Batch commands, a fundamental component of the Windows operating system, allow users and administrators to automate tasks and efficiently manage system operations. Originating from the DOS-based systems, batch files and commands have evolved to become powerful tools in modern Windows environments.
This article provides a deep dive into batch commands, covering their basics, functionalities, and advanced applications, particularly focusing on the latest Windows versions.
In this article:
- Understanding Batch Commands
- Implementing Batch Commands in Windows
- Batch Commands in Modern Windows Systems
- Challenges and Best Practices
- Advanced Batch Scripting Techniques
- Real-World Applications and Case Studies
- Conclusion
1. Understanding Batch Commands
Batch commands are text-based scripts written in a sequence, typically saved with a .bat or .cmd file extension. When executed, these scripts run a series of commands automatically. They are essentially a set of instructions to the system to perform various tasks without user intervention.
- Basics of Batch Files: A batch file is a plain text file that contains a sequence of commands for the system to execute. These files can be created using any text editor and are executed through the Command Prompt in Windows.
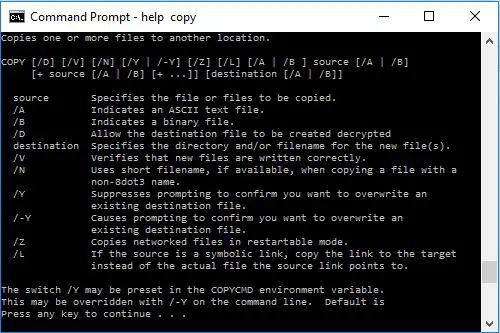
- Command Syntax and Structure: Batch commands follow a specific syntax and structure. They can include built-in system commands, loops, conditional statements, and can even call other batch files or executable programs.
Batch File Commands
| Command | Description |
| call | Calls one batch program from another while allowing the calling program to continue running |
| echo | Toggles command-echoing on or off |
| endlocal | Restores environment variables set by a setlocal command |
| for | Used to run a specified command for each file in a set of files |
| goto | Jumps to a specific line that is labeled in a batch file |
| if | Used to perform conditional processing of commands |
| pause | Suspends processing of the batch file and waits for the user to respond |
| rem | Used to insert remarks (comments) in a batch file for documentation purposes |
| setlocal | Initiates localization of environment variables in a batch file |
| shift | Used to change the position of replaceable parameters in a batch file |
2. Implementing Batch Commands in Windows
Batch commands are versatile and can be used for a wide range of tasks in Windows like:
- Automating Routine Tasks: Tasks like file backups, system cleanups, and software installations can be automated using batch files, saving time and reducing the possibility of human error.
- System Management and Configuration: Batch commands can configure system settings, manage user accounts, and control network configurations.
- Advanced Scripting: With the incorporation of advanced scripting elements like variables, loops, and conditional logic, batch files can handle complex operations and decision-making processes.
Automating Routine Tasks
- File Management: Batch commands can automate the process of copying, moving, renaming, or deleting files. For instance, a batch script could be scheduled to clean up temporary files or back up critical data to a different directory or drive.
- System Maintenance: Tasks such as disk defragmentation, checking disk health, or clearing system caches can be automated using batch files. This ensures regular maintenance without manual intervention, keeping the system efficient.
- Software Installation and Updates: Batch files can streamline the process of installing or updating software across multiple systems, especially in an organization, by executing a sequence of installation steps automatically.
System Management and Configuration
- Network Settings: Administrators can use batch scripts to configure network settings, such as setting up IP addresses, modifying DNS settings, or mapping network drives, especially in environments with multiple computers.
- User Account Management: Creating, modifying, or deleting user accounts can be automated with batch commands. This is particularly useful in large organizations with frequent changes in personnel.
- Service Management: Starting, stopping, or restarting system services can be handled through batch files. This is often used in server maintenance and application deployment scenarios.
3. Batch Commands in Modern Windows Systems
In recent versions of Windows, batch commands continue to be relevant for compatibility with new Windows features and interacting with Windows services.
