Category: A to Z
-
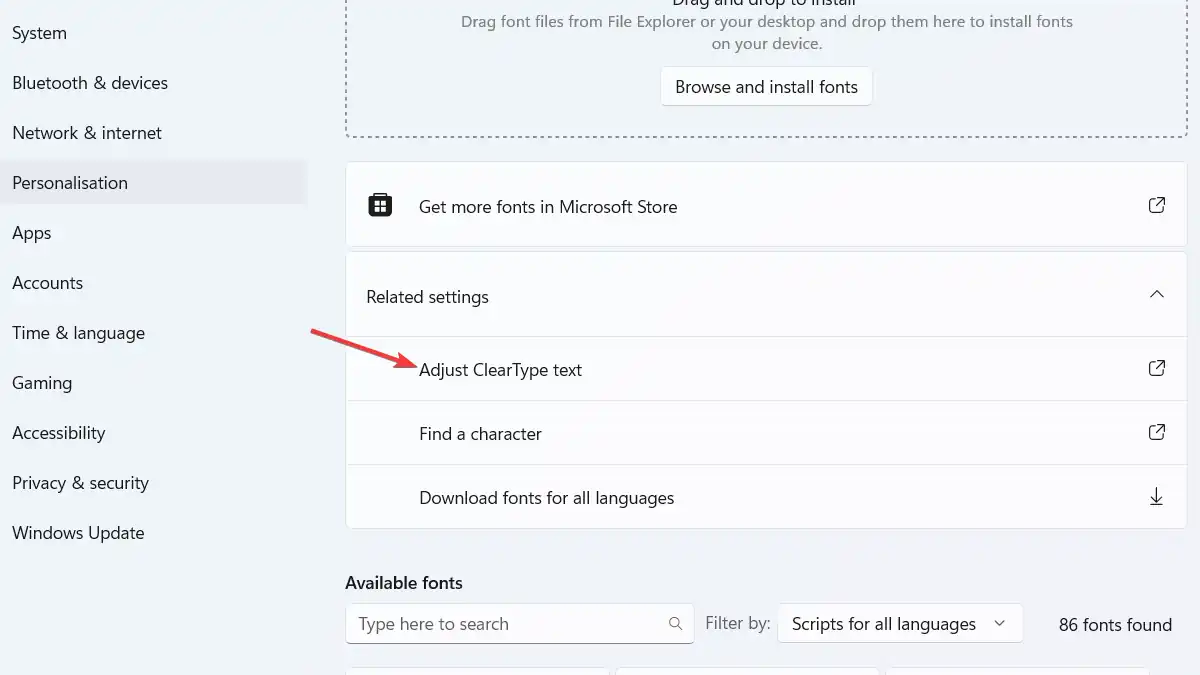
Demystifying ClearType: Microsoft’s Answer to Crisp and Clear Text
Don’t miss this easy-to-understand guide on Microsoft’s ClearType technology for enhanced on-screen text readability.
-

Guarding the Fortress: Understanding Sensitive Personal Information (SPI)
Dive into the world of Sensitive Personal Information (SPI), unraveling its types and importance. Learn why SPI is the treasured fortress in the digital age that demands steadfast guarding.
-

Mastering the Art of Crafting a Request for Proposal
Demystifying the intricacies of a Request for Proposal (RFP), this guide serves as a comprehensive beacon for IT professionals.
-
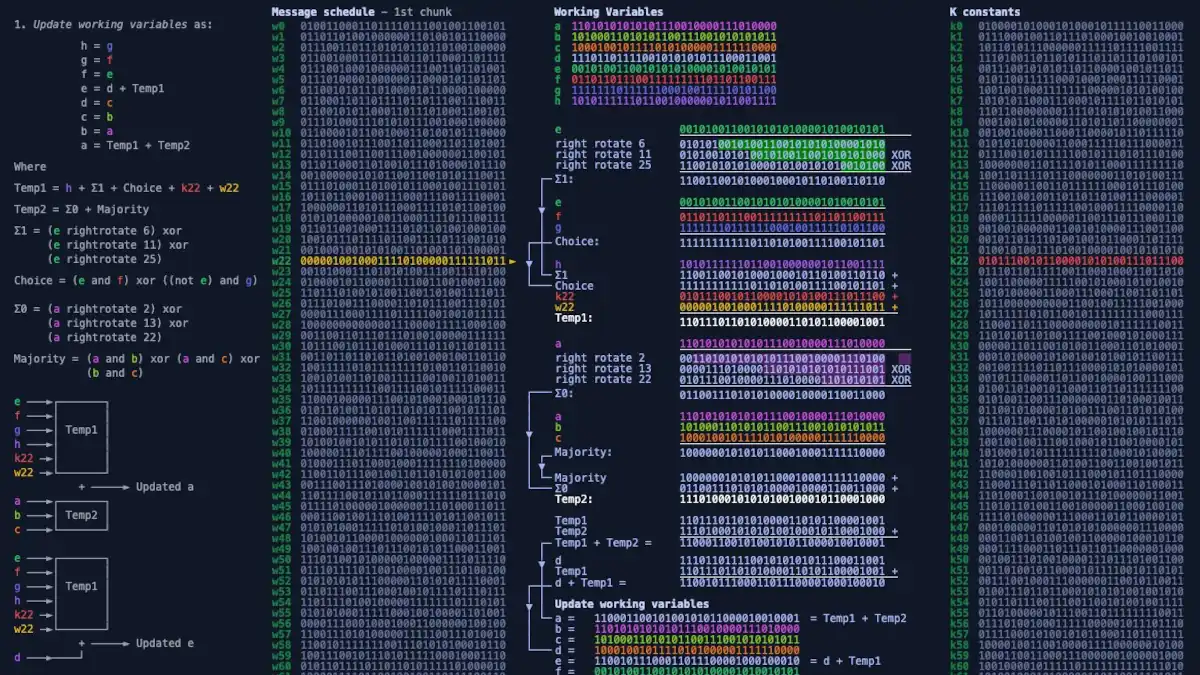
SHA-256 Unmasked: Deciphering Cryptographic Hash Functions
Unveil the world of cryptographic hash functions as we break down SHA-256. Understand its vital role in ensuring data integrity and security in the digital realm.
-
Quantum Computing Basics: Unraveling the Complexity and Limitations
In this article, we’re going to explore the basics of Quantum Computing and understand its limitations. Let’s also take a closer look at Qubits, the foundation of Quantum Computers. Step into a new era of network technology revolution. In this article Introduction The realm of Quantum Computing can seem like an intimidating jungle of complex…
-

