Category: Networking Fundamentals
-
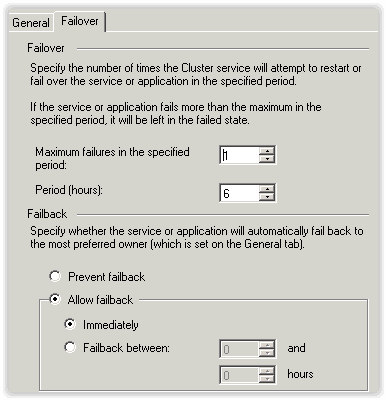
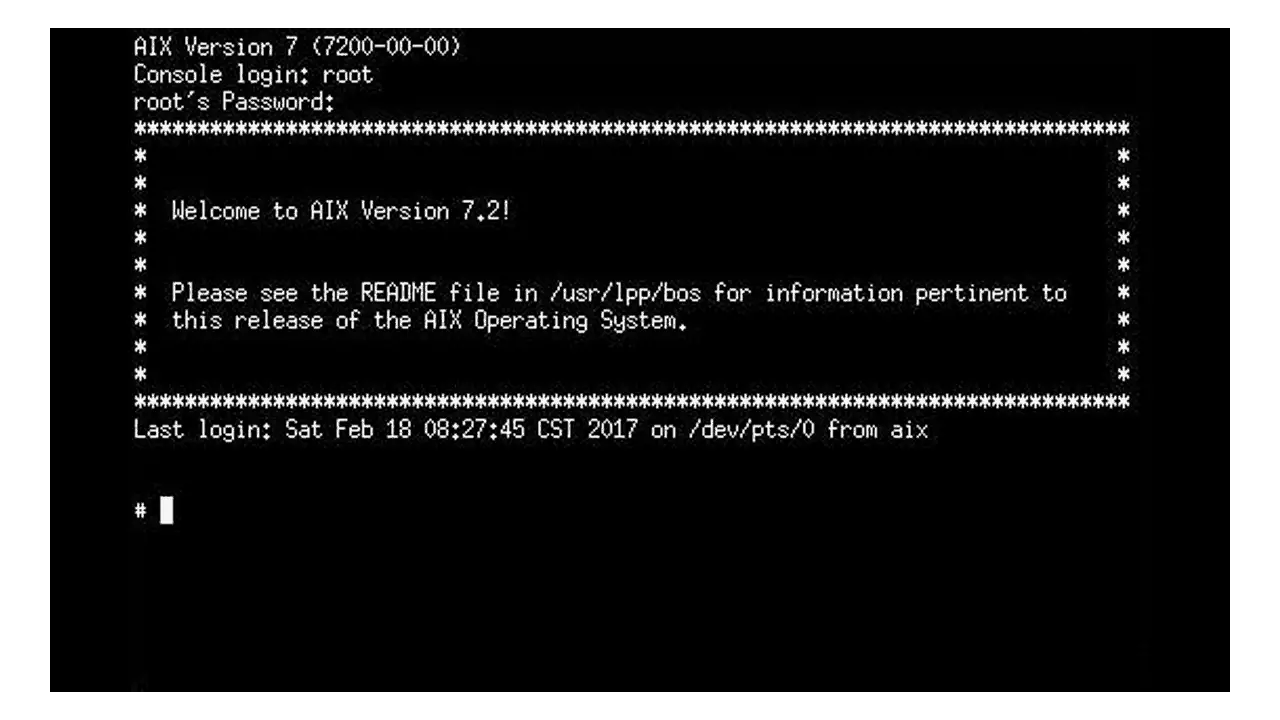
Failback
Unlock the complexities of Failback in computer networking. Explore definitions, technical mechanisms, and best practices. Your guide to system resilience.
-
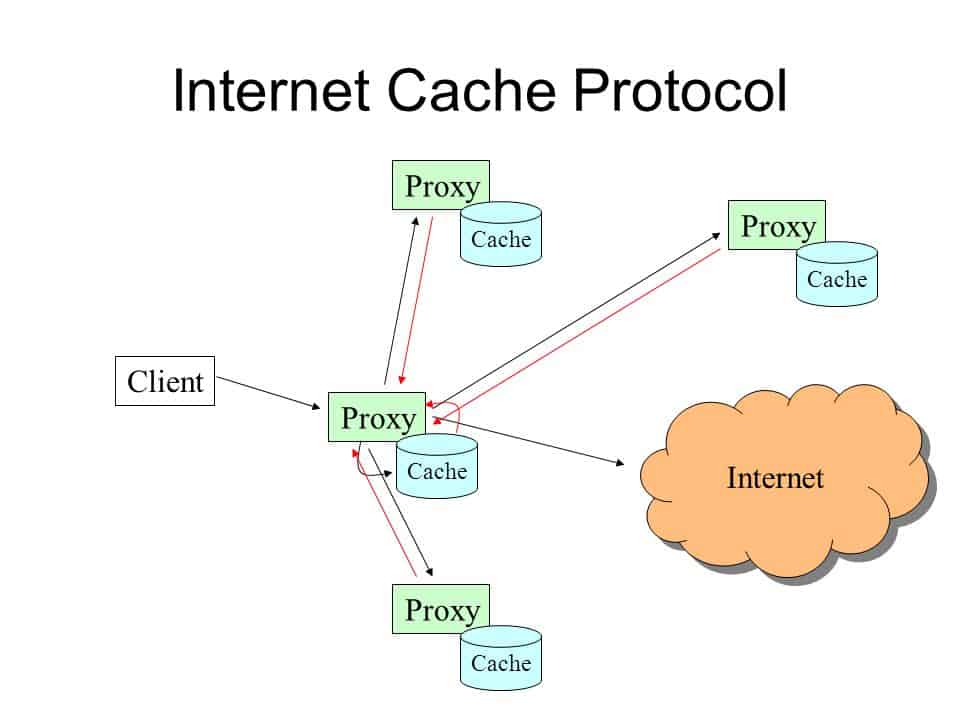
Internet Cache Protocol (ICP)
Internet Cache Protocol is a UDP-based protocol developed in 1995 to allow arrays of proxy servers to communicate and work together over a network.
-
Internet Control Message Protocol (ICMP)
ICMP stands for Internet Control Message Protocol is a TCP/IP network layer protocol used by routers and TCP/IP hosts for building and maintaining routing tables, adjusting data flow rates, and reporting errors and control messages for TCP/IP network communication.
-
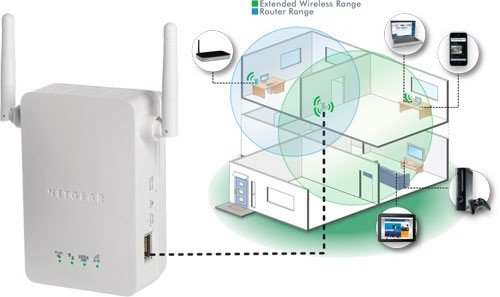
WiFi Range Extender
You can expand your Wifi network with a Wifi Range Extender (or WiFi Repeater). See how it works and how easy is to set it up.
-
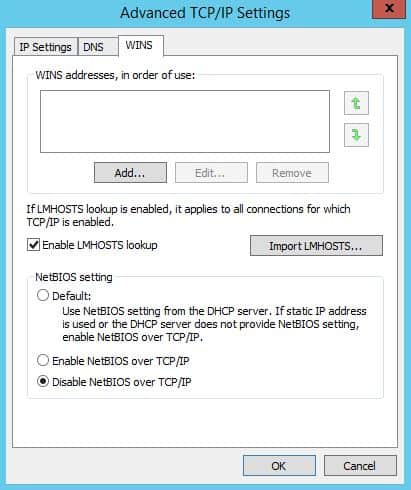
NetBT: NetBIOS over TCP/IP
Discover the inner workings of NetBT, the protocol enabling NetBIOS functionalities over TCP/IP networks. Learn how NetBT is critical for name resolution and session support, especially in Windows environments.
-

