The Editorial Team is a collective of technology enthusiasts, computer network engineers, and industry professionals dedicated to creating meticulously curated content for a diverse readership. With a combined experience spanning several decades, our team distills complex technology topics into clear, informative articles. Whether it’s networking fundamentals, cutting-edge AI insights, or in-depth guides on blockchain technology, the Editorial Team strives to provide reliable information that advances the understanding of technology for everyone from students to seasoned professionals.

Editorial Team’s mission
The Editorial Team’s mission extends beyond mere reporting; we aim to be the architects of understanding, constructing bridges over the rivers of jargon and complexity. From the foundational bricks of networking to the ever-evolving skies of cloud computing, we guide you through the technological labyrinth.
We take pride in our meticulous attention to detail and our unwavering commitment to accuracy, ensuring that each piece of information is a thread in the vast tapestry of technological knowledge. As we chart the course through the evolving landscape of technology, we invite our readers to join us on this exhilarating journey of discovery and growth. Together, we not only explore the current terrain of technology but also anticipate the horizons of tomorrow’s innovations.
Our Latest Articles
-
Deep Learning
Dive into the world of deep learning, the AI marvel powering today’s tech wonders. Explore its mechanisms, history, and transformative potential.
-
Group Policy Object (GPO)
Unravel the intricacies of Group Policy Object (GPO) within Windows Active Directory. Dive deep into its functionality and its pivotal role in AD management.
-
Transformers in AI: Decoding the Revolution
Dive into the intricacies of Transformer architectures—understand their rise, relevance, and ripple effect in the AI realm.
-
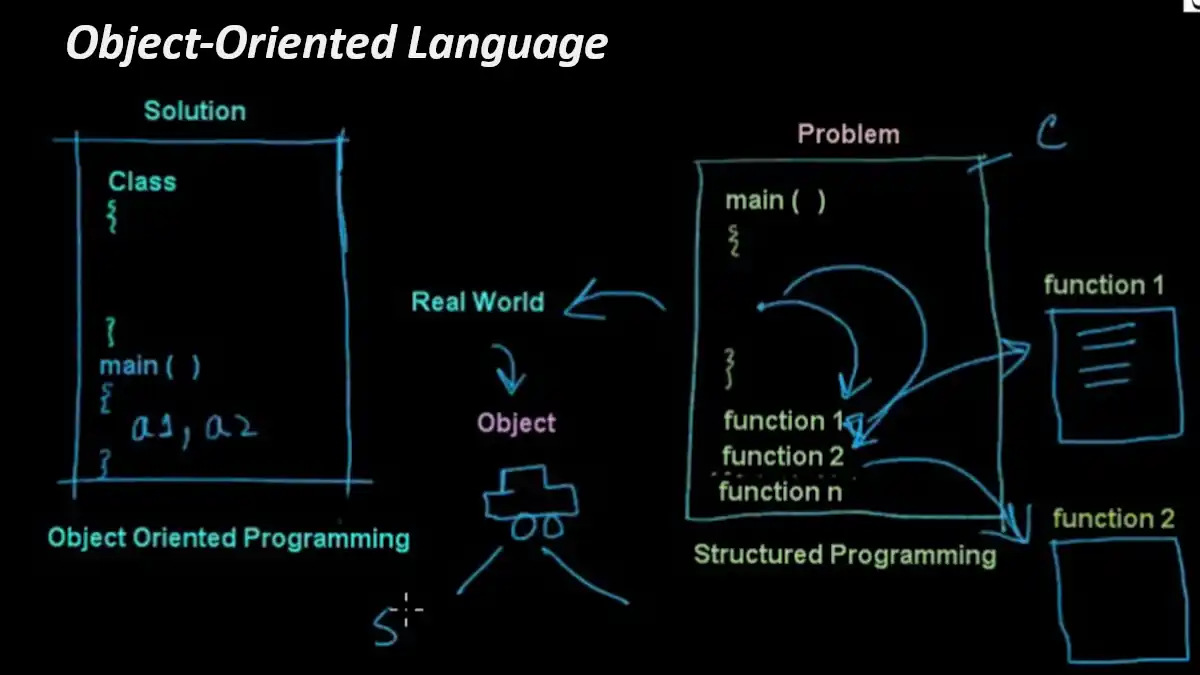
Object-Oriented Language (OOL)
Dive deep into the world of object-oriented programming, unlocking the secrets behind this popular paradigm and its revolutionary impact.
-
Paradox: The Database Titan of Yesteryears
Journey back in time to understand Paradox, a monumental player in the database management realm. Dive deep into its legacy, influence, and evolution.
