Category: A to Z
-

Phishing Exposed: Understanding Digital Deception
Delve deep into the dark world of Phishing, as we unravel the mechanics of this notorious cyber menace, empowering you to navigate the digital realm securely
-
Neuromorphic Design: Bridging Brains and Bytes
Delving into neuromorphic design—the frontier where neuroscience meets artificial intelligence, offering groundbreaking tech advancements
-

Xerox’s Palo Alto Research Center (PARC)
Discover the epicenter of innovation—Xerox’s Palo Alto Research Center (PARC). Dive into its legacy of groundbreaking discoveries that reshaped technology.
-
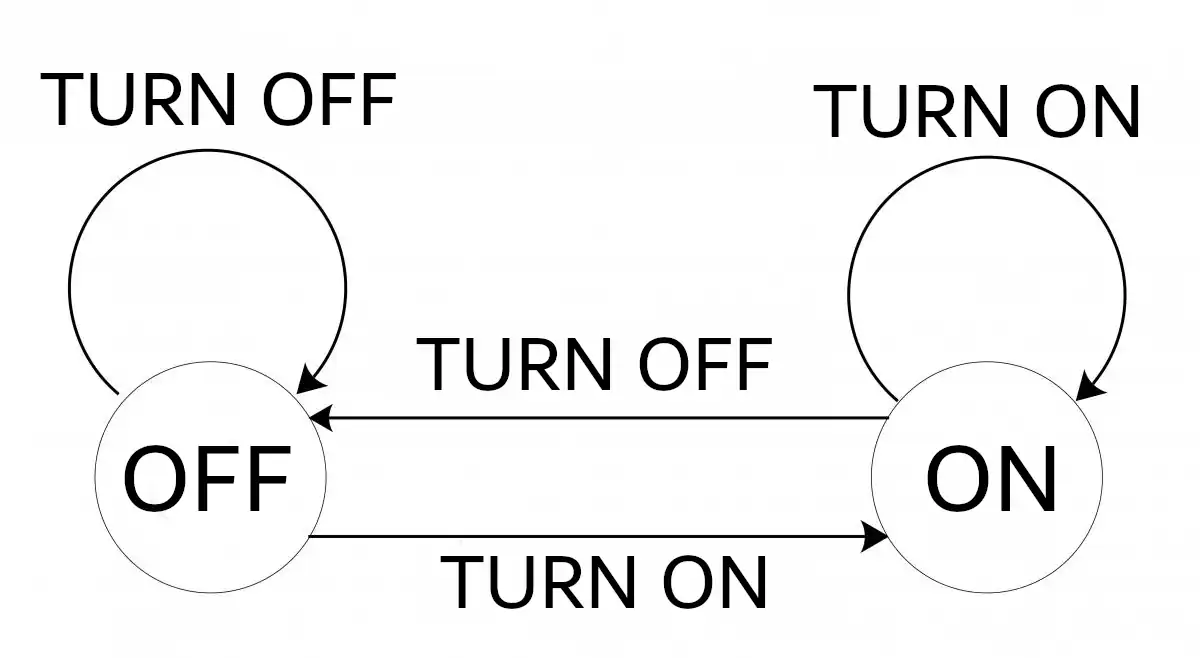
Decoding Finite State Machines in AI
Dive deep into the realm of computer networking and AI as we unravel the intricate fabric of Finite State Machines. An essential read for every tech enthusiast!
-

Graphic User Interface (GUI)
Embark on a journey to explore the Graphic User Interface (GUI). Uncover its role in modern computing and its profound impact on user experience.
-
Deep Learning
Dive into the world of deep learning, the AI marvel powering today’s tech wonders. Explore its mechanisms, history, and transformative potential.
-
Group Policy Object (GPO)
Unravel the intricacies of Group Policy Object (GPO) within Windows Active Directory. Dive deep into its functionality and its pivotal role in AD management.
-
Transformers in AI: Decoding the Revolution
Dive into the intricacies of Transformer architectures—understand their rise, relevance, and ripple effect in the AI realm.
