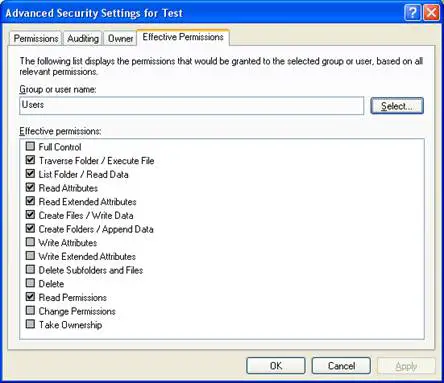
Effective Permissions is the cumulative permissions a user has for accessing a resource based on his or her individual permissions, group permissions, and group membership.
What are Effective Permissions?
Effective Permissions, in Microsoft Windows family, is the cumulative permissions a user has for accessing a resource based on his or her individual permissions, group permissions, and group membership. The effective permissions a user experiences trying to access a file or folder depend on the various permissions granted to the user expressly or by virtue of their membership in a particular group. When a permissions conflict exists between one group and another, or between the user and a group, rules are applied that resolve the issue.
How Effective Permissions work?
In networks based on Windows NT or Windows 2000, calculation of effective permissions can be determined using three simple rules:
First, if a user belongs to two (or more) groups, and these two groups have different NTFS standard file permissions on a given file, the user’s ability to access the file both locally and over the network is determined as follows:
- The effective NTFS permission is the least restrictive (most permissive) NTFS standard permission. For example,read (NTFS) + change (NTFS) = change (NTFS)
- The exception to this is that the no-access permission overrides all other permissions. For example,read (NTFS) + no access (NTFS) = no access (NTFS)
Second, if a user belongs to two (or more) groups, and these two groups have different shared folder permissions on a given shared folder, the user’s ability to access the shared folder over the network is determined as follows:
- The effective shared folder permission is the least restrictive (most permissive) shared folder permission. For example,read (shared folder) + change (shared folder) = change (shared folder)
- The exception to this is that the no-access permission overrides all other permissions. For example,read (shared folder) + no access (shared folder) = no access (shared folder)
Third, when a user attempts to access a folder or file over a network that has both NTFS permissions (the first example) and shared folder permissions (the second example) configured on it, the effective permission is the most restrictive (least permissive) permission. For example,
read (NTFS) + change (shared folder) = read (combined)