Definition of Event Viewer in the Network Encyclopedia.
In this article
- What is the Event Viewer
- View Events from Multiple Event Logs
- Event Viewer on Remote Computers
- Schedule a Task
- Manage Event Subscriptions
What is the Event Viewer?
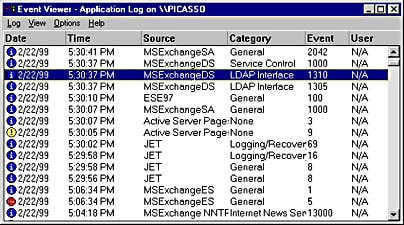
The Event Viewer is a Microsoft Management Console (MMC) snap-in that enables you to browse and manage event logs. It is an indispensable tool for monitoring the health of systems and troubleshooting issues when they arise.
Event Viewer enables you to perform the following tasks:
- View events from multiple event logs.
- Save useful event filters as custom views that can be reused.
- Work with event logs on remote computers.
- Schedule a task to run in response to an event.
- Create and manage event subscriptions.
Events are significant actions that take on a server or computer and include the following:
- A process has been completed, such as the defragmentation of a database.
- A service has been started, stopped, or paused.
- A service has issued an unexpected response to a client.
- A service was unable to start.
- A memory violation has occurred, resulting in an application being terminated.
Event Viewer records events in many different logs such as:
- System log: Records warnings, errors, and information events about Windows NT services and devices
- Security log: Records success and failure events for objects being audited
- Application log: Records warnings, errors, and information events about applications running on the server
The system and application logs should be monitored regularly for signs of problems with devices, services, or applications running on the server. When a problem occurs, Event Viewer is the first place you should check. If auditing is configured on the server, you can monitor the security log for signs of attempted unauthorized access (failure audits) or for an indication of resource usage (success audits).
View Events from Multiple Event Logs
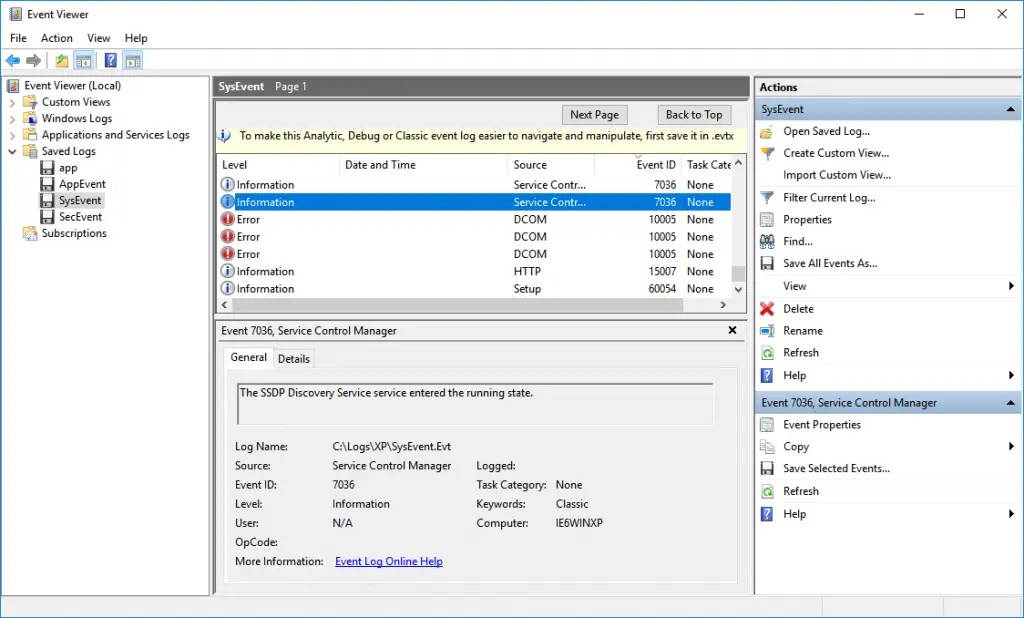
When you use Event Viewer to troubleshoot a problem, you need to locate events related to the problem, regardless of which event log they appear in. Event Viewer enables you to filter for specific events across multiple logs, making it easy to display all events that are potentially related to an issue that you are investigating. To specify a filter that spans multiple logs, you need to create a custom view.
Create a Custom View
You can create a filter that includes events from multiple event logs that satisfy specified criteria. You can then name and save that filter as a custom view. To apply the filter associated with a saved custom view, you navigate to the custom view in the console tree and click on its name.
To create a custom view:
- Start Event Viewer.
- On the Action menu, click Create Custom View.
- To filter events based upon when they occurred, select the corresponding time period from the Logged drop-down list.
- In Event level, select the check boxes next to the event levels that you want included in the custom view.
- You can either specify the event logs or the event sources of the events that will appear in the custom view.
- To specify the event logs: Select the Event Log option and, in the Event log drop-down list, select the check boxes next to the event logs from which you want to include events.