NetBIOS (Network Basic Input/Output System)
NetBIOS stands for Network Basic Input/Output System, is a specification created by IBM and Microsoft that allows distributed applications to access each other’s network services independent of the transport protocol used.
-
Transmission Control Protocol (TCP)
Unlock the mysteries of TCP, the backbone of modern internet communication. From its history to its inner workings, discover how TCP makes the internet tick.
-

Network Cabinet Essentials: Organizing Your Network Infrastructure
Discover the pivotal role of Network Cabinets in managing IT infrastructure. Learn about types, technical features, and best practices in our guide.
-

Analog Modem: Tracing the Evolution from Acoustic Couplers to 56K
An analog modem stands as a pivotal device in the history of telecommunications, enabling digital data to traverse the analog infrastructure of traditional telephone lines.
-
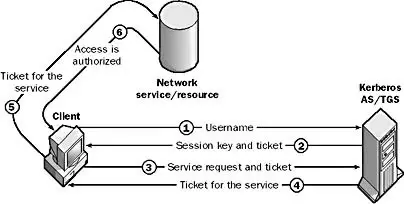
Kerberos v5 Security Protocol
Kerberos Protocol is a method of securely authenticating users’ requests for access to services on a network.
-
Y Splitter in Networking: Expand Your Connections
Explore the essential role of Y Splitters in computer networking, from Ethernet to fiber optics, and how they expand connectivity options.