The Password Authentication Protocol (PAP), a cornerstone in the realm of network security, plays a pivotal role in the authentication process within Point-to-Point Protocol (PPP) connections. But what makes PAP so significant in modern network communication? In this article, we will unravel the layers of PAP, exploring its operations, advantages, and its place in the ever-evolving landscape of network security protocols. Join us as we demystify PAP, providing you with a comprehensive understanding of its mechanisms and implications in today’s digital world.
Table of Contents:
- What is Password Authentication Protocol (PAP)?
- How PAP Works in PPP Connections
- Strengths and Weaknesses of Password Authentication Protocol
- PAP vs. Other Authentication Protocols
- Password Authentication Protocol in Modern Network Applications
- Conclusion
- References

1. What is Password Authentication Protocol (PAP)?
The Password Authentication Protocol (PAP) is a simple, clear-text authentication scheme used within the context of the Point-to-Point Protocol (PPP). PAP is part of the suite of protocols used to establish direct connections over serial links, including telephone lines, fiber optics, or satellite transmissions. It functions by having the client send a username and password to the server, which then verifies these credentials against its database. This protocol is straightforward and easy to implement but is noted for its lack of security features, as it transmits passwords in plain text.
Historical Context and Development
PAP’s emergence is closely linked to the development of PPP in the late 1980s and early 1990s, as outlined in RFC 1334. The primary goal was to provide a basic method for authenticating PPP connections, particularly in situations where advanced security was not a primary concern. PAP filled a need in early network configurations where simplicity and ease of use were paramount. Over time, however, as network security became a greater concern, the use of PAP diminished in favor of more secure protocols like CHAP (Challenge-Handshake Authentication Protocol) and EAP (Extensible Authentication Protocol). Despite its simplicity and vulnerabilities, PAP played a significant role in the early days of network authentication.
2. How PAP Works in PPP Connections
In PAP, the authentication process is initiated by the client, which sends an authentication request to the server. This request includes the client’s username and password. The server, upon receiving these credentials, compares them against its database. If the credentials match, the server acknowledges the authentication, allowing the connection to proceed. If the credentials do not match, the server denies access. This process is straightforward but lacks complexity, making it susceptible to various security threats such as eavesdropping and replay attacks.
PAP Packets and Their Structure
Password Authentication Protocol packets are simple in structure. There are primarily three types of packets used in the PAP process:
- Authentication-Request: This packet, initiated by the client, contains the user’s credentials (username and password). It’s sent in clear text format.
- Authentication-Acknowledge (ACK): If the server verifies the credentials as valid, it sends an ACK packet to the client, confirming successful authentication.
- Authentication-Negative Acknowledgement (NAK): Conversely, if the credentials are invalid, the server sends a NAK packet, indicating failed authentication.
Each packet has a standard format, including fields for the packet type (request, acknowledge, or negative acknowledge), a unique identifier, the length of the packet, and the actual data payload (credentials or response message). The simplicity of this packet structure is a double-edged sword—it allows for easy implementation and processing but offers minimal security features.
3. Strengths and Weaknesses of Password Authentication Protocol
Security Concerns with PAP
The primary security concern with the Password Authentication Protocol (PAP) is its simplicity, which is both its strength and its Achilles’ heel. In PAP, passwords are sent as plain text over the network, making them vulnerable to interception and eavesdropping. This vulnerability is especially concerning in modern networks where attacks such as man-in-the-middle and packet sniffing are common. Furthermore, PAP does not provide protection against replay attacks, where an attacker can capture the authentication sequence and replay it to gain unauthorized access.
Situations Where PAP is Still Relevant
Despite its security drawbacks, PAP still finds relevance in specific scenarios. It is often used in environments where legacy systems are operational, and compatibility with older network protocols is necessary. Additionally, PAP can be suitable in closed, secure networks where the threat of eavesdropping is minimal. For example, in some controlled environments like internal lab networks or in scenarios where simplicity and ease of use outweigh the security concerns, PAP might be employed.