-

Unraveling Identity Provider: Securing Digital Realms
Dive deep into the world of Identity Providers (IdPs) – the unsung heroes of digital security. Understand their crucial role in the cybernetic tapestry.
-
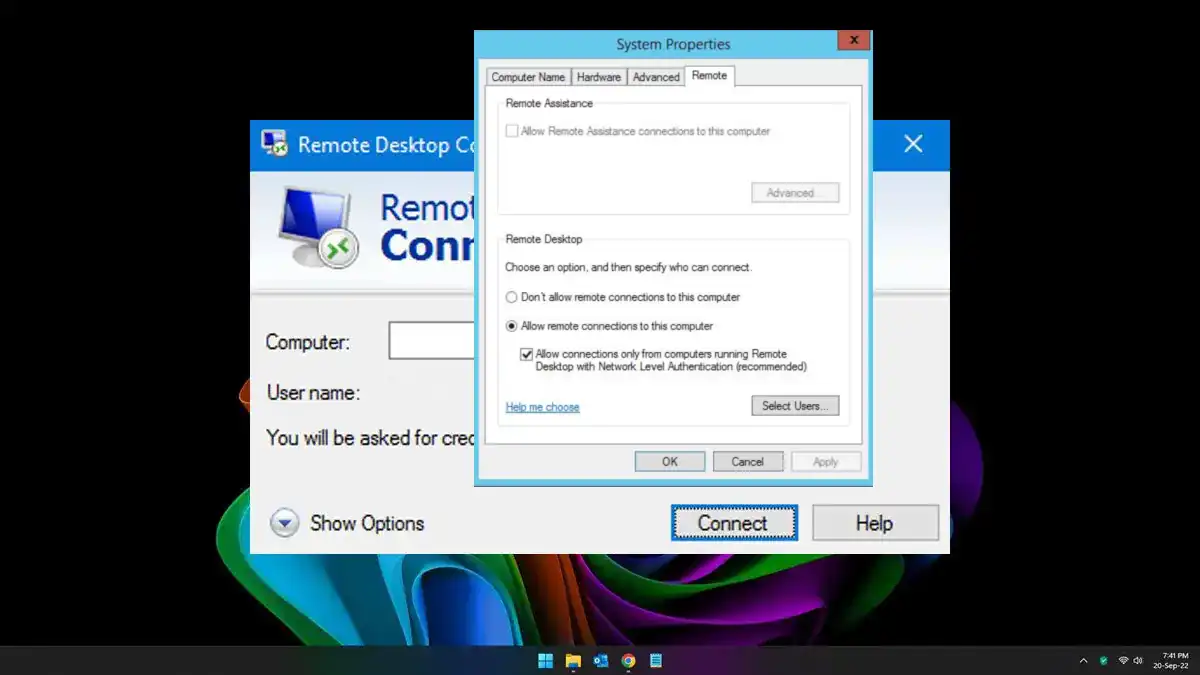
Network Level Authentication (NLA): Securing Connections
Don’t miss this beginner-friendly guide to understanding the mechanism of Network Level Authentication (NLA).
-
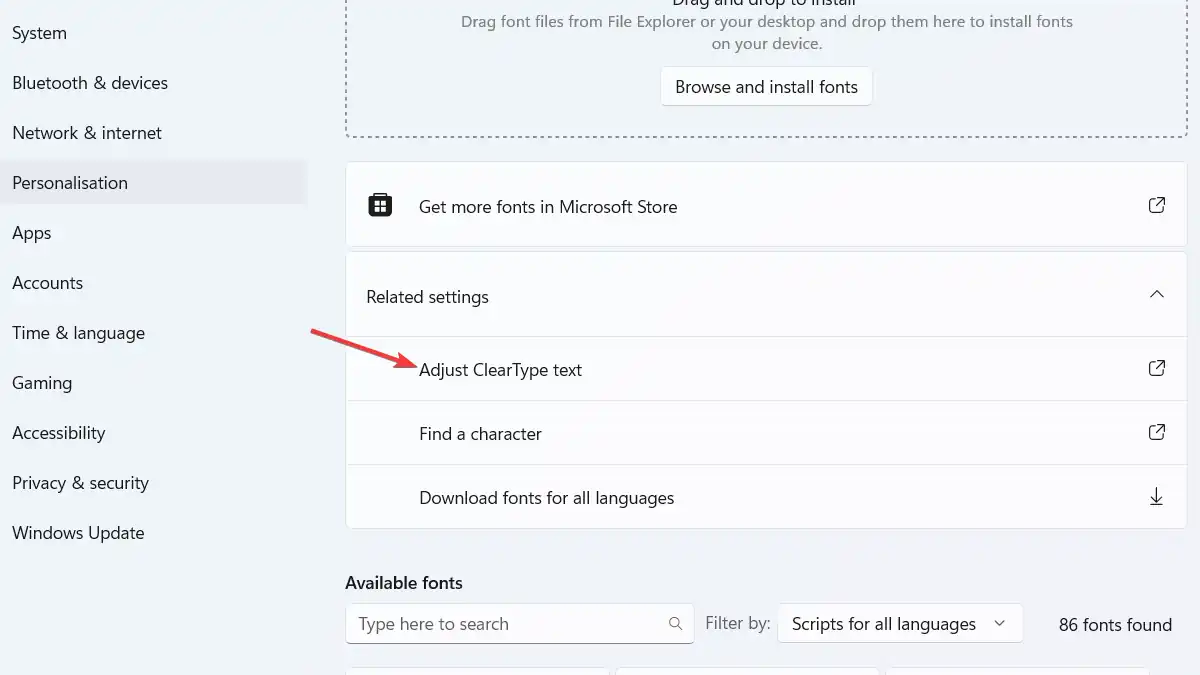
Demystifying ClearType: Microsoft’s Answer to Crisp and Clear Text
Don’t miss this easy-to-understand guide on Microsoft’s ClearType technology for enhanced on-screen text readability.
