth noting the advent of VoLTE (Voice over LTE), a technology that marries the benefits of VoIP and cellular technology, offering high-quality voice calls over 4G and future 5G networks. This might blur the lines between cellular and VoIP services in the future, bringing together the best of both worlds.
Benefits and Disadvantages of VoIP
Voice over Internet Protocol (VoIP) represents an intriguing fusion of the old and the new – combining the familiarity of voice communication with the groundbreaking power of the Internet. As with any technology, VoIP brings with it a slew of benefits along with its fair share of challenges.
Benefits
Starting with the benefits, the cost efficiency of VoIP stands tall. By leveraging the internet for call transmission, VoIP slashes traditional phone costs – especially for long-distance and international calls. Companies like Skype and Zoom are prime examples. Both offer affordable rates for international calls, far cheaper than conventional telephone networks, saving individuals and businesses a significant amount of money.
The flexibility and mobility that VoIP provides is another undeniable advantage. Unlike traditional phone systems tied to a specific line or number, VoIP allows you to make and receive calls from anywhere with an internet connection. This mobility is beneficial for businesses with remote employees or international clients. A case in point is a digital marketing firm Trello, which leverages VoIP’s flexibility to maintain seamless communication with its distributed workforce.
Moreover, VoIP’s integration with other digital services is a game changer. Features such as voicemail-to-email transcription, auto-attendants, call routing, and CRM integration provide value-added services that transcend traditional telephony. For instance, the sales team of an e-commerce company can use a VoIP system integrated with their CRM to manage customer interactions more efficiently.
Disadvantages
However, despite its advantages, VoIP isn’t devoid of potential challenges. One of the primary disadvantages is its dependence on a stable internet connection. If your internet goes down, so does your VoIP system. For instance, during Hurricane Sandy in 2012, many businesses using VoIP were left without phone service due to internet outages.
Furthermore, VoIP’s call quality can fluctuate depending on your bandwidth and network congestion. High latency or packet loss can lead to jitter or echo, which can diminish the overall call experience. A case in point could be a business conference call ruined by low-quality VoIP connections, causing disruptions and inefficiencies.
Lastly, emergency calls can be an issue with Voice over IP. Traditional phone services have a fixed location, making it easier for emergency services to locate callers. With VoIP, providing your precise location can be tricky, as the call can be made from anywhere with an internet connection. This issue was highlighted when a VoIP user couldn’t relay their exact location during an emergency call, making it difficult for help to arrive promptly.
In conclusion, while VoIP provides numerous benefits that can revolutionize personal and business communication, it is crucial to be aware of potential downsides and make an informed decision based on individual needs and circumstances.
VoIP Applications and Use Cases
The transformative power of VoIP has given birth to a wide array of applications and use cases, ranging from personal communication to complex business solutions. Central to this are various Voice over IP services that have become household names.
Skype, one of the pioneers in the VoIP space, offers voice, video, and messaging services, enabling people to stay connected irrespective of geographical boundaries. It’s become an indispensable tool for long-distance family conversations, job interviews, and virtual meetings.
Zoom, initially popular in the corporate world, became a ubiquitous tool during the COVID-19 pandemic. Leveraging VoIP, it has enabled virtual classrooms, corporate meetings, and even social gatherings, maintaining human connection during challenging times.

For businesses, services like RingCentral and Vonage provide comprehensive VoIP solutions. These platforms offer an array of features such as auto-attendant, call recording, CRM integrations, analytics, and more, revolutionizing business telecommunication.
Looking towards the future, VoIP is set to ride the wave of technological advancements. One major trend is the integration of AI and machine learning with Voice over IP. This could lead to smarter call routing, voice recognition, and automated customer service, further enhancing efficiency and user experience.
The rise of 5G technology will also have a profound impact on VoIP. The increased bandwidth and lower latency of 5G will drastically improve call quality and enable more data-intensive applications, like augmented and virtual reality conferencing.
