Trivial File Transfer Protocol (TFTP) is a simple, UDP-based protocol designed for quick file transfers within a network. Predominantly used in situations where speed and simplicity are prioritized over security, such as booting network devices or transferring configuration files, TFTP stands out for its minimalistic approach.
In this article, we delve into TFTP’s workings, its implementation across different operating systems, and its practical applications in modern network environments. Discover the nuances of TFTP’s protocol structure, error handling, and the security considerations essential for network professionals.
Table of Contents:
- What is TFTP?
- How it Works
- TFTP Implementation
- Modern Applications of TFTP
- Technical Aspects of TFTP
- Conclusion
- References
1. What is TFTP?
TFTP is an abbreviation for Trivial File Transfer Protocol, a TCP/IP file transfer protocol. TFTP differs from the popular File Transfer Protocol (FTP) in that it does not support any form of authentication, focusing on minimalism for ease of implementation and efficient operation. TFTP is defined in Request for Comments (RFC) 1350 (see link in references).
2. How It Works
TFTP copies files to and from remote hosts by using the User Datagram Protocol (UDP), ensuring fast data transmission without the overhead of extensive error checking. The remote host must be running the TFTP service or daemon for the TFTP client to be able to communicate with it. In UNIX networks that use diskless workstations and the bootstrap protocol (BOOTP), TFTP is usually used to download the boot disk image from the BOOTP server to the workstation.
3. TFTP Implementation
Microsoft Windows
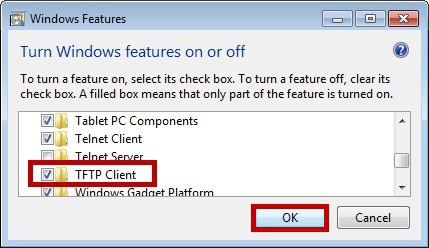
In Microsoft Windows environments, TFTP is not included as a built-in service. However, Windows does provide a TFTP client accessible via the command prompt. This client allows basic interaction with TFTP servers for file transfers. In more advanced versions like Windows 2000 and later, a TFTP server component, known as the Trivial File Transfer Protocol Daemon (TFTPD), is available. This server functionality is particularly useful in scenarios like network-based installations and remote booting services.
UNIX and Linux
In UNIX and Linux systems, TFTP is more deeply integrated. It’s commonly used for booting diskless workstations, especially in environments where the Bootstrap Protocol (BOOTP) or its successor, the Dynamic Host Configuration Protocol (DHCP), is employed. The TFTP server daemon in these systems enables the transfer of boot files and other configurations to diskless clients, facilitating network-based booting and initial setup processes.
4. Modern Applications of TFTP
While TFTP’s simplicity limits its application in general-purpose file transfers, especially where security and robust error handling are required, it remains relevant in specific use cases:
- Network Booting: TFTP is crucial in environments where diskless workstations or thin clients are used. It allows for the seamless transfer of boot files and essential configurations, enabling these systems to boot from a network server.
- Network Configuration and Management: In many networking devices like routers and switches, TFTP is used to transfer configuration files and firmware updates. Its simplicity allows for easy integration into these devices’ firmware.
- Simplified File Transfers in Constrained Environments: In scenarios where the network infrastructure is limited, and the overhead of full-fledged protocols like FTP is undesirable, TFTP provides a lightweight alternative for basic file transfer needs.
5. Technical Aspects of TFTP
Protocol Structure
TFTP operates using a client-server model and employs a simple request-response mechanism. It utilizes UDP, which makes it faster but less reliable than TCP-based protocols. Files are transferred in blocks of 512 bytes. The transfer is considered complete when a block less than 512 bytes is sent, indicating the end of the file.
Error Handling
TFTP’s error handling is rudimentary. It includes basic mechanisms to deal with issues like file not found, access violation, or disk full. Errors typically result in the termination of the connection, with an error packet sent to the counterpart. This simplicity in error handling aligns with TFTP’s design philosophy of minimalism but also underscores its limitations for more complex network tasks.
Security Considerations
TFTP lacks built-in security features like authentication or encryption. This design choice prioritizes speed and simplicity but also makes TFTP unsuitable for transferring sensitive data over unsecured networks. In modern network environments, TFTP is often used in controlled settings or behind firewalls to mitigate security risks.
6. Conclusion
TFTP stands out for its simplicity and efficiency in specific scenarios, particularly in network booting and configuration tasks. Its minimalistic design, while limiting in terms of features and security, offers a lightweight solution for basic file transfer needs in certain network environments. Understanding its operation, applications, and limitations is essential for network professionals, especially those managing legacy systems or specific types of network infrastructure.