Definition of NETWORK PACKET in Network Encyclopedia.
What is NETWORK PACKET?
A Network Packet is the fundamental unit of information transmitted over a network or over a digital communication link. Packets usually contain a header with control information about the packet type, source address, and destination address (see Network Packet Content).
They can also contain error-checking information. Packets have a logical structure based on the protocol used, but the general structure of a packet includes a header followed by a payload (data) and an optional trailer (footer). Packets can also have different sizes and structures depending on the underlying network architecture. A packet might also be called a datagram, a frame, or a cell.
Network Packet from the OSI Model perspective
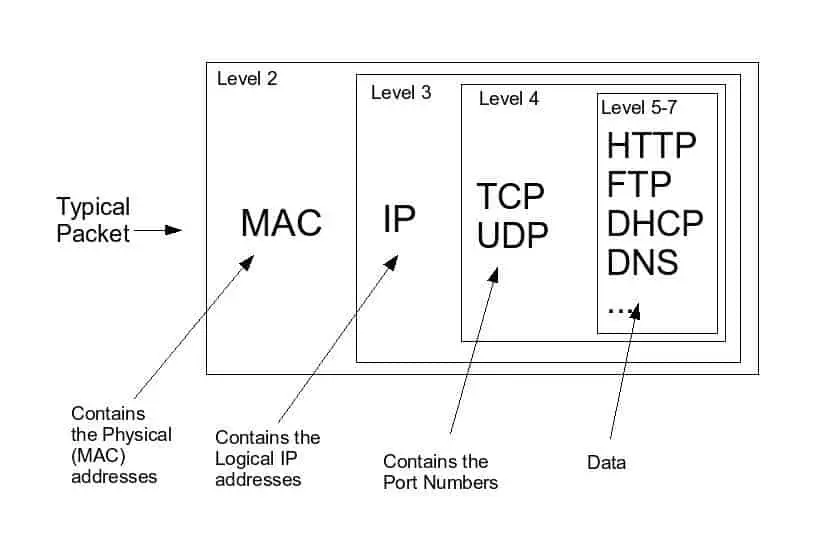
From the perspective of the Open Systems Interconnection (OSI) reference model, the terms “packet” and “frame” have precise definitions. A packet is an electronic envelope containing information formed in one of the layers from layer 3 through layer 7 of the OSI model. A frame is an electronic envelope of information that includes the packet as well as other information from all seven layers of the OSI model.
Network Packet Content
A packet may contain any of the following components:
- Addresses – The routing of network packets requires two network addresses, the source address of the sending host, and the destination address of the receiving host.
- Error detection and correction – Error detection and correction is performed at various layers in the protocol stack. Network packets may contain a checksum, parity bits or cyclic redundancy checks to detect errors that occur during transmission. At the transmitter, the calculation is performed before the packet is sent. When received at the destination, the checksum is recalculated, and compared with the one in the packet. If discrepancies are found, the packet may be corrected or discarded. Any packet loss due to these discards is dealt with by the network protocol. In some cases, modifications of the network packet may be necessary while routing, in which cases checksums are recalculated.
- Hop limit – Under fault conditions packets can end up traversing a closed circuit. If nothing was done, eventually the number of packets circulating would build up until the network was congested to the point of failure. Time to live is a field that is decreased by one each time a packet goes through a network hop. If the field reaches zero, routing has failed, and the packet is discarded. Ethernet packets have no time-to-live field and are subject to broadcast radiation in the presence of a switching loop.
- Length – There may be a field to identify the overall packet length. However, in some types of networks, the length is implied by the duration of the transmission.
- Priority – Some networks implement quality of service which can prioritize some types of packets above others. This field indicates which packet queue should be used; a high priority queue is emptied more quickly than lower priority queues at points in the network where congestion is occurring.
- Payload – Payload is the data that is carried on behalf of an application. It is usually of variable length, up to a maximum that is set by the network protocol and sometimes the equipment on the route. When necessary, some networks can break a larger packet into smaller packets.