In the vast world of Windows Operating Systems, monitoring system events is crucial for administrators to maintain optimal performance and ensure security. One central utility aiding this task is the Event Viewer. The Event Viewer captures a spectrum of events in Windows OS, categorizing them into specific logs. Among these, the Application, System, and Security Logs stand prominent. While each serves its purpose, the Security Log, in particular, plays an indispensable role in tracking security incidents and maintaining the integrity of the system. This article delves deeper into the Security Log, elucidating its significance and inner workings.
In this article:
- What is the Security Log?
- Event Viewer: The Central Monitoring Tool
- Security Log: Dive into Details
- Comparing Logs: Application, System, and Security
- Setting up and Configuring the Security Log
- Auditing and the Security Log
- Best Practices for Managing the Security Log
- Future Enhancements and Developments
- References
1. What is the Security Log?
The Security Log, as captured by Windows’ Event Viewer, is a repository of security-related event records. These records can include valid and invalid logon attempts, resource access, resource use, and the actions of users with respect to these resources. As an administrator, it’s essential to monitor the Security Log routinely, ensuring the safety of your systems and data. The information contained within helps in detecting unauthorized or malicious activities, and potential security breaches, and assists in the audit process.
2. Event Viewer: The Central Monitoring Tool
The Event Viewer is an integral component of Windows operating systems, designed to aid administrators in diagnosing problems and keeping a watchful eye over system activities. At its core, the Event Viewer is a Microsoft Management Console (MMC) snap-in, providing a unified interface that showcases a wide array of event logs. These logs capture specific system and application events based on their nature and significance.
Importance in System Administration
In the system administration world, staying informed is key. With Windows Operating Systems hosting numerous applications and processes simultaneously, it becomes imperative to track, report, and sometimes audit system behaviors. Event Viewer comes to the rescue by:
- Troubleshooting Assistance: By monitoring events and errors, administrators can swiftly detect issues, be it software conflicts or hardware malfunctions.
- Security Oversight: With cyber threats becoming increasingly sophisticated, having a log of all security-related activities helps in early detection and mitigation.
- System Optimization: Recurrent warnings or errors can indicate the need for system upgrades or configuration tweaks.
- Regulatory Compliance: For organizations mandated to comply with certain regulations, maintaining and reviewing logs can be a necessity.
Categorization of Logs
Logs within the Event Viewer are systematically categorized to streamline the process of reviewing and analyzing:
- Application Log: Captures events posted by programs. This can range from a software failure to a notification about a successful operation. See more
- System Log: Logs events flagged by Windows system components. This could be about driver failures or resource conflicts. See more
- Security Log: As previously mentioned, this deals with security-related events such as login attempts and resource access.
Additional logs, like the Directory Service, DNS Server, and File Replication Service, are also present, tailored to specific server roles.
3. Security Log: Dive into Details
Types of Events Captured
The Security Log is a goldmine of data on a system’s security events. Among the myriad of events it captures are:
- Logon/Logoff Events: This includes successful user logons, failed logon attempts, user logoffs, and session disconnects.
- Object Access: Any attempt to access specific files, directories, or other objects that have been audited.
- Privilege Use: Events triggered when users exercise rights like changing system time or backing up files.
- Policy Change: This pertains to changes in user rights assignments, audit policies, or trust relationships.
- System Events: Indicators of system restarts or shut-downs, or events affecting security logs themselves.
- Process Tracking: Details about processes that have been invoked or terminated.
Access Control and Permissions
Controlling who can view or manipulate the Security Log is pivotal. After all, in the wrong hands, this data can be misused. Windows employs a two-pronged approach:
- Log Access: Only users with the ‘Manage auditing and security log’ right (usually administrators) can view security logs.
- Log Management: Actions like clearing logs also necessitate specific permissions. It’s recommended to restrict these rights to minimize risks.
