Category: A to Z
-

Common Criteria for Information Technology Security Evaluation (CC): Certifying Computer Security
In this article, we will delve into the significance of the Common Criteria, its global adoption, and the entities that rely on it for securing their digital assets. Additionally, we will touch upon its historical predecessor, the C2 security standard, to highlight the evolution of security evaluations in the IT realm.
-

SPF Records: Ensuring Your Emails Land Where They Should
Discover how to craft, validate, and implement SPF records to protect your domain, prevent email spoofing, and ensure your messages reach their intended destinations. With practical insights and expert advice, this article is an indispensable resource for anyone looking to bolster their email security and deliverability.
-

Virtual Hosting Unveiled: Revolutionizing Modern Networking
In this article we will unravel the various facets of virtual hosting. We’ll explore what it means, its different forms, and how it’s transforming the networking landscape.
-
UEFI: Unified Extensible Firmware Interface
In this article, we’ll explain what UEFI (Unified Extensible Firmware Interface) is, how it’s revolutionizing our computers, and why it’s become an indispensable part of modern computing.
-
Exploring the Session Layer in the OSI Model
Delve into the Session Layer of the OSI Model: understand its functions, protocols, and impact on network communication in this detailed exploration.
-

Windows Fax: Bridging the Gap Between Fax and Digital Communication
Think faxing is old-school? Think again! Dive into our guide on Windows Fax – it’s like sending a text from the past, but cooler!
-
MAC Layer: The Backbone of Network Communication
Unravel the complexities of the Medium Access Control Layer in network communication, its functionalities, and its pivotal role in the OSI model.
-

PowerShell Basics: Streamline Your Workflow Today
Explore the basics of Windows PowerShell, its features, and its role in modern computing in this comprehensive beginner’s guide.
-
Brute-Force Attack
Learn what a brute-force attack is, real-world examples, and foolproof strategies to protect yourself. Your ultimate guide to understanding and combating this pervasive cyber threat.
-
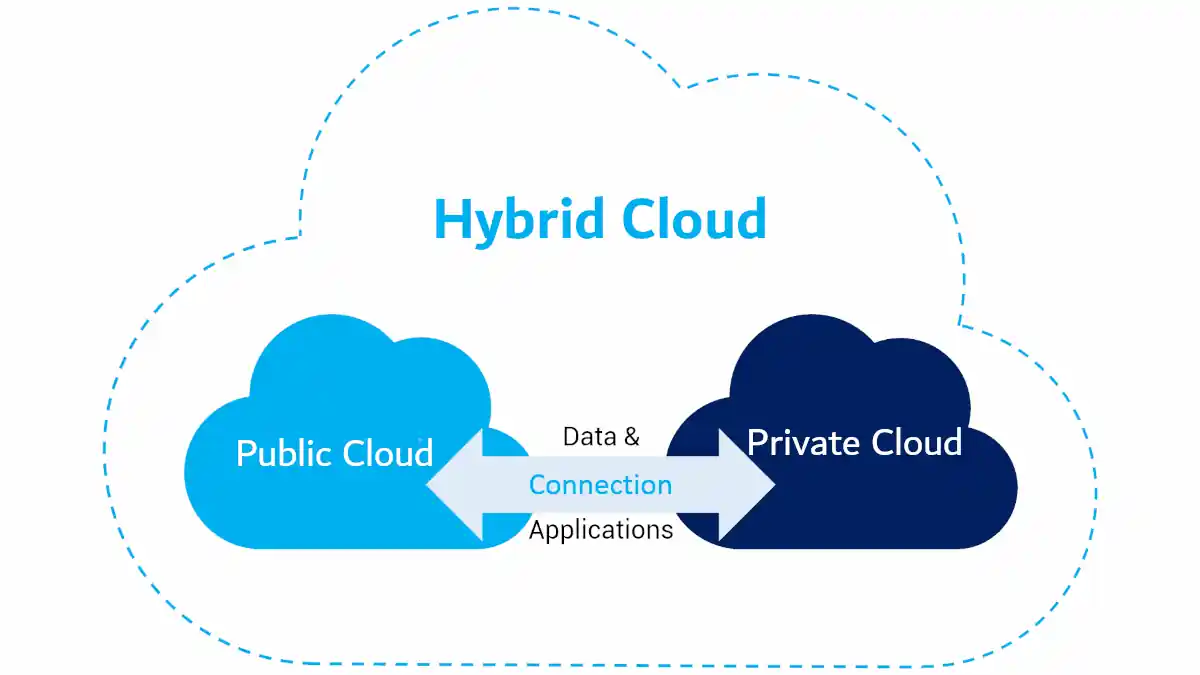
The Future of Hybrid Cloud: Integrating AI for Optimized Networking
Explore the future of Hybrid Cloud as we delve into integrating AI for optimized networking. Discover how intelligent systems can revolutionize cloud management and security.