-
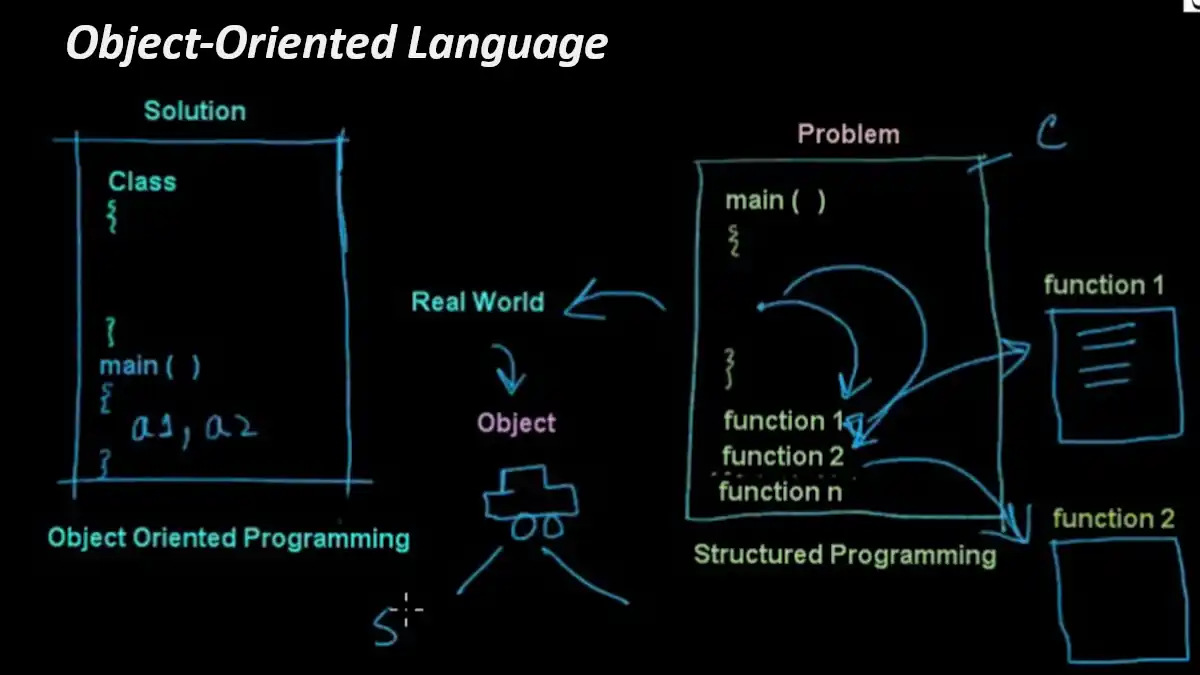
Object-Oriented Language (OOL)
Dive deep into the world of object-oriented programming, unlocking the secrets behind this popular paradigm and its revolutionary impact.
-
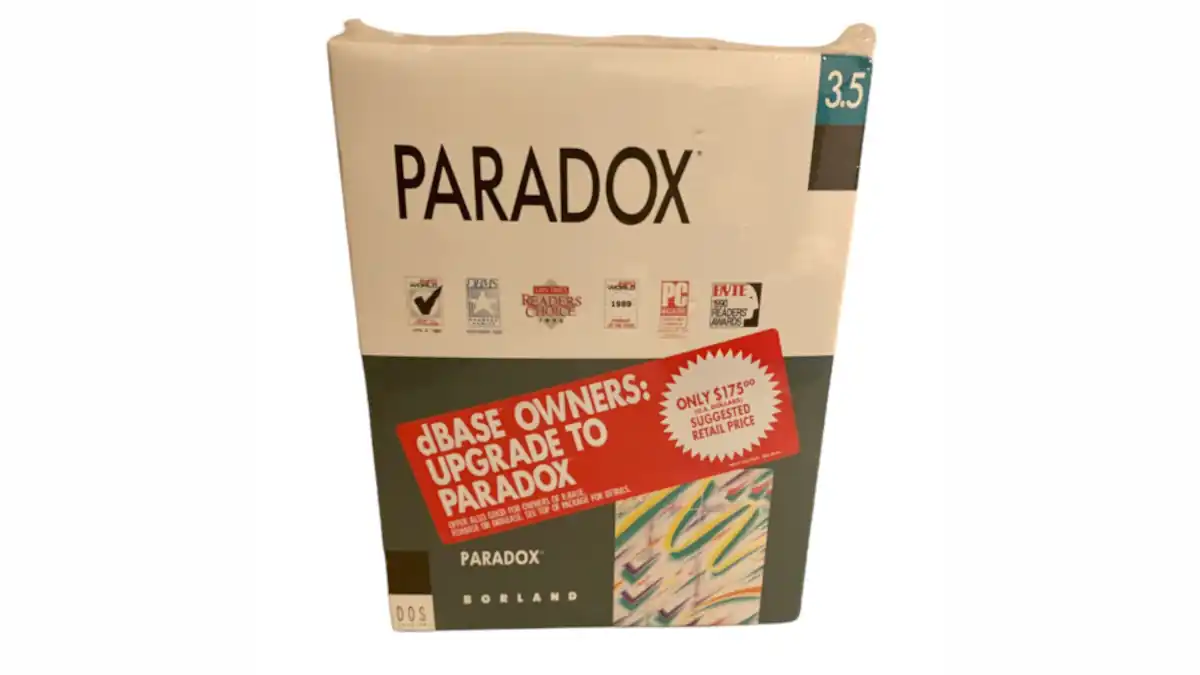
Paradox: The Database Titan of Yesteryears
Journey back in time to understand Paradox, a monumental player in the database management realm. Dive deep into its legacy, influence, and evolution.
