Category: Network Protocols
-

Mastering Internet Routing with BIRD: A Step-by-Step Guide to Building Your Own Routing System
Want to learn how to master routing in modern networks? Our comprehensive guide to BIRD, the Bird Internet Routing Daemon, walks you through everything from installation to real-world deployment of BGP and OSPF configurations. Get step-by-step instructions, troubleshooting tips, and practical use cases that will help you build your own routing system.
-

Zigbee: The Unsung Hero of Smart Devices
This article will delve into the nuts and bolts of the Zigbee protocol, decoding its magic and how it powers the hidden conversations of our smart homes. From its architecture to its real-world applications, prepare to uncover the invisible network that could be inside your very own living room.
-

AAA Protocol: Your Gateway to Secure Network Access
Dive into the world of AAA Protocol, where network security meets ease of access. Discover how Authentication, Authorization, and Accounting work to keep your network secure.
-

Understanding Dynamic Adaptive Streaming over HTTP (DASH)
Explore the essentials of Dynamic Adaptive Streaming over HTTP (DASH), the technology revolutionizing media delivery online.
-
High-Performance Routing (HPR): Revolutionizing Network Communication
Conceived to address the growing demands for efficiency and reliability in network communication, HPR marks a significant departure from traditional routing methodologies.
-
Precision Time Protocol (PTP): An Overview
Precision Time Protocol (PTP), defined in the IEEE 1588 standard, offers a solution for precisely synchronizing clocks throughout a computer network.
-

Decoding EAP Protocol: A Guide to Extensible Authentication
The Extensible Authentication Protocol (EAP) is a network authentication framework used to control access to both wired and wireless networks.
-
Exploring the Session Layer in the OSI Model
Delve into the Session Layer of the OSI Model: understand its functions, protocols, and impact on network communication in this detailed exploration.
-
MAC Layer: The Backbone of Network Communication
Unravel the complexities of the Medium Access Control Layer in network communication, its functionalities, and its pivotal role in the OSI model.
-

Mastering Network Time Protocol (NTP): A Comprehensive Guide
Dive deep into the Network Time Protocol (NTP) to understand its intricacies, applications, and importance in synchronized computing.
-

Unraveling the Threads of RTSP: The Pulse of Live Streaming
Decode the magic behind live streaming with RTSP! Explore the core of real-time multimedia transmission with our in-depth guide.
-
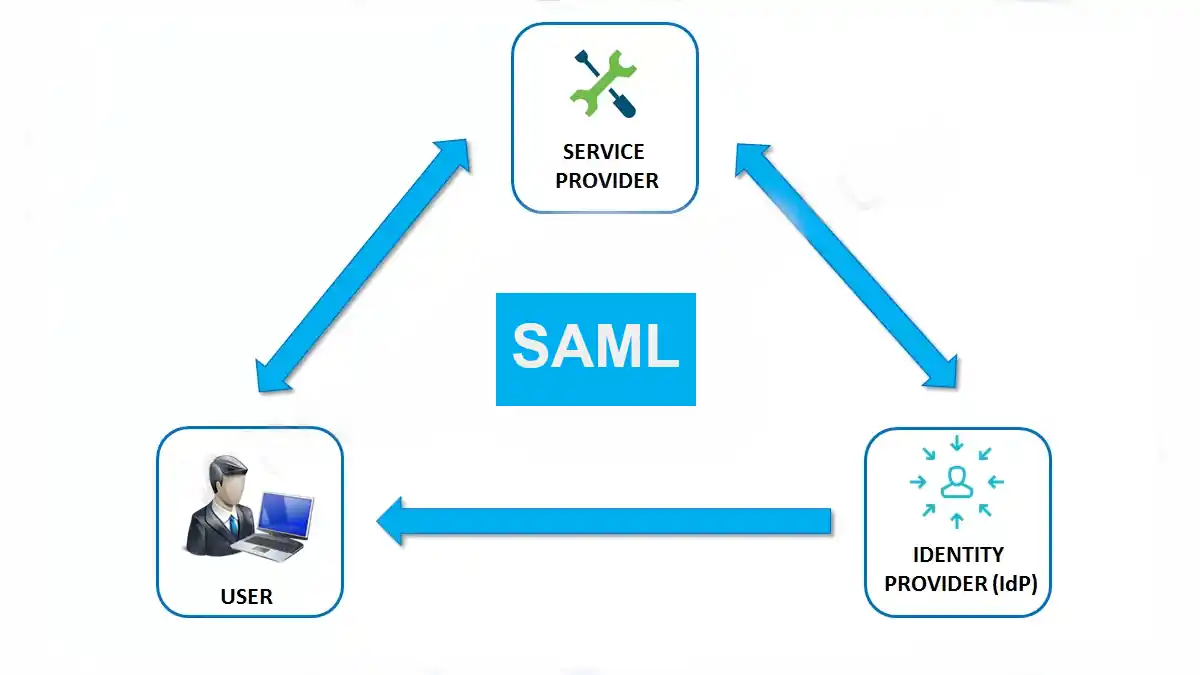
Security Assertion Markup Language (SAML)
It’s time to talk about Security Assertion Markup Language (SAML). Welcome to the exciting realm of network security and access management!