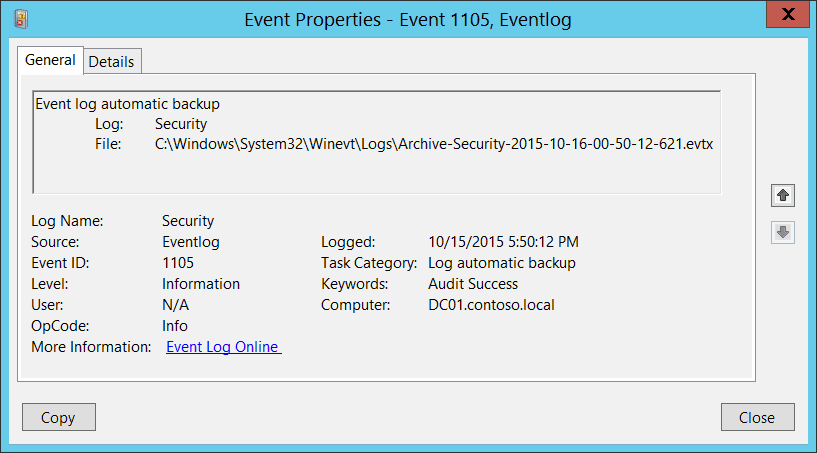
Interpreting Event Codes and Categories
For every event captured, the Security Log provides a wealth of data:
- Event ID: A unique identifier for each event type. For instance, ‘4624’ indicates a successful logon.
- Category: This gives context about the event nature, such as Logon, Object Access, or System Event.
- User: Details about which user account was involved.
- Computer: The machine where the event transpired.
- Description: A comprehensive overview of the event, providing crucial insights.
By deciphering these codes and categories, administrators can glean not only the ‘what’ but also the ‘why’ behind system events.
4. Comparing Logs: Application, System, and Security
Key Differences and Purposes
Each log within the Event Viewer serves a distinct purpose, catering to different aspects of system operation:
- Application Log: Primarily records events logged by applications or programs. For instance, if an application crashes or encounters an error, the specifics will be registered here.
- System Log: Reflects the operations of the Windows OS components. If a hardware driver fails to load or there’s a network issue, the System Log will capture this information.
- Security Log: Exclusively for events linked to security, it provides an audit trail of all security-related activities, such as failed logins, object access, and policy changes.
When to Check Which Log
Knowing which log to review is essential for efficient troubleshooting:
- Application Log: Ideal when diagnosing issues related to specific software or applications. If a program repeatedly crashes or misbehaves, this log provides the initial clues.
- System Log: Turn to this when facing system-wide disturbances, like unexpected reboots, hardware conflicts, or network disconnections.
- Security Log: Review this when investigating potential security breaches, unauthorized access attempts, or auditing user activities for compliance.
The Interrelation and Workflow
While distinct, these logs are not isolated entities. Often, an event in one log may correlate to an event in another. For example, a failed application event in the Application Log due to inadequate permissions might correspond to a denied access event in the Security Log. By cross-referencing these logs, administrators can piece together a holistic picture of system operations and issues.
5. Setting up and Configuring the Security Log
Specifying Event Types to Capture
- Open the ‘Local Security Policy’ management console.
- Navigate to ‘Advanced Audit Policy Configuration’ under ‘Security Settings’ > ‘Advanced Audit Policy Configuration’ > ‘Audit Policies’.
- Here, you can define which specific security events to track, such as Logon/Logoff, Object Access, or System Events.
Setting Log Size and Overwrite Policies
Managing the size of the Security Log ensures it doesn’t consume undue disk space:
- Open Event Viewer and locate the ‘Security’ log under ‘Windows Logs’.
- Right-click and select ‘Properties’.
- Set the ‘Maximum log size’ as desired. You can also choose the behavior once this size is reached: either overwrite older entries or archive the log when full.
Advanced Filtering Options
Windows allows for meticulous event filtering to pinpoint specific entries:
- In the Event Viewer, right-click on the ‘Security’ log and choose ‘Filter Current Log’.
- You can specify criteria like Event levels (Critical, Warning, etc.), Event IDs, date ranges, or specific keywords.
- Apply the filters to view only the events that match your criteria.
6. Auditing and the Security Log
Importance of Auditing in Security
Auditing plays a pivotal role in ensuring the security of IT infrastructures. It facilitates the tracking of activities, helping administrators pinpoint unauthorized or suspicious actions. The Security Log is the heart of Windows’ auditing mechanism. By meticulously logging security-related events, it provides a transparent view of user activities, permissions changes, and system alterations, serving as the first line of defense against potential security threats.
