A Domain Local Group in Windows Server is a security group that plays a pivotal role in managing access to resources within a specific domain. It allows for granular control over who can access certain network resources, such as files, folders, and printers, by assigning permissions to the group rather than to individual users.
This article will dive deep into the functionality, configuration, and best practices of Domain Local Groups, ensuring you can leverage their full potential to streamline access management and bolster your network’s security.
Table of Contents:
- What is a Domain Local Group on Windows Server?
- Creating and Managing Domain Local Groups
- Strategic Use of Domain Local Groups
- Integrating Domain Local Groups Across Trust Boundaries
- References

1. What is a Domain Local Group on Windows Server?
A Domain Local Group is a specialized security group in Windows Server, pivotal for managing access to resources within an Active Directory (AD) domain. Active Directory, a cornerstone of Windows Server networking, must be operational, and a domain established, for Domain Local Groups to exist. These groups facilitate granular access control by aggregating users, thereby streamlining permissions management for domain resources like files and printers.
Active Directory: The Foundation
Before leveraging Domain Local Groups, ensure Active Directory Domain Services (AD DS) is installed and configured on your Windows Server, transforming it into a domain controller. This setup is crucial as it underpins the creation and management of Domain Local Groups, alongside other directory objects, within a structured, secure domain environment.
Domain Essentials
Creating a domain is a prerequisite. It serves as the environment where Domain Local Groups operate, defining the boundary for their scope and permissions. Within this boundary, Domain Local Groups offer a flexible yet powerful means to manage user permissions with precision, embodying the essence of effective network resource administration.
The A-G-DL-P procedure
To use a domain local group, you first determine which users have similar job responsibilities in your enterprise. Then you identify a common set of network resources in a domain that these users might need to access. Next, you create a domain local group for the users and assign the group appropriate permissions to the network resources. This procedure is called A-G-DL-P (access, group, domain local, permissions), which is a variation of the AGLP administration paradigm used in Windows NT-based networks.
2. Creating and Managing Domain Local Groups
Step-by-Step Guide to Creation
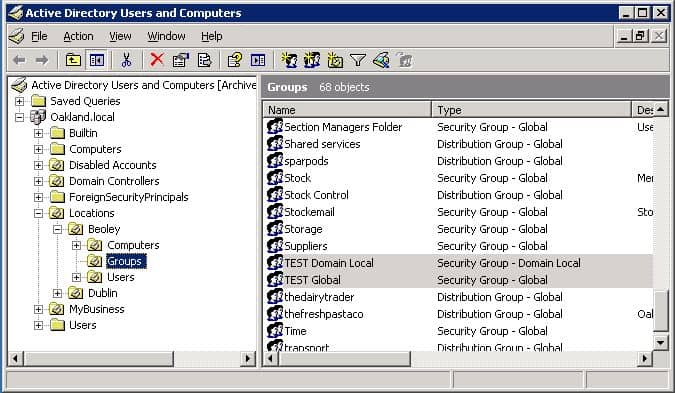
- Initiate Active Directory Users and Computers: Begin by launching this tool from the Administrative Tools folder. It’s your gateway to managing AD objects.
- Navigate to Your Domain: Within the console, locate and select the domain or the specific Organizational Unit (OU) where the Domain Local Group will reside.
- Forge the Group: Right-click the chosen location, select “New,” then “Group.” In the dialog, input a meaningful name that reflects the group’s purpose, ensuring clarity and coherence.
- Specify Group Characteristics: Set the group scope to “Domain local” and the group type to “Security.” These settings are essential for defining the group’s operational context and its capability to hold permissions.
- Enlist Members: With the group created, proceed to populate it by adding users, computers, or other groups. This step is where the group’s utility in permission management comes to life.
Best Practices for Management
- Conduct Regular Audits: Periodically review group memberships and permissions. This practice ensures that access rights remain aligned with current roles and security policies.
- Adhere to Naming Conventions: Employ descriptive, consistent naming for groups. This approach aids in identification and reduces administrative errors.
- Embrace Nesting: Utilize nested groups strategically to refine access control without complicating the direct assignment of permissions to individual users.