- To specify the event sources: Select the Event Source option and, in the Event source drop-down list, select the check boxes next to the event sources in the drop-down list that you want to include in the custom view.
- In Event IDs, type the event IDs that you want your custom view to display. Separate multiple event IDs by commas. If you want to include a range of IDs, say 4624 through 4634 inclusive, type 4624-4634. If you want your filter to display events with all IDs except certain ones, type the IDs of those exceptions, preceded by a minus sign. For example, to include all IDs between 4624 and 4634 except for 4630, type 4624-4634,-4630.
- In User, enter the name of the user accounts you want to display. Enter multiple users by separating them with a comma (,).
- In Computer(s), enter the name of the computers that you want your custom view to display. Enter multiple computers by separating them with a comma (,) and click OK.
- On the Save Filter to Custom View dialog box, in Name, type a name for the custom view.
- In Description, type an optional description of the custom view and then select the folder in which you want to store the custom view.
- You can make the Custom View accessible to anyone using the computer or only to someone logged on to your current account.
- To save the custom view and make it accessible to anyone using the computer: Ensure the All Users check box is selected and click OK.
- To save the custom view and make it accessible only to someone logged on to your current account: Ensure that the All Users check box is not selected and click OK.
Note: Leaving a field in the Create Custom View dialog box blank specifies that you want your filter to display entries with any value of the corresponding property.
Event Viewer on Remote Computers
You can use the Event Viewer or the wevtutil command at a command prompt to manage event logs on a remote computer.
To use Event Viewer to manage event logs on a remote computer
- Start Event Viewer.
- Click the root node, for example Event Viewer (Local), in the console tree.
- On the Action menu, click Connect to Another Computer.
- In the Another computer box, type the name or IP address of the remote computer.
- (Optional) Select Connect as another user, click Set User, enter the User name and Password, end then click OK.
- Click OK.
To use wevtutil to manage event logs on a remote computer
- To open a Command Prompt window, click Start, in the Start Search box, type cmd, and then press Enter.
- Type the following command in the Command Prompt window:
wevtutil <command> /r:<remote_computer_name>
Enable Remote Event Log Management in the Firewall
You must enable the Remote Event Log Management exception in the Windows Firewall Settings on the remote computer to which you want to connect.
You can type **eventvwr<remote_computer_name>** in a Command Prompt window to start Event Viewer and connect to a remote computer. You can also include options that enable Event Viewer to start with a specified Custom View or with a particular log selected. To learn more about the eventvwr command, type eventvwr /? in a Command Prompt window. Although you can use the eventvwr command to start Event Viewer and connect to computers running previous versions of Windows, any options specified will be ignored.
When connected to a remote computer, Custom Views displayed by the Event Viewer are the Custom Views stored on the local computer. If you click one of those local Custom Views, the underlying query will be run against the event logs on the remote computer.
Schedule a Task
By using Event Viewer, you can easily automate responses to events. Event Viewer is integrated with Task Scheduler, enabling you to right-click most events to start scheduling a task to run when that event is logged in the future.
To Run a Task in Response to a Given Event
- Start Event Viewer.
- In the console tree, navigate to the log that contains the event you want to associate with a task.
- Right-click the event and select Attach Task to This Event.
- Perform each step presented by the Create Basic Task Wizard.
Manage Event Subscriptions
Event Viewer enables you to view events on a single remote computer. However, troubleshooting an issue might require you to examine a set of events stored in multiple logs on multiple computers.
To specify which events to collect, you can create an event subscription. The subscription specifies exactly which events will be collected and in which log they will be stored locally. Once a subscription is active and events are being collected, you can view and manipulate these forwarded events as you would any other locally stored events.
Using the event collecting feature requires that you configure both the forwarding and the collecting computers. The functionality depends on the Windows Remote Management (WinRM) service and the Windows Event Collector (Wecsvc) service. Both of these services must be running on computers participating in the forwarding and collecting process. To learn about the steps required to configure event collecting and forwarding computers, see Configure Computers to Forward and Collect Events.
Creating a new subscription
Once you have configured the computers, you can create a subscription to specify which events to collect.
- On the collector computer, run Event Viewer as an administrator.
- Click Subscriptions in the console tree.
- On the Actions menu, click Create Subscription.
- In the Subscription Name box, type a name for the subscription.
- In the Description box, enter an optional description.
- In the Destination Log box, select the log file where collected events are to be stored. By default, collected events are stored in the ForwardedEvents log.
- Click Add and select the computers from which events are to be collected.
- Click Select Events to display the Query Filter dialog box. Use the controls in the Query Filter dialog box to specify the criteria that events must meet to be collected.
- Click OK on the Subscription Properties dialog box. The subscription will be added to the Subscriptions pane and, if the operation was successful, the Status of the subscription will be Active.
Events raised on the forwarder computers that meet the criteria of the subscription will be copied to the collector computer log specified in step 6.
Event Viewer is around since Windows NT