In the digital age, where data security is paramount, understanding various authentication methods is crucial. Basic Authentication, also known as Clear-Text Authentication, stands out for its simplicity and widespread application across the internet. This method involves transmitting user credentials—typically a username and password—over a network in an unencrypted form. While Basic Authentication offers straightforward implementation, it raises significant security concerns, as unencrypted credentials can be easily intercepted and read. Despite this, it remains a common choice in various web server systems, including IIS (Internet Information Services) and Apache.
In this article, we will dissect Basic Authentication, examining its mechanics, usage in different web server environments, and delve into its security implications. Our exploration will provide valuable insights for web developers, network administrators, and security professionals, highlighting both the utility and vulnerabilities of this authentication method.
Table of Contents:
- What is Basic Authentication?
- Basic Authentication in Web Server Systems
- Security Analysis of Basic Authentication
- Enhancing Security with Basic Authentication
- Alternatives to Basic Authentication
- References

1. What is Basic Authentication?
Definition and Mechanics
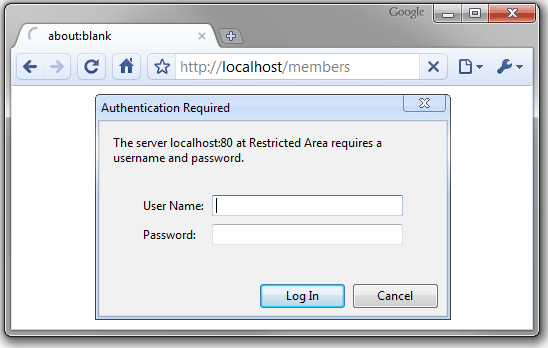
Basic Authentication is a method used in HTTP for an application or a web server to request a username and password from a client. The credentials are then sent across the network as part of the HTTP request header.
- Transmission Process: The credentials are encoded using Base64, a binary-to-text encoding scheme. While this encoding disguises the credentials from casual inspection, it is not encryption and can be easily decoded.
- Usage in HTTP: When a server or application using Basic Authentication receives a request, it sends back a response with a
401 Unauthorizedstatus and aWWW-Authenticateheader. The client must then resend the request with the appropriateAuthorizationheader containing the Base64-encoded credentials.
Historical Context
- Origins and Evolution: Basic Authentication has been part of the HTTP protocol since the early days of the internet, defined in RFC 1945 (HTTP/1.0) and later in RFC 2617 for HTTP/1.1. Its simplicity made it one of the earliest methods to control access to web resources.
- Widespread Use: Despite its security limitations, Basic Authentication gained widespread use due to its ease of implementation and support across various platforms and web servers.
Security Implications
- Clear-Text Vulnerability: The primary security concern with Basic Authentication is that the credentials are transmitted in clear text (encoded but not encrypted). This makes them vulnerable to interception, especially if the connection is not secured with HTTPS.
- Limited Use Cases: Given these vulnerabilities, Basic Authentication is often recommended only for specific use cases, such as internal networks or systems where higher security levels are not required or where HTTPS is consistently used to encrypt the data in transit.
In summary, Basic Authentication serves as a straightforward method for securing web resources but comes with notable security risks due to its clear-text nature. Understanding these risks is essential for anyone implementing or managing web authentication systems. The next chapters will explore how Basic Authentication is implemented in popular web servers like IIS and Apache and delve into effective practices to mitigate its inherent security weaknesses.
2. Basic Authentication in Web Server Systems
Implementation in IIS (Internet Information Services)
- Setting Up Basic Authentication in IIS: In IIS, Basic Authentication can be enabled through the IIS Manager. This is done by accessing the Authentication feature of the website or application and enabling the Basic Authentication module. It requires a Windows domain account or a local account on the web server.
- Configuring User Credentials: Administrators must ensure that proper user accounts and permissions are set up within their Windows environment. These accounts are used to validate the credentials sent through Basic Authentication.
- Security Considerations: IIS typically recommends using Basic Authentication over an SSL/TLS connection to ensure that the credentials are encrypted during transmission. This is crucial as credentials are otherwise sent in clear text.
Implementation in Apache Web Server
- Enabling Basic Authentication in Apache: In Apache, Basic Authentication is managed through the
.htaccessfile or directly in the Apache configuration file (httpd.conf). This involves setting up a directive within the directory or location block where authentication is required. - Creating a Password File: Apache requires a password file, typically created using the
htpasswdutility. This file stores the user credentials which are used to authenticate the request. - Access Control: Apache allows fine-grained control over access to resources. Administrators can configure which users or groups are allowed or denied access in the context of Basic Authentication.
Comparison of Configuration and Management
- Ease of Setup: Apache’s Basic Authentication setup is more manual and requires direct editing of configuration files, whereas IIS offers a GUI-based setup through the IIS Manager.
- Flexibility and Control: Apache provides more flexibility in terms of configuration, allowing for complex setups like per-directory authentication and integration with various modules. IIS, while less flexible, integrates seamlessly with Windows-based authentication systems.
- Security Practices: Both systems recommend the use of HTTPS when employing Basic Authentication. Apache, however, provides more options for custom configurations and integrating additional security measures.
- User Management: IIS directly utilizes Windows user accounts, making it more straightforward for environments already operating within a Windows domain. Apache, on the other hand, requires a separate management of a password file, giving administrators more control but also adding a layer of complexity.
In summary, Basic Authentication in both IIS and Apache serves the same fundamental purpose but differs in terms of configuration, management, and flexibility. Understanding these differences is crucial for administrators and developers to effectively implement and manage Basic Authentication in their respective environments. While both platforms provide the means to secure resources, the choice between IIS and Apache often depends on the specific requirements of the environment, existing infrastructure, and the level of control and customization needed.