Compatibility with New Windows Features
- Integration with Advanced Windows Tools: Modern versions of Windows support enhanced batch scripting that can invoke tools like Task Scheduler, Windows Management Instrumentation (WMI), and even PowerShell scripts, offering a broader range of functionalities.
- Interfacing with Windows API: Advanced batch scripts can interface with Windows API, allowing scripts to perform tasks that were traditionally possible only with more complex programming languages.
Interacting with Windows Services
- Automation of Background Processes: Batch commands can be used to automate the management of background processes and services, such as scheduling a service to restart at a specific time or in response to certain events.
- Troubleshooting and Logs: Batch scripts can also be designed to gather system logs or run diagnostics, aiding in troubleshooting common Windows issues.
Enhanced Scripting Capabilities
- Looping and Conditional Logic: The latest versions of Windows support more complex batch file constructions, such as loops and conditional statements, allowing for more sophisticated and flexible scripts.
- User Interaction: Modern batch scripts can include user prompts, decision-making logic based on user input, and interactive menus, making them more dynamic and user-friendly.
In conclusion, batch commands in Windows have evolved significantly, offering a range of functionalities that extend beyond basic task automation. Their integration with modern Windows features and services makes them a powerful tool for system administrators and users alike, capable of handling complex automation and system management tasks with ease.
4. Challenges and Best Practices
While batch files are powerful, they come with their own set of challenges:
- Security Concerns: Improperly written batch files can pose security risks. It’s crucial to write secure scripts and avoid executing batch files from unknown sources.
- Debugging and Error Handling: Efficient error handling and debugging mechanisms should be in place to ensure the smooth execution of batch files.
5. Advanced Batch Scripting Techniques
- Using Batch Scripts with PowerShell: Combining batch scripts with PowerShell commands opens up a broader range of possibilities, allowing more complex and powerful automation.
- Networking and Remote Execution: Batch files can be used to execute tasks on remote systems, making them valuable in network administration.
6. Real-World Applications and Case Studies
Application in Large-Scale System Deployments
- Enterprise IT Management: In enterprise environments, batch scripts are crucial for deploying software and configurations across numerous workstations. For instance, a company could automate the rollout of a security patch to all its computers overnight using a batch script.
- Automating Server Setup: Server administrators use batch files to automate the setup of new servers, including configuring roles, installing features, and setting up network parameters. This streamlines the process of scaling infrastructure.
Automation in Software Development and Testing
- Build Automation: Software development teams often use batch scripts to automate their build processes. These scripts compile code, run tests, and package the software for deployment, ensuring consistency and efficiency.
- Automated Testing: Batch files can automate the execution of a suite of tests, reporting results back to developers. This is particularly useful in continuous integration and deployment (CI/CD) pipelines.
Network Management and Maintenance
- Routine Network Tasks: Network administrators use batch scripts to automate routine tasks like resetting network connections, renewing IP addresses, and monitoring network traffic.
- Disaster Recovery: Batch files play a crucial role in disaster recovery processes, where they can be used to automate data backup and restoration processes.
Case Studies
- Retail Chain Network Upgrade: A retail chain implemented a series of batch scripts to upgrade network configurations across their nationwide stores. The scripts were designed to execute after hours, minimizing disruption and ensuring uniformity in network settings.
- Automated Data Management for a Healthcare Provider: A healthcare provider utilized batch scripts to automate the transfer and backup of patient data across multiple databases. This ensured data redundancy and compliance with healthcare data regulations.
- Software Deployment in an Educational Institution: A university used batch files to deploy educational software across its computer labs. The scripts handled software installation, configuration, and user access settings, significantly reducing the manual workload of the IT staff.
In summary, batch commands find a wide range of applications in real-world scenarios, from automating routine tasks in network management to playing crucial roles in large-scale system deployments and software development processes. These case studies demonstrate the versatility and effectiveness of batch commands in diverse operational environments.
7. Conclusion
Batch commands remain a vital tool in the Windows ecosystem, offering simplicity and power for a wide range of tasks. Their ability to automate routine operations, manage system settings, and execute complex scripts makes them invaluable in both personal and professional computing environments.