An Access Control List (ACL), is any mechanism for implementing access control on an operating system, file system, directory service, or other software. Access control lists (ACLs) are implemented into the basic operating system architecture of Microsoft’s Windows operating system platforms and are used to control access to objects in Active Directory and files on NTFS volumes.
An access control list is basically a list attached to an object specifying which security principals (users, groups, computers, and so on) are allowed to access the object and what level of access they are allowed to have. In Windows 2000, ACLs are more properly called discretionary access control lists (DACLs) because they can be configured and managed by administrators at their discretion.
There is also another type of ACL in Windows called a system access control list (SACL), which is used to control the generation of audit messages when object auditing has been configured on a file system.
System Access Control List (SACL)
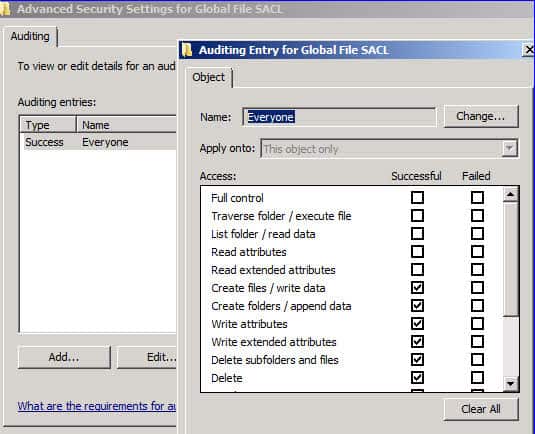
A system access control list (SACL) enables administrators to log attempts to access a secured object. Each ACE specifies the types of access attempts by a specified trustee that cause the system to generate a record in the security event log. An ACE in a SACL can generate audit records when an access attempt fails, when it succeeds, or both. For more information about SACLs, see Audit Generation and SACL Access Right.
Access control lists are natively implemented on some UNIX operating system platforms such as Solaris (which first implemented ACLs in version 2.5.1) and are also available as third-party software for other UNIX platforms.
Traditionally access control on UNIX file systems was managed using the chmod (change mode) command, but this offered only limited or coarse-grained control of file permissions and provided no flexibility for configuring unique sets of access permissions for particular users or groups.
To set and display access control lists on Solaris, use the setfacl and getfacl commands. Other UNIX packages and add-ons may use different commands such as setacl and getacl.