Category: Network Security
-
DDoS Attacks and difference from DoS
Let’s delve into the world of cybersecurity, specifically focusing on two prevalent threats: Denial of Service (DoS) and Distributed Denial of Service (DDoS) attacks.
-

Unpacking the Core: The Principles of Zero Trust Security
Through a detailed exploration of its foundational principles, we will uncover how Zero Trust operates not just as a technology, but as a comprehensive strategy reshaping security frameworks across industries.
-

Quantum Threat: Can Quantum Computers Break Bitcoin?
Explore how quantum computing could disrupt Bitcoin by breaking SHA-256 and cracking private keys, and what can be done to prevent this.
-
The 2016 Dyn Cyberattack: An Overview
On October 21, 2016, the internet infrastructure company Dyn, which controls much of the DNS infrastructure used by major websites, was hit by a series of distributed denial-of-service (DDoS) attacks.
-

The Intriguing World of Denial of Service (DoS) Attacks
Dive into the intriguing world of Denial of Service (DoS) attacks. Learn what they are, explore their history, understand their mechanics, and discover robust defense strategies.
-
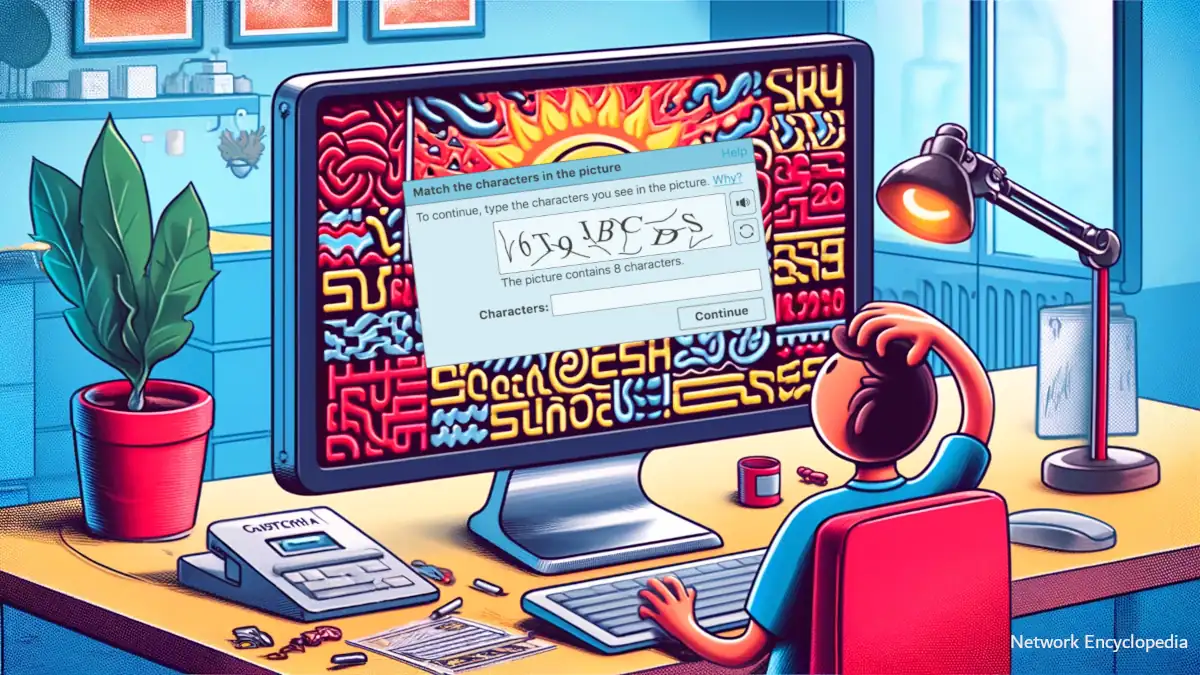
Unraveling CAPTCHA: The Gatekeeper of Modern Websites
CAPTCHA (Completely Automated Public Turing test to tell Computers and Humans Apart) is designed to prevent automated software from performing actions that could potentially harm websites, ensuring that only humans can access certain functionalities.
-

Decoding EAP Protocol: A Guide to Extensible Authentication
The Extensible Authentication Protocol (EAP) is a network authentication framework used to control access to both wired and wireless networks.
-

Common Criteria for Information Technology Security Evaluation (CC): Certifying Computer Security
In this article, we will delve into the significance of the Common Criteria, its global adoption, and the entities that rely on it for securing their digital assets. Additionally, we will touch upon its historical predecessor, the C2 security standard, to highlight the evolution of security evaluations in the IT realm.
-

SPF Records: Ensuring Your Emails Land Where They Should
Discover how to craft, validate, and implement SPF records to protect your domain, prevent email spoofing, and ensure your messages reach their intended destinations. With practical insights and expert advice, this article is an indispensable resource for anyone looking to bolster their email security and deliverability.
-
Brute-Force Attack
Learn what a brute-force attack is, real-world examples, and foolproof strategies to protect yourself. Your ultimate guide to understanding and combating this pervasive cyber threat.

