Category: A to Z
-
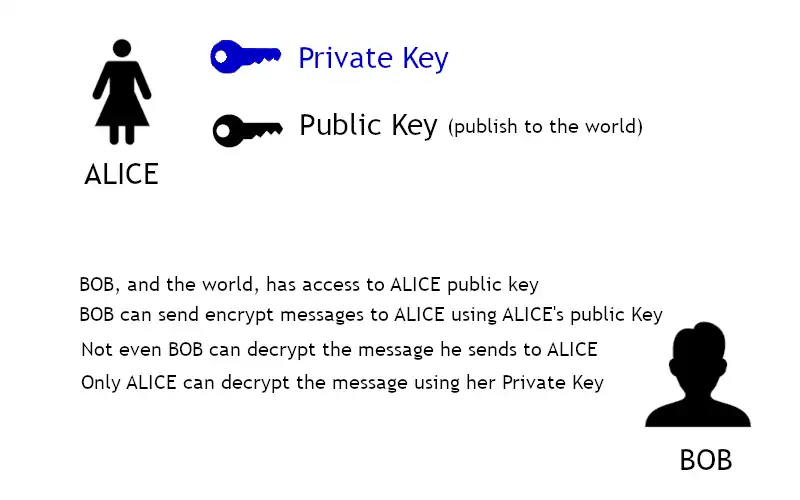
Asymmetric Encryption
Asymmetric encryption requires the use of two keys: a private key that is known only by its owner and a public key that is readily available to those who need to use it.
-
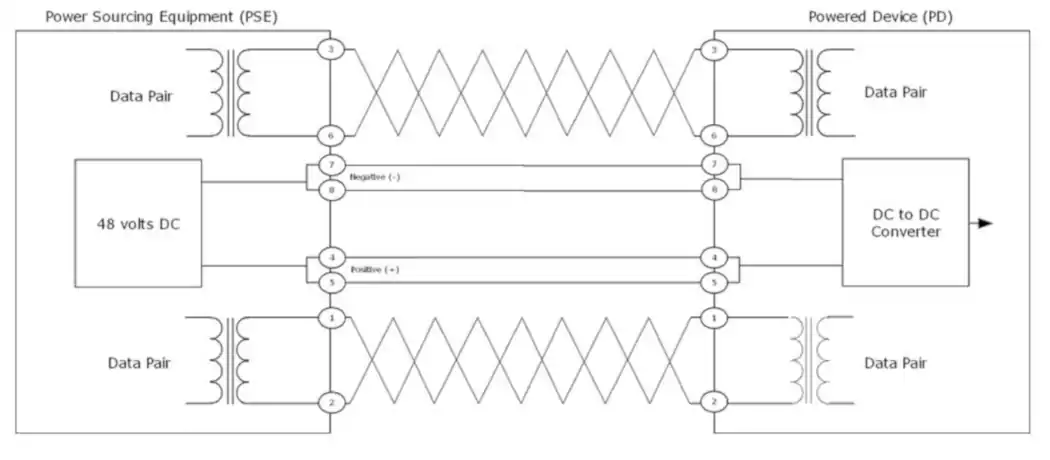
How Power Over Ethernet works – PoE Operations
Understanding how PoE works. The idle state and three operational states: detection, classification, and operation.
-
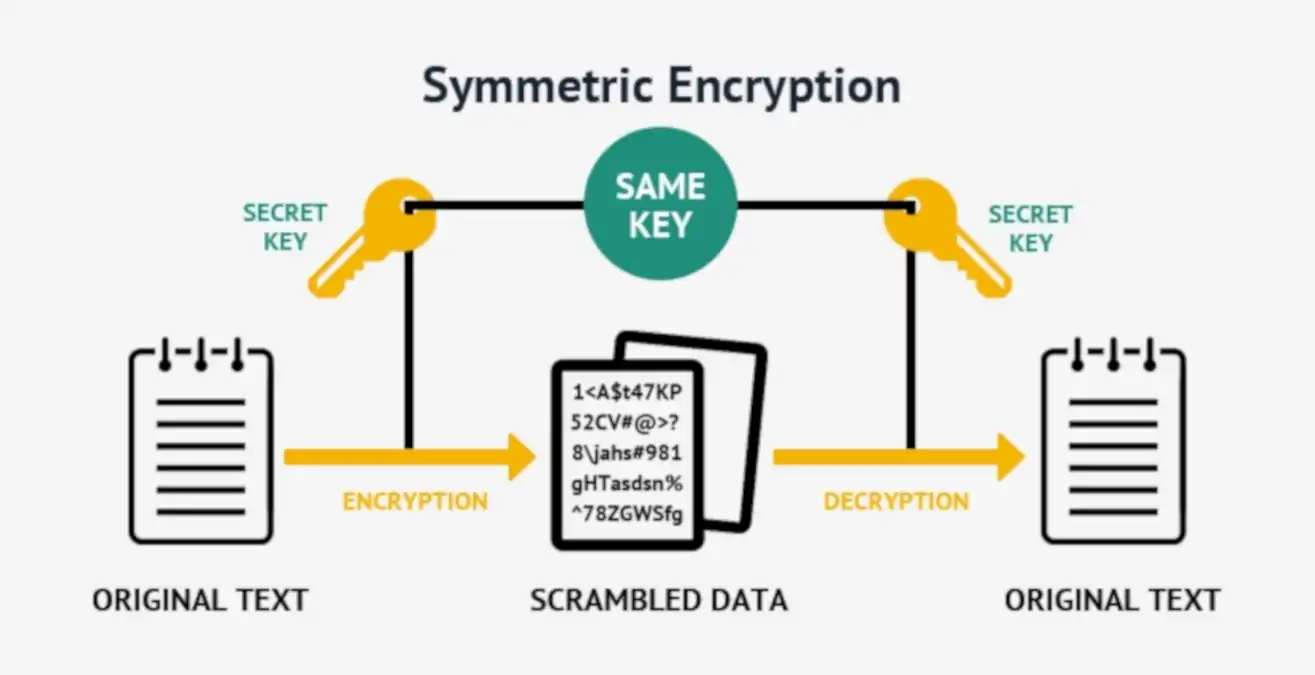
Symmetric Encryption
Symmetric encryption, or single-key encryption, is the most well-understood cryptography primitive.