- Document Religiously: Maintain meticulous records of each group’s purpose, membership, and assigned permissions. Documentation is a linchpin for operational continuity and compliance.
3. Strategic Use of Domain Local Groups
Access Control and Permissions Management
Domain Local Groups are instrumental in implementing fine-grained access control strategies within a Windows Server environment. By assigning permissions to a Domain Local Group rather than directly to individual user accounts, administrators can efficiently manage user access to resources. For example, if a group of users needs access to a specific folder, permissions can be assigned once to the Domain Local Group, simplifying the process of updating access as users join or leave the organization.
Scenario-Based Applications
- File Server Access: Create a Domain Local Group for each department requiring access to shared folders on a file server. Assign the necessary permissions to these groups, and then add users to the groups based on their departmental affiliation.
- Application Access: For applications that support Windows integrated authentication, use Domain Local Groups to manage access rights. This method is particularly useful for applications hosted within the domain that require controlled access.
- Cross-Domain Resource Access: In environments with multiple domains, use Domain Local Groups in conjunction with Global Groups for efficient access management. Place users in Global Groups within their respective domains, and then include these Global Groups in the Domain Local Group associated with the resource. This setup streamlines cross-domain access without compromising the granularity of permissions.
4. Integrating Domain Local Groups Across Trust Boundaries
Understanding Trust Relationships
Trust relationships in Active Directory are foundational links that allow separate domains to recognize each other’s user authentication, essentially saying one domain trusts the other to authenticate its users. These relationships can be one-way or two-way, providing flexibility in how resources and access are managed across domains. Trusts enable a user or group in one domain to access resources in another, paving the way for seamless cross-domain collaboration and resource sharing.
- Types of Trusts: Several trust types exist, including external, forest, shortcut, and realm trusts, each serving different integration and access needs between Windows and non-Windows environments.
- Transitive vs. Non-Transitive: Trusts can also be classified as transitive, where trust automatically extends to all domains within a forest, or non-transitive, limiting trust to two specific domains.
Managing Access in Multi-Domain Environments
In environments where resources span across multiple domains, Domain Local Groups become instrumental in managing access efficiently. Leveraging trust relationships, administrators can create access control strategies that are both scalable and secure.
- Using Global and Universal Groups: To manage access across domains, administrators should add users to Global Groups in their respective domains. These Global Groups can then be placed into Universal Groups (if the scope of resource access extends across the forest) or directly into Domain Local Groups (if access is confined to specific domains) where the resources reside. This strategy, known as AGDLP (Accounts, Global, Domain Local, Permissions), minimizes the complexity of access management in multi-domain scenarios.
- Cross-Domain Resource Access: For resources that users across different domains need to access, Domain Local Groups in the resource domain can be assigned permissions to these resources. Users from other domains, once part of the appropriate Global or Universal Groups, can access these resources without direct individual permissions, streamlining the access management process.
- Trust Planning and Management: Effective integration of Domain Local Groups across trust boundaries requires careful planning and management of trust relationships. Administrators must ensure that trusts are correctly configured to support the intended access patterns and that trust relationships are monitored and maintained to reflect changes in the organizational structure or security policies.
- Security Considerations: When integrating Domain Local Groups across domains, consider the security implications of extending trusts. Ensure that trusts are established only as necessary and that permissions are granted following the principle of least privilege to minimize potential security risks.
By understanding and effectively managing trust relationships and access controls in multi-domain environments, administrators can leverage Domain Local Groups to facilitate secure and efficient access to resources, regardless of where they or the users reside. This strategic approach to access management underscores the importance of Domain Local Groups in complex Active Directory infrastructures, enabling organizations to maintain a high level of security and operational efficiency across their networked environments.
5. References
Books:
- “Active Directory Administrator’s Pocket Consultant” by William R. Stanek
- “Mastering Active Directory – Design, Deploy, and Protect Active Directory Domain Services for Windows Server 2022“, 2021, by Dishan Francis.
Suggested Reading:
- “Active Directory Users and Computers“, by Network Encyclopedia.
- “How To Configure Group Policies to Set Security for System Services“, by Microsoft Learn.
- “Active Directory Domain Services Overview“, by Microsoft Learn.