Conclusion
In this digital era where technology is ceaselessly evolving, VoIP has stood its ground as a key player in revolutionizing communication. We have dissected the core of Voice over IP, compared it with traditional cellular phones, and delved into its pros and cons. Understanding VoIP is like fitting pieces of a complex puzzle together, from appreciating its working mechanism to being aware of its challenges, and exploring its myriad applications.
VoIP, being the blend of cost efficiency, flexibility, and integrative capabilities, has carved a niche for itself in the world of telecommunication. Yet, like any technology, it’s not a one-size-fits-all solution. It’s important to keep in mind the potential drawbacks, like dependence on a stable internet connection, fluctuating call quality, and challenges with emergency calls.
The journey of unraveling VoIP doesn’t end here. The rise of AI, machine learning, and 5G are set to shape its future, promising an exciting roadmap ahead. As we continue to innovate and redefine the boundaries of communication, Voice over Internet Protocol stands as a testament to human ingenuity and the power of the Internet.
List of Recommended books
For those keen on deepening their understanding of VoIP and its broader implications, here’s a list of recommended books:
- “VoIP For Dummies” by Timothy V. Kelly
- “VoIP Technologies: A Comprehensive Guide to Voice over Internet Protocol (VoIP)” by Uyless Black
- “VoIP: Internet Linking for Radio Amateurs” by Jonathan Taylor
- “Switching to VoIP: A Solutions Manual for Network Professionals” by Theodore Wallingford
- “VoIP Hacks: Tips & Tools for Internet Telephony” by Ted Wallingford
- “Packet Guide to Voice over IP: A System Administrator’s Guide to VoIP Technologies” by Bruce Hartpence.
Previous Article
Our article about Voice over Internet Protocol has been completely rewritten and updated. However, for consultation and reference purposes, we have decided to keep the original text here.
What is Voice over IP (VoIP)?
Voice Over IP, or VoIP, is an umbrella term for a set of technologies that allow voice traffic to be carried over Internet Protocol (IP) internetworks such as the Internet.
The term “Voice over IP” was coined by the VoIP Forum, a consortium of companies dedicated to the development and extension of IP telephony technologies. Voice over IP (VoIP) is the prime example of “convergence” in the networking and telecommunications industry because it enables telephony and computer networking traffic to be combined into a single data stream of IP packets.
Various vendors have offered proprietary VoIP solutions, but most have recently moved toward standards-based solutions that implement the H.323 and T.120 communication protocols developed by the International Telecommunication Union (ITU). These include voice-encoding industry standards such as G.723 and G.729. One goal of these standards is to enable integration between IP telephony and global cellular telephony standards such as the Global System for Mobile Communications (GSM). However, the move toward standards has been slow, and only a few vendors offer end-to-end carrier-class VoIP services with acceptable levels of communication latency.
Vendors tout the following advantages of using VoIP technologies:
- Lower long-distance costs: VoIP enables users to avoid long-distance charges by placing local calls to their Internet service provider (ISP) and having the encapsulated voice traffic move free of charge over the Internet. The problem with this approach is that transmission over the Internet is unpredictable and often has unacceptable levels of latency. One solution is for vendors to construct their own private IP internetworks for VoIP services, but this is an expensive prospect even for the largest carriers and has contributed to the slow progress in voice/data convergence. Some companies offer their own VoIP services to employees using the internal company network, but this approach is still costly and requires expertise to maintain.
- New solutions for remote access by mobile users: VoIP solutions allow users to communicate with remote stations using both voice and data integrated into a single IP data stream. For example, a user can browse a Web site and talk to customer support at the site simultaneously by using a single modem connection.
Advantages of VoIP?
Some VoIP services offer features and services that are not available with a traditional phone, or are available but only for an additional fee. You may also be able to avoid paying for both a broadband connection and a traditional telephone line.
Disadvantages of VoIP?
If you’re considering replacing your traditional telephone service with VoIP, there are some possible differences:
- Some VoIP services don’t work during power outages and the service provider may not offer backup power.
- Not all VoIP services connect directly to emergency services through 9-1-1. For additional information, see VoIP & 911 Advisory.
- VoIP providers may or may not offer directory assistance/white page listings.