Category: A to Z
-
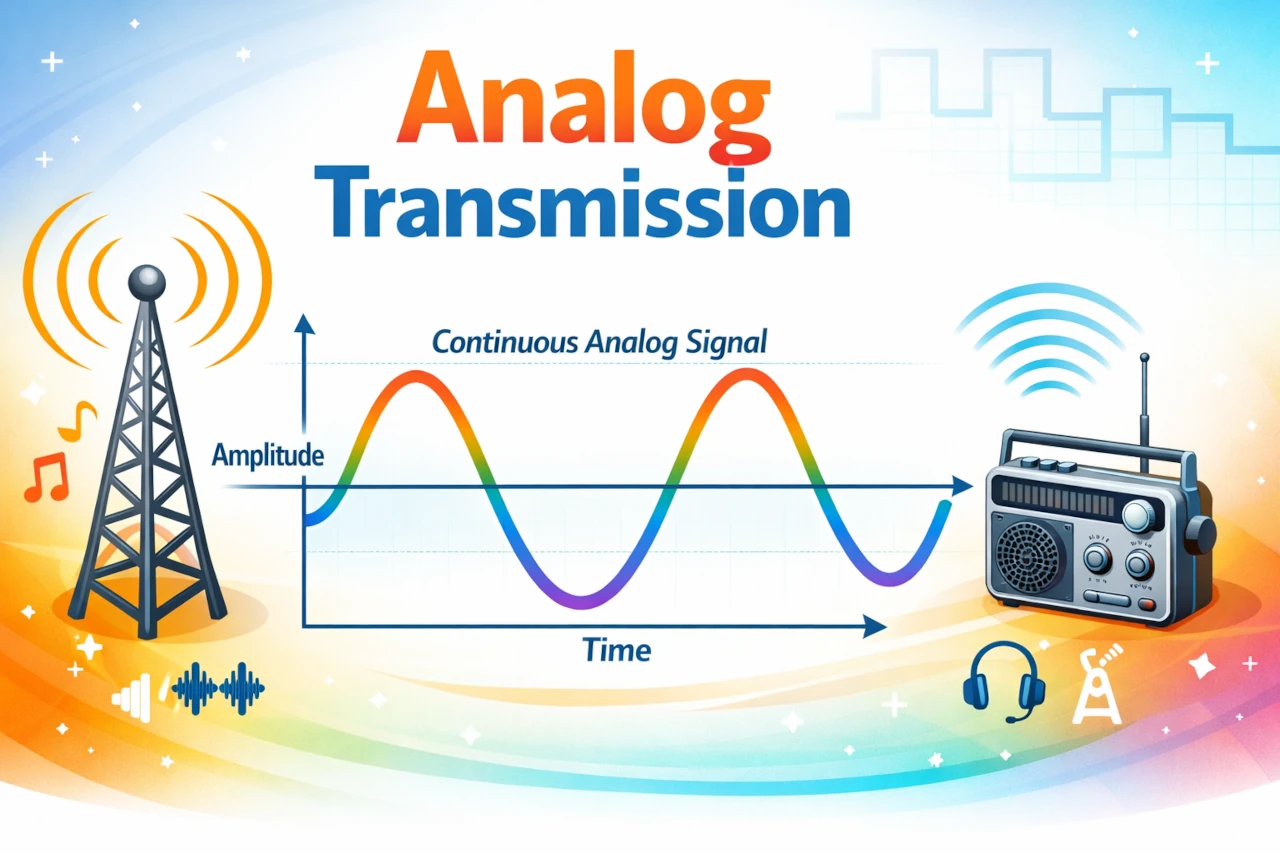
Analog Transmission
Imagine you are trying to tell a friend a secret by whispering across a crowded room. Your voice rises and falls, gets louder and softer, stretches and compresses in time. The sound waves leaving your mouth are continuously varying shapes traveling through the air.
-

