The Editorial Team is a collective of technology enthusiasts, computer network engineers, and industry professionals dedicated to creating meticulously curated content for a diverse readership. With a combined experience spanning several decades, our team distills complex technology topics into clear, informative articles. Whether it’s networking fundamentals, cutting-edge AI insights, or in-depth guides on blockchain technology, the Editorial Team strives to provide reliable information that advances the understanding of technology for everyone from students to seasoned professionals.

Editorial Team’s mission
The Editorial Team’s mission extends beyond mere reporting; we aim to be the architects of understanding, constructing bridges over the rivers of jargon and complexity. From the foundational bricks of networking to the ever-evolving skies of cloud computing, we guide you through the technological labyrinth.
We take pride in our meticulous attention to detail and our unwavering commitment to accuracy, ensuring that each piece of information is a thread in the vast tapestry of technological knowledge. As we chart the course through the evolving landscape of technology, we invite our readers to join us on this exhilarating journey of discovery and growth. Together, we not only explore the current terrain of technology but also anticipate the horizons of tomorrow’s innovations.
Our Latest Articles
-
What “Scalability” Really Means in Computer Networking
Scalability is often treated as a buzzword in networking, but it is a deeply technical concept that determines whether a system can grow efficiently. This article explains what scalability really means in computer networks, the challenges it introduces, and the design principles that make large-scale networks like the Internet possible.
-
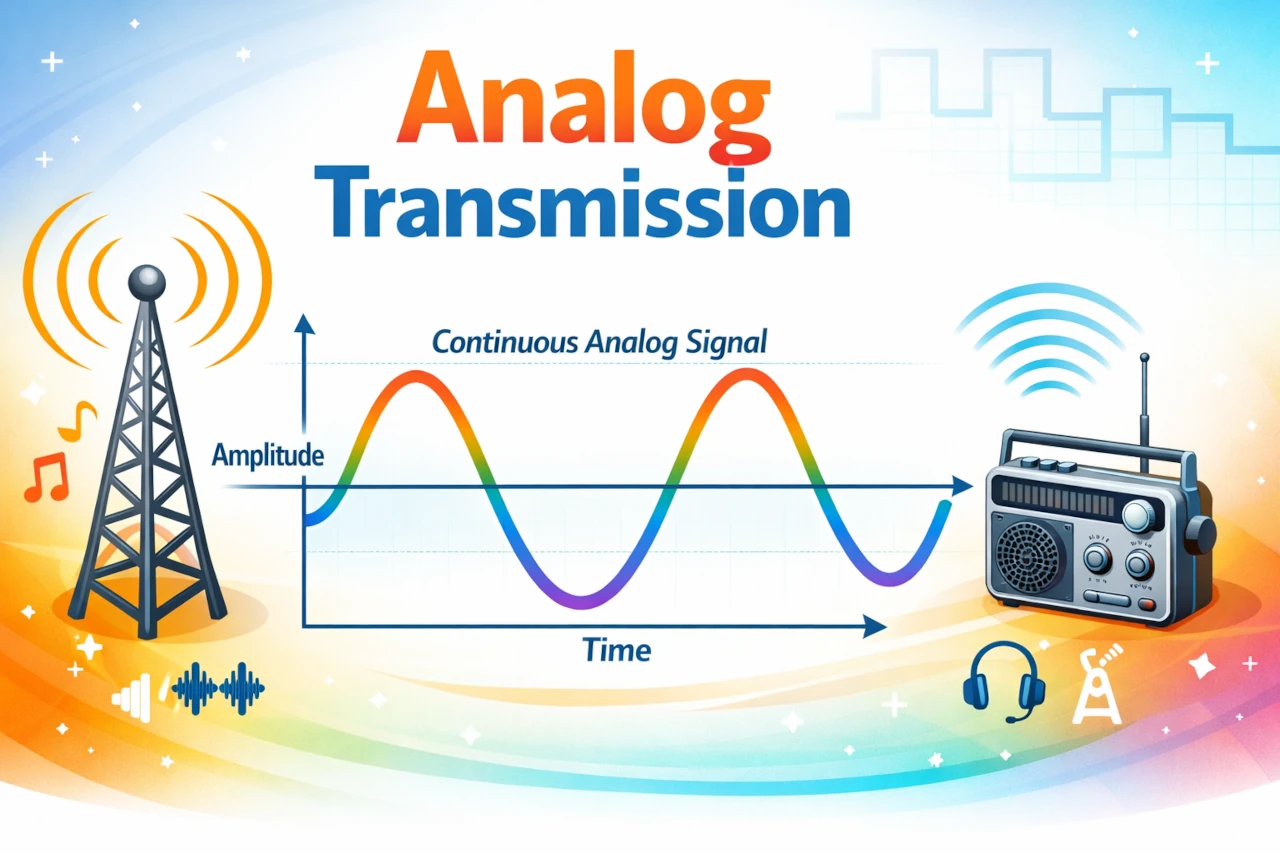
Analog Transmission
Imagine you are trying to tell a friend a secret by whispering across a crowded room. Your voice rises and falls, gets louder and softer, stretches and compresses in time. The sound waves leaving your mouth are continuously varying shapes traveling through the air.
-