The Weasel Effect: Solving One Problem Only to Create a Bigger One
Explore the Weasel Effect, a new concept highlighting how short-term solutions can lead to larger problems, and learn strategies for sustainable problem-solving.
-

Understanding Critical Data: Essential Aspects Exploration
Critical data refers to the essential information required for the successful operation of a business or organization.
-

Ashton-Tate: The dBase Creators
Ashton-Tate was a software company that was best known for developing the popular dBASE database application. It was founded in 1980 by Hal Lashlee and George Tate.
-

Unraveling the Threads of RTSP: The Pulse of Live Streaming
Decode the magic behind live streaming with RTSP! Explore the core of real-time multimedia transmission with our in-depth guide.
-
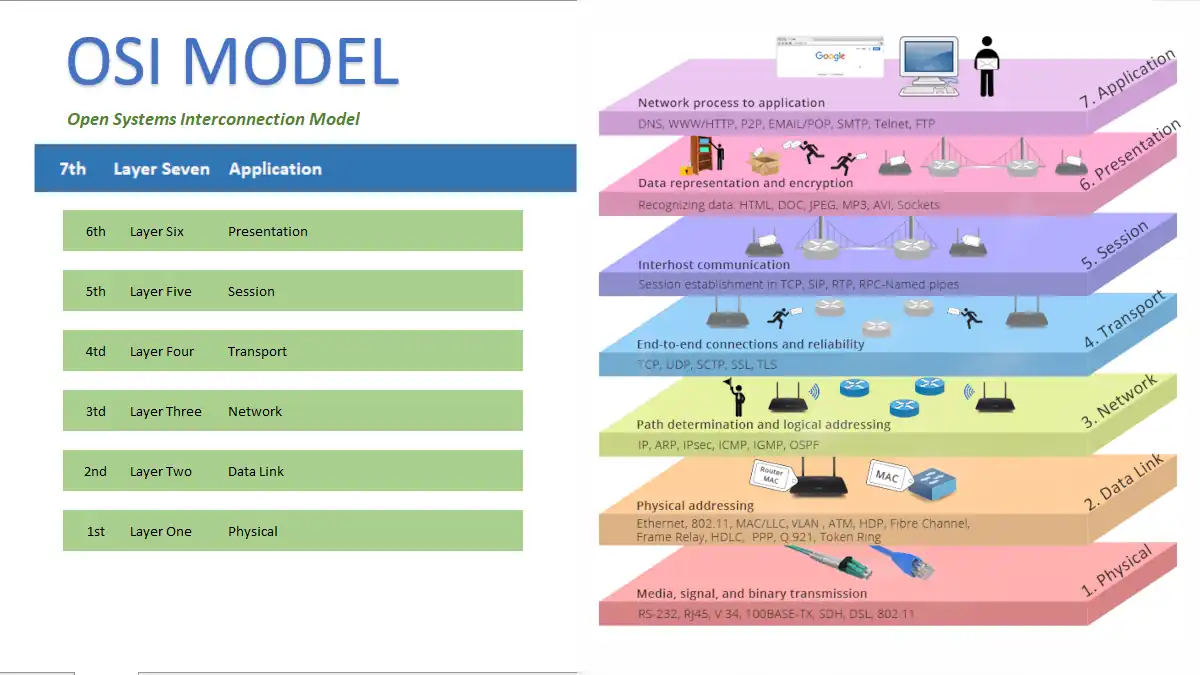
Mastering the Summit: Exploring the 7th Layer of the OSI Model
Dive into the intricacies of the 7th Layer of the OSI Model! Uncover its role, operations, and significance in network communication.
-
Round-Trip Time (RTT)
In the intricate domain of computer networking, Round-Trip Time, popularly known as RTT, plays an instrumental role.