4. PAP vs. Other Authentication Protocols
Comparisons with CHAP and EAP
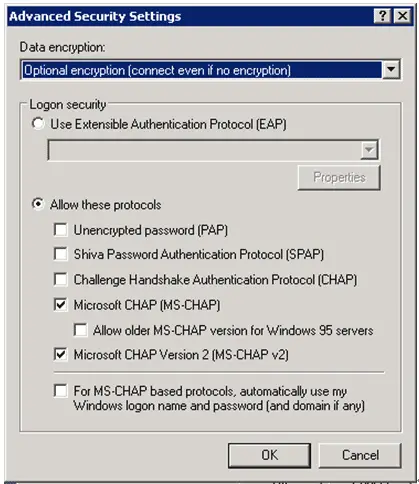
Compared to PAP, CHAP (Challenge-Handshake Authentication Protocol) provides enhanced security by using a challenge-response mechanism. In CHAP, the server sends a challenge to the client, which responds with a value calculated using a one-way hash function. This means the actual password is never sent over the network. EAP (Extensible Authentication Protocol) offers even more flexibility and security, supporting multiple authentication methods including tokens, certificates, and public key encryption. EAP is designed to be used in more complex and varied network environments, such as wireless networks and point-to-point connections.
Use Cases for Different Protocols
PAP is typically used in simpler, more controlled environments or where legacy system compatibility is a priority. CHAP, on the other hand, is better suited for environments where a higher level of security is needed but without the complexity of EAP. EAP is ideal for highly secure and complex network environments, such as enterprise Wi-Fi networks, where it can support a range of authentication methods and adapt to various security policies and requirements.
In summary, while PAP offers simplicity and ease of use, its security limitations make it less favorable for modern, high-security environments. CHAP and EAP, with their advanced security features, are more suitable for contemporary networks where security and flexibility are paramount.
5. Password Authentication Protocol in Modern Network Applications
Legacy and Current Relevance in Network Security
The Password Authentication Protocol (PAP), despite its simplicity and security limitations, holds a significant legacy in the history of network security. It was one of the first protocols to address the need for user authentication over networks, paving the way for more sophisticated methods. In modern network applications, PAP’s relevance has diminished, particularly in public and enterprise environments where security is a critical concern. However, its straightforward mechanism still finds occasional use in specific situations, such as in legacy systems or environments where network security is not a primary concern.
Evolving Authentication Standards
The landscape of network security is continually evolving, with an increasing focus on more secure and robust authentication methods. Standards like CHAP, EAP, and more recent protocols incorporate stronger encryption, multiple factor authentication, and dynamic challenge-response mechanisms. These advancements reflect the growing need for security in an increasingly interconnected world, where threats are more sophisticated, and data protection is paramount.
6. Conclusion
The Password Authentication Protocol (PAP) represents a fundamental step in the evolution of network security protocols. Its simple design provided an early solution for user authentication in network connections but fell short in the face of modern security challenges. Today, PAP’s use is largely confined to specific, controlled environments or legacy systems.
The future of network security continues to veer away from such simplistic methods, favoring more secure and adaptive protocols. As cybersecurity threats become more complex, the demand for advanced, multifaceted authentication methods will continue to grow, further diminishing the role of protocols like PAP.
7. References
- “PPP Authentication Protocols” (RFC 1334), Lloyd, B. and Simpson, W., 1992.
- “Data Communications and Networking,” by Behrouz A. Forouzan.
- “Computer Networks: A Systems Approach,” by Larry L. Peterson and Bruce S. Davie.
- “Understanding Cryptography: A Textbook for Students and Practitioners,” by Christof Paar and Jan Pelzl.
- “Network Security Essentials: Applications and Standards,” by William Stallings.
- “Internet Cryptography,” by Richard E. Smith.