-

Guarding the Fortress: Understanding Sensitive Personal Information (SPI)
Dive into the world of Sensitive Personal Information (SPI), unraveling its types and importance. Learn why SPI is the treasured fortress in the digital age that demands steadfast guarding.
-

Mastering the Art of Crafting a Request for Proposal
Demystifying the intricacies of a Request for Proposal (RFP), this guide serves as a comprehensive beacon for IT professionals.
-
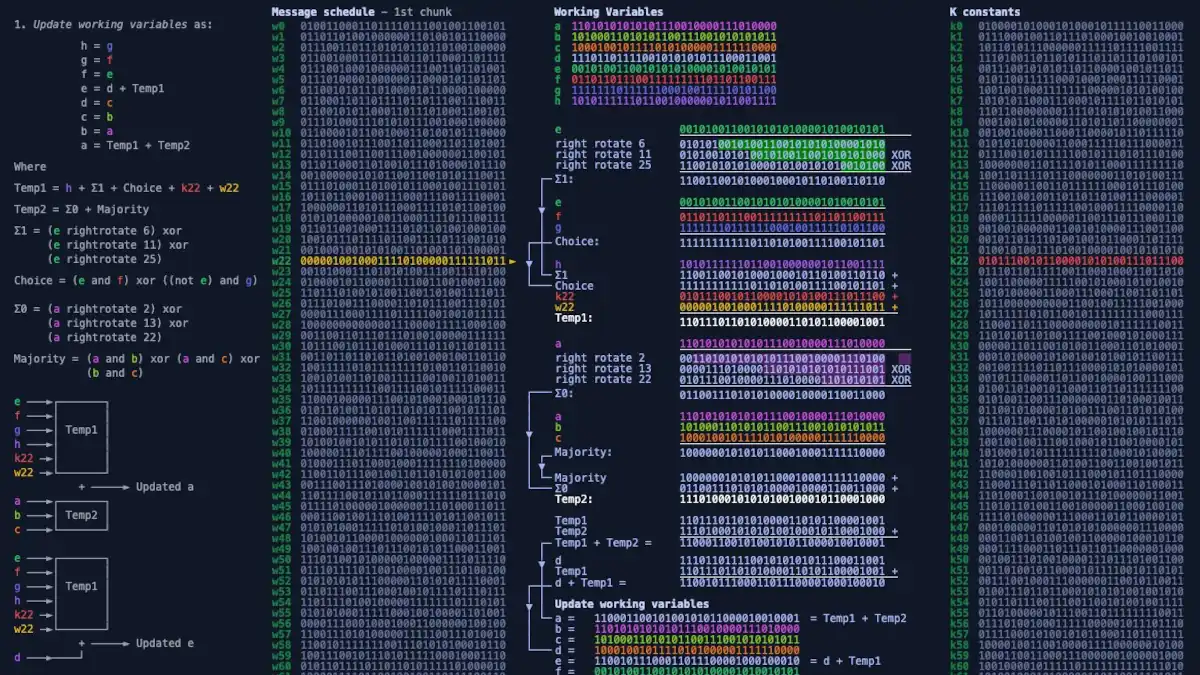
SHA-256 Unmasked: Deciphering Cryptographic Hash Functions
Unveil the world of cryptographic hash functions as we break down SHA-256. Understand its vital role in ensuring data integrity and security in the digital realm.