Encapsulation in Computer Networks Explained Step by Step (With Real Packet Examples)
Learn encapsulation in computer networks step by step. See how an HTTP message is wrapped by TCP, then IP, then Ethernet—using real packet examples and headers.
-
Recurrent Neural Networks and the Secrets of Sequence Learning
Discover how Recurrent Neural Networks process sequences over time, enabling AI systems to understand language, forecast trends, and tackle problems where order and memory truly matter.
-
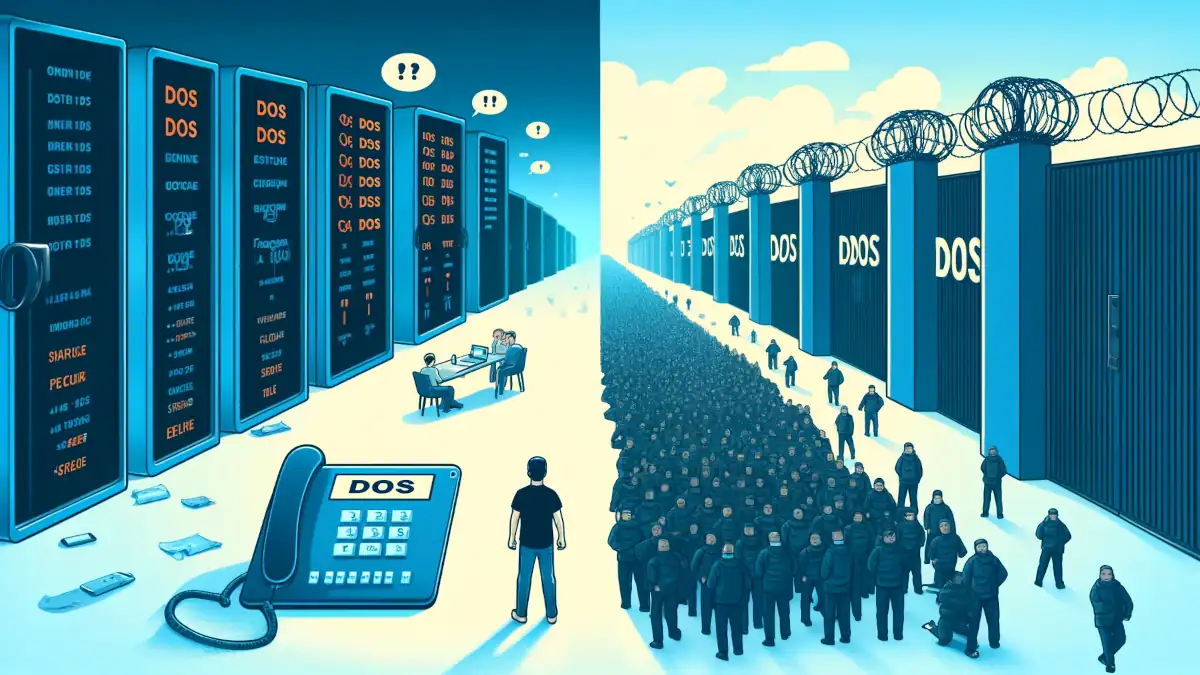
DDoS Attacks and difference from DoS
Let’s delve into the world of cybersecurity, specifically focusing on two prevalent threats: Denial of Service (DoS) and Distributed Denial of Service (DDoS) attacks.
-

Unraveling LTE: Your Ticket to High-Speed Mobile Communication
In this article, we’ll embark on a journey through the world of LTE. We’ll decode how it works, why it’s a game-changer in mobile communications, and how it manages to deliver that crisp, clear video call quality even as you roam around.
-
Booting Up: The Magic of Preboot eXecution Environment (PXE)
This article will demystify how PXE enables a computer to start up or “boot” from a network before its main operating system begins to run.
-

Coding Standards: A Symphony of Syntax
In this article, we’ll dissect these standards piece by piece, not only to understand what they are but also to learn how to effectively teach them to the next generation of web maestros – our junior web developers.
-

Introduction to the Sandbox: Your Digital Playground
Dive into the digital playground of sandboxes where safety and innovation play nice together. Explore how sandboxes create secure environments for testing and development, their various types, and their pivotal role in enhancing security across technologies. Discover the future trends of sandboxing in this comprehensive guide.
-

Zigbee: The Unsung Hero of Smart Devices
This article will delve into the nuts and bolts of the Zigbee protocol, decoding its magic and how it powers the hidden conversations of our smart homes. From its architecture to its real-world applications, prepare to uncover the invisible network that could be inside your very own living room.
-

AAA Protocol: Your Gateway to Secure Network Access
Dive into the world of AAA Protocol, where network security meets ease of access. Discover how Authentication, Authorization, and Accounting work to keep your network secure.
-
Software 2.0: The Evolution of Coding as We Know It
In this article, we’ll dive deep into the intricacies of Software 2.0, exploring how it’s reshaping the landscape of technology by automating the decision-making processes in software applications.