Configuring Audit Policies
Windows offers granular control over what to audit:
- Access ‘Local Security Policy’ from Administrative Tools.
- Under ‘Advanced Audit Policy Configuration’, select the desired categories like ‘Account Management’ or ‘Policy Change’.
- Define the specific events you wish to audit—successes, failures, or both. For instance, you might want to track successful file accesses but only failed login attempts.
Analyzing Audit Results
Once auditing is enabled, it’s vital to interpret the results:
- Open Event Viewer and navigate to the ‘Security’ log.
- Examine entries for patterns. Multiple failed logins from an unknown IP, for instance, might suggest a brute force attack attempt.
- Use the ‘Filter Current Log’ option to hone in on specific event types or periods, aiding in more precise analysis.
7. Best Practices for Managing the Security Log
Routine Monitoring and Review
Consistent monitoring is crucial:
- Dedicate specific intervals, be it daily or weekly, to review the Security Log. Regular reviews help identify patterns and address potential threats proactively.
- Archive logs periodically. Storing older logs ensures that you retain a record of past events for future analysis or compliance needs.
Integrating with Third-Party Security Tools
While the Event Viewer is powerful, it’s often beneficial to integrate with specialized security tools:
- Tools like Splunk or SolarWinds can digest log data, providing enhanced analytics and visualization.
- Integration can centralize logs from multiple sources, offering a consolidated view of security events across the enterprise.
Alert Configurations and Proactive Measures
Instead of merely being reactive, adopt a proactive stance:
- Configure alerts for critical events. For instance, receiving an immediate notification for numerous failed logins can help thwart an ongoing attack.
- Use built-in Task Scheduler in conjunction with Event Viewer to automate responses to specific events. This could include sending emails, starting scripts, or even shutting down systems in response to particular security incidents.
By adhering to these practices, administrators can harness the full power of the Security Log, ensuring not just compliance but also a secure, transparent, and resilient IT ecosystem.
8. Future Enhancements and Developments
As the digital realm continues to evolve, so does the importance of security logs and their associated tools. In this chapter, we explore the forthcoming advancements that aim to make the Security Log more resilient, intuitive, and proactive in thwarting potential security threats.
Evolution of Security Logs in Modern Operating Systems
Modern operating systems are constantly adapting to new security challenges. The granularity and depth of logging have improved significantly over the years. The trend is leaning towards real-time logging and immediate notification systems, ensuring that administrators can respond to threats as they happen. Moreover, modern OS is focusing on:
- Integration with Cloud: With businesses transitioning to cloud environments, security logs are also evolving to ensure seamless integration with cloud platforms, ensuring consistent monitoring across both on-premises and cloud infrastructures.
- Enhanced User Interfaces: The move is towards more user-friendly, graphical presentations of logs, making it easier for administrators to understand and respond to threats without delving into the technicalities.
Integration with AI and Predictive Analytics
Artificial Intelligence (AI) and predictive analytics are transforming how we perceive security logs:
- Automated Analysis: AI-driven systems can sift through vast amounts of log data, identifying patterns and anomalies faster than any human could.
- Predictive Threat Detection: Predictive analytics can forecast potential security breaches based on past data, giving administrators a heads-up before the actual threat materializes.
- Intuitive Visualizations: AI can create dynamic, interactive dashboards that highlight potential areas of concern, making data interpretation more intuitive.
Upcoming Features and What to Look Forward To
The roadmap for the evolution of security logs looks promising:
- Real-time Collaboration Tools: Future security logs will have built-in collaboration tools allowing immediate discussion and action on identified threats.
- Holistic Integration: Expect tighter integration between the Security Log, Application Log, and System Log, providing a 360-degree view of the system’s health and security.
- Open-source Log Analytics Platforms: With the rising trend of open-source solutions, anticipate more community-driven log analytics tools that are versatile and adaptable to specific business needs.
10. References
- Books:
- Windows Security Monitoring: Scenarios and Patterns by Andrei Miroshnikov.
- Mastering Windows Server 2019 by Jordan Krause.
- RFCs:
- Web Articles: