Application Logs are crucial for understanding the behavior of software applications, especially for diagnosing issues and understanding usage patterns. In the context of the Windows operating system, the Application Log takes on added significance due to the integration with the Event Viewer, a powerful diagnostic tool. This article will dive deep into what an Application Log is, how it functions within the Windows OS, and its importance for both system administrators and regular users.
In this article:
- What is an Application Log?
- How Does Application Log Work in Windows?
- Logging Mechanism
- Importance of Application Logs
- How to Access and Read Application Logs in Windows
- Understanding Application Log Entries
- How to Filter and Query Application Logs
- Application Log vs. Security Log vs. System Log
- Frequently Asked Questions (FAQ)
- References
1. What is an Application Log?
An Application Log is a file that records events and transactions that occur within an application. These logs capture various types of information, such as user activities, system messages, and errors, providing a detailed record for troubleshooting and analysis.
2. How Does Application Log Work in Windows?
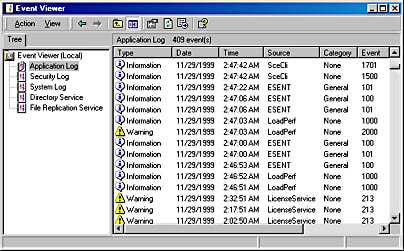
Event Viewer
In Windows operating systems, the Event Viewer is the built-in utility for viewing logs. It categorizes logs into Application, Security, and System logs, among others. The Event Viewer collects, stores, and helps you analyze these logs to keep track of what’s happening on your system.
Types of Events
- Informational Events: These are general messages that inform you about successful operations.
- Warning Events: These are cautionary messages that tell you about potential issues.
- Error Events: These are critical messages that highlight failed operations.
3. Logging Mechanism
Log Files
Application logs in Windows are stored as .evtx files. These files are binary, which means you cannot read them with standard text editors. Instead, you’ll need to use the Event Viewer or specialized software to interpret them.
Event IDs
Each event in the log is associated with an Event ID, a unique identifier that helps categorize and recognize the type of event. This ID can be used for troubleshooting by matching it against known issues or by searching for solutions online.
4. Importance of Application Logs
Application logs are not just a chronicle of software activities; they serve multiple crucial functions:
- Troubleshooting: If an application is behaving unexpectedly, the logs can provide clues for diagnosis.
- Monitoring: System administrators can keep an eye on application performance and usage.
- Compliance: Certain regulatory frameworks require keeping detailed logs to ensure that the software meets prescribed guidelines.
- Security: Unusual activities or unauthorized access can be detected.
- Optimization: By analyzing logs, developers can improve application efficiency and user experience.
5. How to Access Application Logs in Windows
Event Viewer
The primary tool for accessing application logs on a Windows system is the Event Viewer. To access it:
- Press
Win + R, typeeventvwr.msc, and press Enter. - In the left panel, navigate to
Windows Logs>Application.
PowerShell
For those who prefer the command line or need to automate tasks, PowerShell offers cmdlets like Get-EventLog and Get-WinEvent to retrieve log data.
Third-Party Tools
Several third-party solutions offer advanced features like real-time monitoring, alerts, and more. These include tools like SolarWinds, Loggly, and Graylog.
6. Understanding Application Log Entries
Basic Components
Each log entry typically contains:
- Event ID
- Source (The application or service that logged the event)
- Log Level (Information, Warning, Error, etc.)
- Date and Time
- Description
Interpreting Entries
Understanding the log entries requires a bit of expertise:
- Event ID is crucial for troubleshooting and can be searched online for solutions.
- Log Level gives you an idea of the severity of the entry.
- Description often contains detailed info which may include error codes, file paths, or other specifics.
7. How to Filter and Query Application Logs
Using Event Viewer
Event Viewer has built-in filtering options. You can right-click the ‘Application’ under ‘Windows Logs’ and choose ‘Filter Current Log.’ Here you can specify criteria like Event level, Event IDs, and a date range to narrow down your search.
Using PowerShell
PowerShell offers more robust querying features through the Get-WinEvent cmdlet. For example:
Get-WinEvent -LogName 'Application' -Level 2
This would fetch all error level events from the application log.
8. Application Log vs. Security Log vs. System Log
Windows Event Viewer categorizes logs into three main types: Application, Security, and System Logs. Understanding the differences between these types can help system administrators and tech-savvy users in identifying, solving, and preventing issues.
Application Log
The Application Log contains events logged by applications or programs. This may include errors, warnings, or informational messages concerning the application’s operation. For example, if Microsoft Word crashes, an event will be generated and logged in the Application Log.
Security Log
The Security Log holds events related to security audits. This includes (but is not limited to) login attempts, privilege escalations, and actions related to account management. It serves as a critical component in compliance and security analysis efforts, helping organizations identify suspicious or unauthorized activities.
System Log
The System Log provides information about system components such as drivers and built-in interface elements. Here you’ll find entries regarding operations of the operating system itself. For example, if a driver fails to load during startup, an event will be generated in the System Log.
Comparison
- Focus: Application Logs concern individual applications, Security Logs focus on auditing and access, and System Logs cover operating system-level events.
- Users: System administrators monitor all three, but Security Logs often require higher-level permissions to access.
- Importance: Security Logs are often the most scrutinized due to compliance mandates, while Application and System Logs are essential for troubleshooting and performance monitoring.
9. Frequently Asked Questions
What is an Event ID?
An Event ID is a unique identifier for each type of event generated and logged. This helps in quick identification and search.
How do I access the Application Log?
You can access the Application Log via Windows Event Viewer, which is accessible by running eventvwr.msc from the Run dialog or Command Prompt.
Is it possible to automate the monitoring of Application Logs?
Yes, various third-party software solutions can automate the process, offering features like real-time alerts and trend analysis.
What are the common errors found in Application Logs?
Common errors may include application crashes, file not found errors, and permission issues, among others.
How do I clear the Application Log?
You can right-click on the Application Log in Event Viewer and select ‘Clear Log.’ However, it’s essential to back up logs before doing so, especially in a business setting where audits may be required.
10. References
- “Windows Event Log” – Microsoft Docs
- “Monitoring Security Events” – Microsoft TechNet
- “Understanding Logging and Monitoring” – NIST Special Publication 800-92
- “GDPR Compliance: What it Means for IT Log Data” – Splunk
- “The Importance of Log Management for Compliance” – SolarWinds