Encapsulation in Computer Networks Explained Step by Step (With Real Packet Examples)
Learn encapsulation in computer networks step by step. See how an HTTP message is wrapped by TCP, then IP, then Ethernet—using real packet examples and headers.
-
Recurrent Neural Networks and the Secrets of Sequence Learning
Discover how Recurrent Neural Networks process sequences over time, enabling AI systems to understand language, forecast trends, and tackle problems where order and memory truly matter.
-

Mastering Internet Routing with BIRD: A Step-by-Step Guide to Building Your Own Routing System
Want to learn how to master routing in modern networks? Our comprehensive guide to BIRD, the Bird Internet Routing Daemon, walks you through everything from installation to real-world deployment of BGP and OSPF configurations. Get step-by-step instructions, troubleshooting tips, and practical use cases that will help you build your own routing system.
-
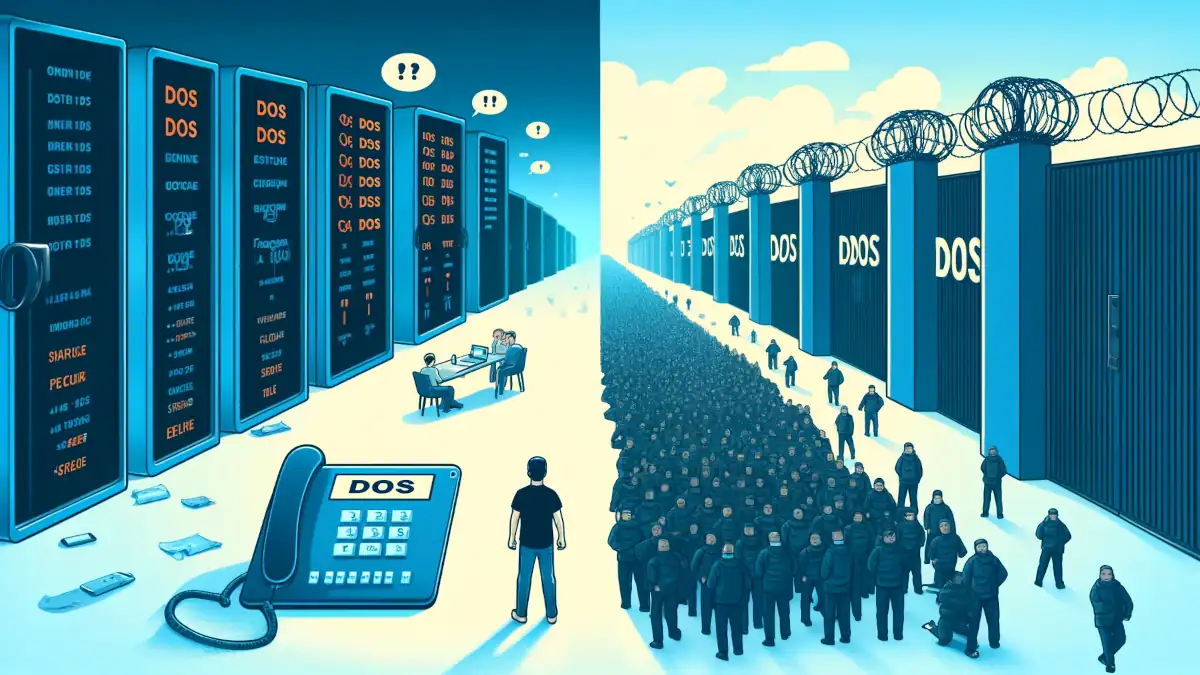
DDoS Attacks and difference from DoS
Let’s delve into the world of cybersecurity, specifically focusing on two prevalent threats: Denial of Service (DoS) and Distributed Denial of Service (DDoS) attacks.
-

Introduction to the Sandbox: Your Digital Playground
Dive into the digital playground of sandboxes where safety and innovation play nice together. Explore how sandboxes create secure environments for testing and development, their various types, and their pivotal role in enhancing security across technologies. Discover the future trends of sandboxing in this comprehensive guide.
-

Understanding Dynamic Adaptive Streaming over HTTP (DASH)
Explore the essentials of Dynamic Adaptive Streaming over HTTP (DASH), the technology revolutionizing media delivery online.
-

Unpacking the Core: The Principles of Zero Trust Security
Through a detailed exploration of its foundational principles, we will uncover how Zero Trust operates not just as a technology, but as a comprehensive strategy reshaping security frameworks across industries.
-
Assembly Language: Low-Level Programming
Assembly language is a low-level programming language that provides a unique perspective on computer operations, sitting just above machine code in complexity.
-

Neural Computation: Unlocking the Brain’s Algorithms
Explore how neural computation merges brain science and AI to create smarter technologies. Dive into the future of computing!
-

The Intriguing World of Denial of Service (DoS) Attacks
Dive into the intriguing world of Denial of Service (DoS) attacks. Learn what they are, explore their history, understand their mechanics, and discover robust defense strategies.