3. Security Analysis of Basic Authentication
In-Depth Examination of Security Drawbacks
Basic Authentication, a method once widely used for its simplicity, faces significant security challenges in today’s complex web environments:
- Vulnerability to Eavesdropping: The most glaring risk associated with Basic Authentication is its susceptibility to eavesdropping. Credentials sent in Base64 encoding over an unencrypted connection can be easily intercepted and decoded using simple tools, exposing user data to potential misuse.
- Man-in-the-Middle Attacks: In scenarios where the network security is compromised, attackers can position themselves between the client and server to capture or manipulate the credentials being transmitted.
- Replay Attacks: Once credentials are intercepted, they can be reused (or replayed) by an attacker to gain unauthorized access, as the credentials remain valid until they are changed.
- Credential Storage and Caching: Browsers and servers often cache credentials, increasing the risk if the cache is accessed by unauthorized entities. Insecure storage practices on the server side can also lead to vulnerabilities.
Scenarios Posing Elevated Risks
- Use in Public or Unsecured Networks: Deploying Basic Authentication in public networks significantly increases the risk of credential interception.
- Applications Requiring High Security: In applications where sensitive data is involved, such as financial or personal information, Basic Authentication’s inherent weaknesses make it an unsuitable choice.
- Long-term Session Maintenance: For services that maintain long-term sessions without regularly revalidating credentials, the use of Basic Authentication can pose ongoing security risks.
Impact on Overall Web Security
- Scope of Risk: The risks associated with Basic Authentication extend beyond individual user accounts. A compromised account can potentially lead to broader security breaches, affecting organizational data and network integrity.
- Compliance and Regulatory Concerns: In the context of regulatory standards like GDPR or HIPAA, the use of Basic Authentication might not comply with the required security measures, leading to legal and reputational risks.
Mitigation Strategies
While Basic Authentication has inherent vulnerabilities, certain measures can mitigate some of its risks:
- Strict HTTPS Enforcement: Using HTTPS exclusively can protect the credentials in transit, although this does not address other vulnerabilities like storage or replay attacks.
- Network Security Best Practices: Implementing network-level security measures, such as firewalls and intrusion detection systems, can reduce the risk of unauthorized access and interception.
- Regular Credential Rotation: Encouraging or enforcing regular password changes can limit the window of opportunity for exploited credentials.
In summary, the security analysis of Basic Authentication reveals several vulnerabilities that pose substantial risks in modern web environments. Understanding these risks and their implications is crucial for anyone using or considering Basic Authentication in their web or API applications. The subsequent chapters will delve into methods for enhancing the security of Basic Authentication and explore more secure alternatives.
4. Enhancing Security with Basic Authentication
Strengthening Basic Authentication
While Basic Authentication has inherent weaknesses, certain practices can enhance its security, especially when high-level alternatives are not feasible:
- Mandatory Use of HTTPS: The most crucial step is ensuring that Basic Authentication credentials are always sent over HTTPS. Encrypting the communication channel with SSL/TLS prevents the interception of credentials during transmission.
- Implementing Secure Headers: Utilize HTTP security headers like Strict-Transport-Security (HSTS) to enforce secure connections and prevent SSL stripping attacks.
- Isolation of Sensitive Applications: For applications handling sensitive data, isolate them in a secure network zone. Use Basic Authentication only where necessary and combine it with network-level security measures.
Additional Security Practices
- Two-Factor Authentication (2FA): Introducing an additional layer of authentication can significantly reduce the risk of unauthorized access. While not always directly compatible with Basic Authentication, 2FA can be implemented in the overall login process.
- Robust Password Policies: Enforce strong, complex passwords and regularly prompt users to change them. Implement account lockout policies to mitigate brute-force attacks.
- Limited Session Duration: Implement timeouts for user sessions and require re-authentication after the session expires, reducing the window of opportunity for exploiting stolen credentials.
- Monitoring and Auditing: Regularly monitor access logs for any unusual activities. Auditing and logging can help in early detection of security breaches.
5. Alternatives to Basic Authentication
Exploring More Secure Authentication Methods
Given the security limitations of Basic Authentication, several more secure alternatives are available:
- OAuth: A robust, token-based standard widely used for secure and flexible authorization, especially in scenarios involving third-party access to user data. OAuth tokens do not expose user credentials and can be limited to specific scopes and durations.
- JWT (JSON Web Tokens): JWTs are used for secure transmission of information between parties as a JSON object. They are useful for stateless authentication and are widely used in modern web applications and APIs.
- Digest Authentication: A more secure variant of Basic Authentication, Digest Authentication uses MD5 hashing of the credentials along with a nonce value, making it more resistant to credential interception.
Considerations for Selecting Authentication Methods
- Security Requirements: The choice of authentication method should be based on the specific security needs of the application. High-security applications may require more robust methods like OAuth or JWTs.
- Application Architecture: Consider how the authentication method integrates with the application’s architecture. Stateless applications may benefit from token-based systems like JWT.
- User Experience: Some methods, like OAuth, can provide a better user experience, especially in scenarios involving third-party services.
- Compliance Needs: Ensure that the chosen authentication method aligns with any relevant compliance and regulatory requirements.
6. References
- RFC 2616 – Hypertext Transfer Protocol — HTTP/1.1: Details on the HTTP protocol, including Basic Authentication.
- RFC 6749 – The OAuth 2.0 Authorization Framework: Provides comprehensive information on OAuth 2.0.
- RFC 7519 – JSON Web Token (JWT): Describes the JWT standard for securely transmitting information.
- OWASP (Open Web Application Security Project): Offers resources and guidelines on web application security, including authentication best practices.
- “Internet Information Server Documentation“, Microsoft Learn.
- “Apache HTTP Server Documentation“, Apache.org