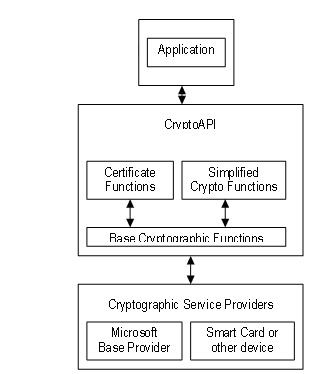
CryptoAPI (Cryptographic Application Programming Interface) is a legacy cryptographic framework provided by Microsoft for applications running on Windows operating systems. It serves as a set of functions and services that allow developers to incorporate cryptographic features, such as encryption, decryption, digital signatures, and certificate management, into their software applications.
In this article:
CryptoAPI was widely used in earlier versions of Windows but has been largely replaced by the more modern Cryptography Next Generation (CNG) framework in recent Windows versions. It provided essential cryptographic functionality to secure data and communications within Windows applications, making it a crucial component for developers working on security-related tasks.

1. CryptoAPI in Windows
CryptoAPI, also known as Cryptographic API, was introduced by Microsoft in the early versions of Windows. It served as a programming interface that allowed developers to integrate cryptographic functions and services into their applications. CryptoAPI provided a set of functions and Win32 libraries to perform various cryptographic operations, including encryption, decryption, digital signatures, and certificate management. This allowed developers to build secure applications that could protect sensitive data and communications.
CryptoAPI was present in several versions of Windows, including Windows 95, Windows 98, Windows NT, Windows 2000, Windows XP, Windows Server 2003, Windows Vista, Windows 7, and Windows 8. It played a significant role in enabling cryptographic security features for a wide range of applications on these platforms.
2. Transition to Cryptography Next Generation (CNG)
Windows Vista features an update to the Crypto API known as Cryptography API: Next Generation (CNG). It has better API factoring to allow the same functions to work using a wide range of cryptographic algorithms and includes a number of newer algorithms that are part of the National Security Agency (NSA) Suite B. It is also flexible, featuring support for plugging custom cryptographic APIs into the CNG runtime. However, CNG Key Storage Providers still do not support symmetric keys. CNG works in both user and kernel mode, and also supports all of the algorithms from the CryptoAPI. The Microsoft provider that implements CNG is housed in Bcrypt.dll.
The transition to CNG marked a significant evolution in Windows cryptography. Here are key points to explain this transition:
- Enhanced Security: CNG was designed to provide enhanced security features, support for modern cryptographic algorithms, and improved protection against emerging threats. It addressed the limitations of CryptoAPI, making it more suitable for today’s security requirements.
- Flexibility and Extensibility: CNG offered a more flexible and extensible architecture, allowing developers to work with a broader range of cryptographic algorithms and services. This flexibility enabled better customization and adaptation to specific security needs.
- Backward Compatibility: While CNG became the recommended cryptographic framework, Microsoft ensured backward compatibility. Existing applications using CryptoAPI could still function, but developers were encouraged to migrate to CNG for improved security and features.
- Transition Period: During the transition, developers were provided with resources and documentation to help them adapt their applications to CNG. Microsoft also encouraged the use of best practices in cryptography to enhance security.
- Ongoing Support: Microsoft continued to support CryptoAPI for a period to ensure a smooth transition for developers and users. However, new features and improvements were primarily focused on CNG.
In summary, CryptoAPI served as a foundational cryptographic framework in earlier versions of Windows but was gradually replaced by Cryptography Next Generation (CNG) in Windows Vista and later. The transition aimed to provide better security, flexibility, and modernization of cryptographic capabilities in Windows, ensuring that applications could adapt to evolving security challenges.