Our Latest Articles
-

Submarine Communication Cables: Secrets of the Ocean Depths
Join us as we dive deeper into the dynamic saga of submarine communication cables, exploring their pivotal role in our interconnected era and the continuous efforts to safeguard this hidden infrastructure.
-
Assembly Language: Low-Level Programming
Assembly language is a low-level programming language that provides a unique perspective on computer operations, sitting just above machine code in complexity.
-

Neural Computation: Unlocking the Brain’s Algorithms
Explore how neural computation merges brain science and AI to create smarter technologies. Dive into the future of computing!
-

The Intriguing World of Denial of Service (DoS) Attacks
Dive into the intriguing world of Denial of Service (DoS) attacks. Learn what they are, explore their history, understand their mechanics, and discover robust defense strategies.
-
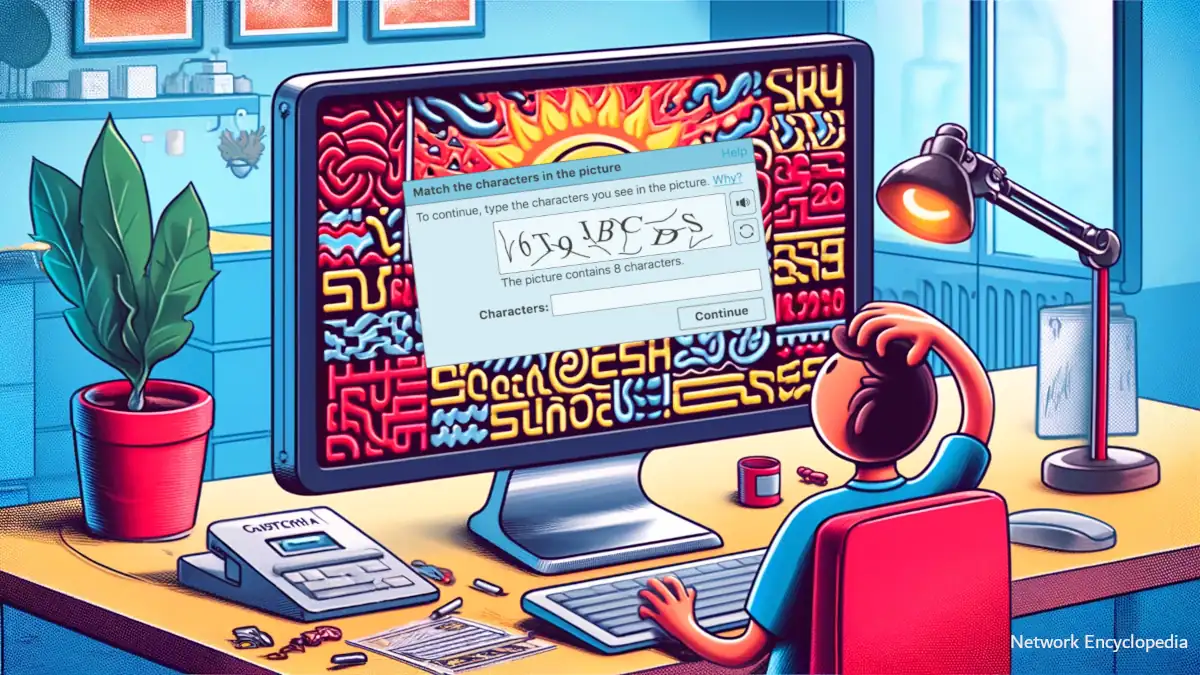
Unraveling CAPTCHA: The Gatekeeper of Modern Websites
CAPTCHA (Completely Automated Public Turing test to tell Computers and Humans Apart) is designed to prevent automated software from performing actions that could potentially harm websites, ensuring that only humans can access certain functionalities.
-

Mastering the Paxos Algorithm: How Consensus Plays with AI
Welcome to a journey through the cerebral circuits of computer science where we demystify the legendary Paxos Algorithm.
-

Exploring Light Emitting Diodes (LEDs) in Modern Displays
Light Emitting Diodes (LEDs) are more than just indicators on your gadgets; they are at the heart of a lighting revolution that spans across numerous technologies.
-

The Y2K Bug: A Midnight Race Against Time
As the 20th century drew to a close, a digital doomsday loomed. Dubbed the Y2K bug, this technological quirk threatened to throw global systems into chaos at the stroke of midnight, January 1, 2000.
-

Decoding AI’s Problem-Solving Capability: A Comprehensive Guide
What exactly is problem-solving in the context of AI, and how does it work? Our exploration delves into the mechanisms AI uses to tackle problems, from simple puzzles to complex, real-world challenges.
-
High-Performance Routing (HPR): Revolutionizing Network Communication
Conceived to address the growing demands for efficiency and reliability in network communication, HPR marks a significant departure from traditional routing methodologies.
-

Understanding XID Response Frames in Networking
Discover what XID Response Frames are in networking, their role in communication protocols, and how they optimize data transmission. An authoritative guide for tech enthusiasts.
-
Precision Time Protocol (PTP): An Overview
Precision Time Protocol (PTP), defined in the IEEE 1588 standard, offers a solution for precisely synchronizing clocks throughout a computer network.