In a world driven by data, how that data is managed, including the control information for its transfer, becomes critically important. One method to transmit control information is In-Band Signaling, a technique with roots deep in the history of telecommunications and a footprint that has expanded in the age of digital networking. This article aims to be your comprehensive guide to understanding what In-Band Signaling is, how it functions in various contexts, and what you need to consider when dealing with it. For a contrasting perspective, you can also explore our article on Out-of-Band Signaling.
In this article:
- What is In-Band Signaling?
- Applications and Use-Cases
- Advantages and Disadvantages
- Security Concerns
1. What is In-Band Signaling?
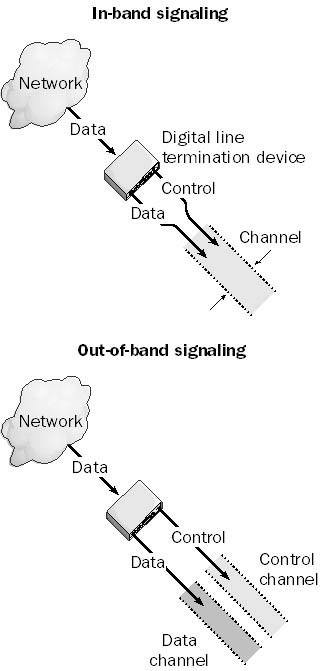
In-Band Signaling refers to the practice of transmitting control information within the same channel or frequency range used for data transmission. Unlike Out-of-Band Signaling, where a separate control channel is allocated, In-Band Signaling embeds control signals into the data stream itself. The methodology was originally popularized in older telecommunications systems but has since found applications in modern digital networks.
Imagine driving a car where the engine control unit shares the same communication link with the car’s audio system; they both communicate, but one does not interfere with the function of the other. In-Band Signaling works on a similar principle: it allows for both data and control information to be transmitted simultaneously, yet separately, within the same channel.
2. Applications and Use-Cases
In the realm of data transmission and telecommunications, this method of transmitting control information has carved out a niche for itself, seeing diverse applications ranging from legacy systems to the intricacies of modern digital networks.
Legacy Telephone Systems
One of the earliest uses of In-Band Signaling was in analog telephone systems. Dual-tone multi-frequency (DTMF) tones, often referred to as touch-tone, is a prime example. Here, specific frequencies were used to indicate different numbers on the keypad, effectively embedding the control signal within the voice channel.
Internet Telephony (VoIP)
Voice over Internet Protocol (VoIP) also utilizes In-Band Signaling. Control signals like start and end of call or quality of service (QoS) parameters are packed along with the voice data packets, enabling more efficient use of bandwidth. (See RFC 3261)
Modern Data Networks
In today’s Ethernet or Wi-Fi networks, this transmission method is also applied in frame headers and trailers, enabling the data link layer to manage flow control, error checking, and network topology information.
Streaming Services
Furthermore, popular streaming platforms often utilize Adaptive Bitrate Streaming which can adjust the quality of a video stream in real-time. This adjustment is typically made via In-Band Signaling within the data packets.
3. Advantages and Disadvantages of In-Band Signaling
As with any technology, In-Band Signaling has its own set of advantages and disadvantages that users must weigh when considering its implementation.
Advantages
Bandwidth Utilization
By using the same channel for both data and control signals, you maximize bandwidth utility, eliminating the need for a separate channel solely for control signals.
Simplicity
With no additional channels to manage, the network architecture remains relatively simple.
Cost-Effectiveness
Fewer resources are required for both hardware and maintenance when no separate control channel is needed.
Disadvantages
Complexity in Parsing
Both data and control signals sharing the same frequency range can lead to complex parsing algorithms to differentiate between the two.
Latency
The process of embedding and later extracting the control signals can introduce latency, potentially impacting real-time services.
Bandwidth Contention
If the network experiences high data traffic, control signals may experience delays, affecting performance.
4. Security Concerns
Given that control information is transmitted within the same channel as user data, several security implications need to be addressed.
Data Tampering
In-Band Signaling is vulnerable to data tampering as an attacker gaining access to the data stream could also manipulate control signals.
Eavesdropping
Control information sent in the same channel as data can also be intercepted, exposing sensitive operations.
Mitigation Strategies
Encryption
Both control and data signals should be encrypted to mitigate the risks of tampering and eavesdropping.
Firewall Rules
Furthermore, specific firewall rules can be implemented to detect anomalies in In-Band Signaling traffic, thereby reducing unauthorized access.
Regular Auditing
Frequent monitoring and auditing can help in identifying suspicious activities early on, helping to prevent possible breaches.
Finally, by considering these factors, users can more safely implement In-Band Signaling while being aware of its potential vulnerabilities.
In sum, understanding the applications, pros, and cons, along with the security aspects of this transition method can empower you to make well-informed decisions in both legacy and modern network setups.