-

Unraveling Identity Provider: Securing Digital Realms
Dive deep into the world of Identity Providers (IdPs) – the unsung heroes of digital security. Understand their crucial role in the cybernetic tapestry.
-
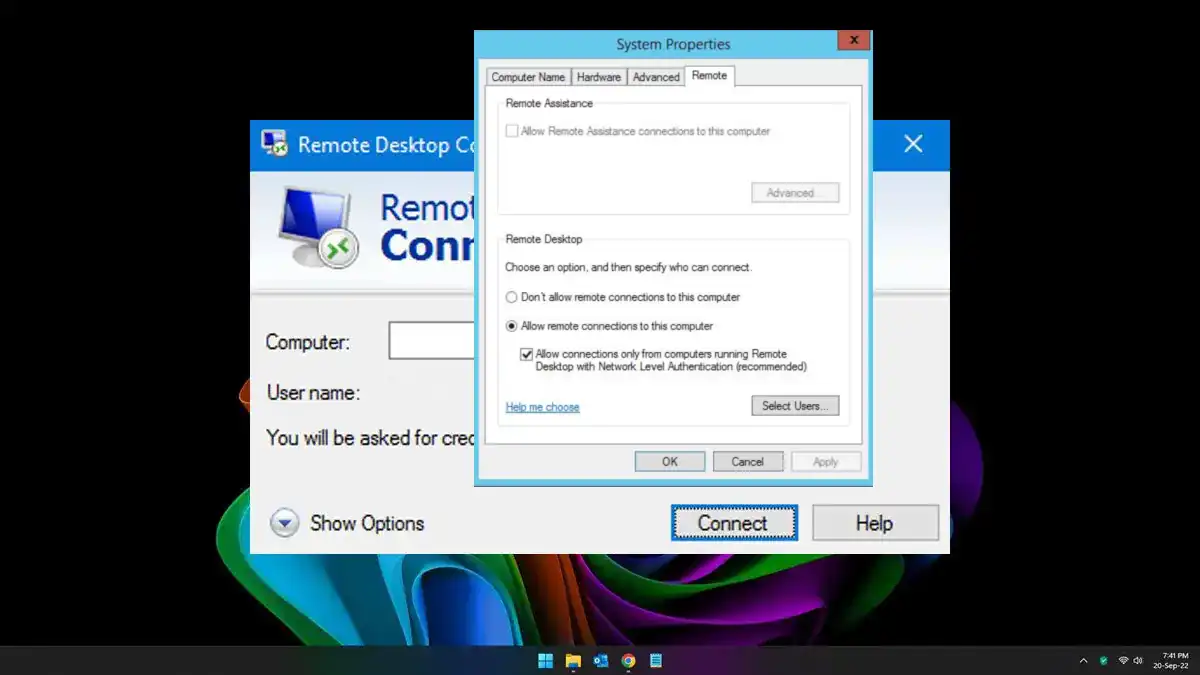
Network Level Authentication (NLA): Securing Connections
Don’t miss this beginner-friendly guide to understanding the mechanism of Network Level Authentication (NLA).