-

PoE Device Roles and Type Parameters
For those who want to delve into the details of the Power over Ethernet technology, here we discuss PoE devices roles and type parameters.
-

History of Fiber Optics
It’s important to study the history of fiber optics to understand that the technology as it exists today is new and still evolving.
-
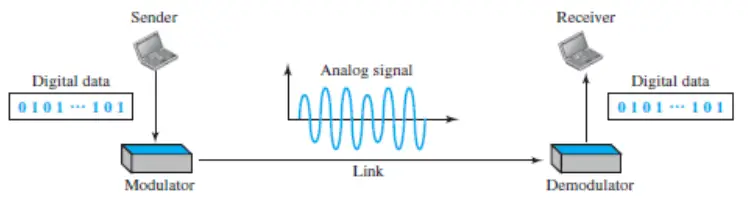
Digital-to-analog conversion
Digital-to-analog conversion is the process of changing one of the characteristics of an analog signal based on the information in digital data. Learn more…
-
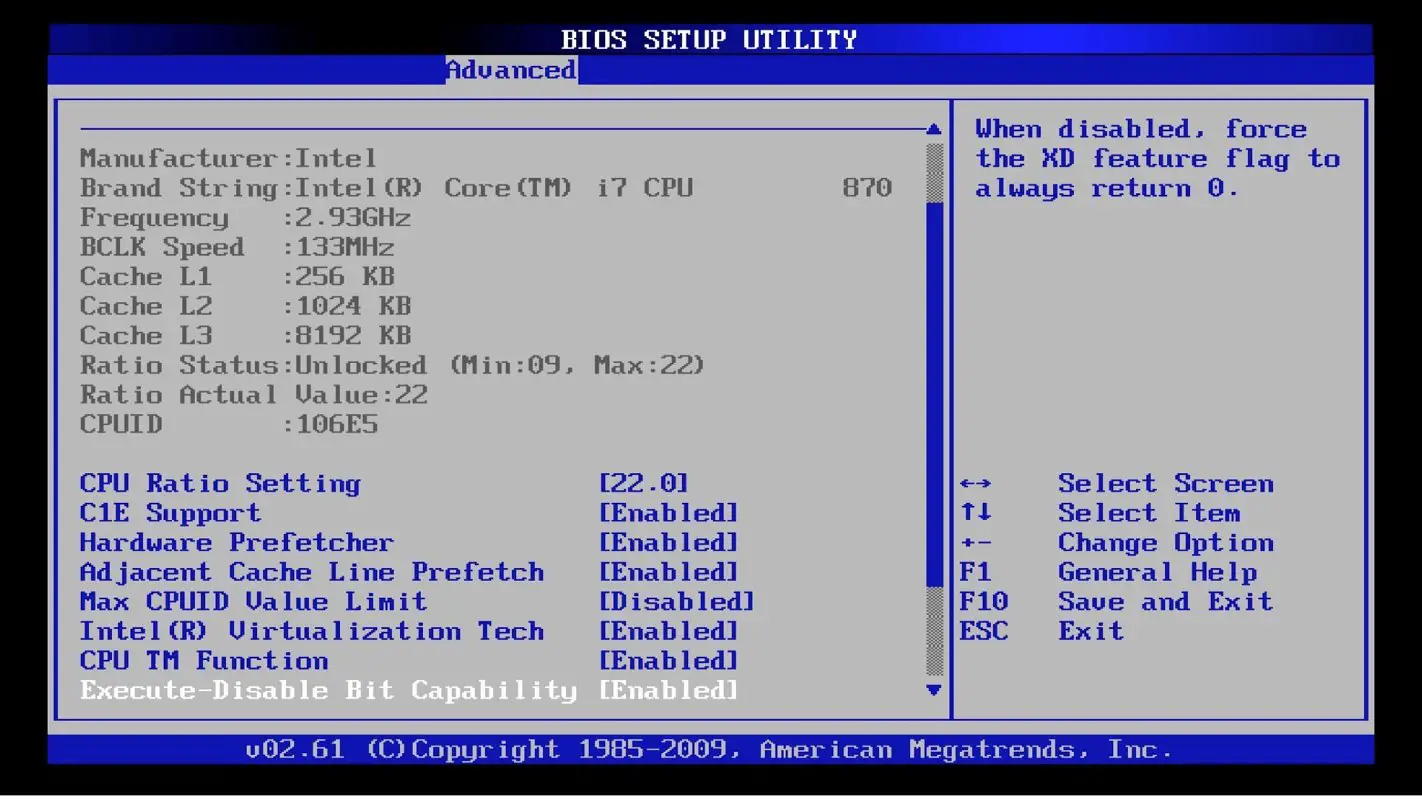
BIOS – Basic Input/Output System
BIOS is one key component of the computer motherboard. It stands for basic input/output system (BIOS).
-
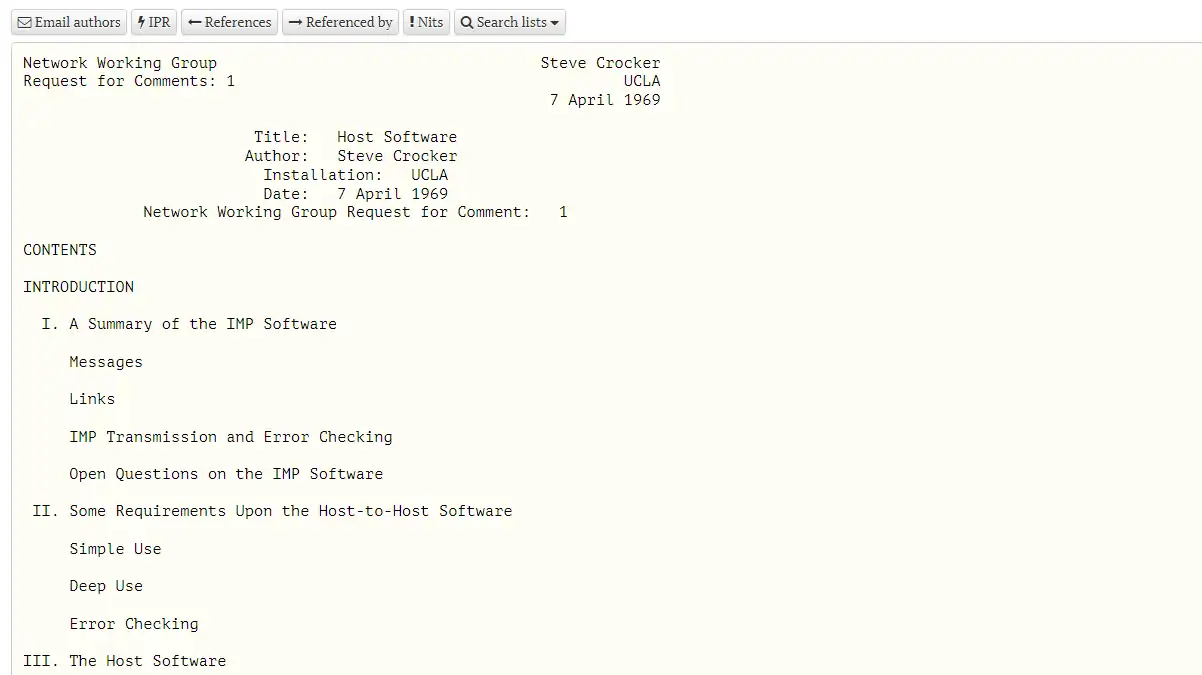
The First Request for Comments or RFC 1
On April 7, 1969, Steve Crocker a UCLA graduate student, wrote a technical document entitled “Host Software” and call that type of document “Request for Comments” to avoid sounding too declarative and to encourage discussion. Unlike the modern RFCs, the initial RFCs were actual requests for comments from the community.
-
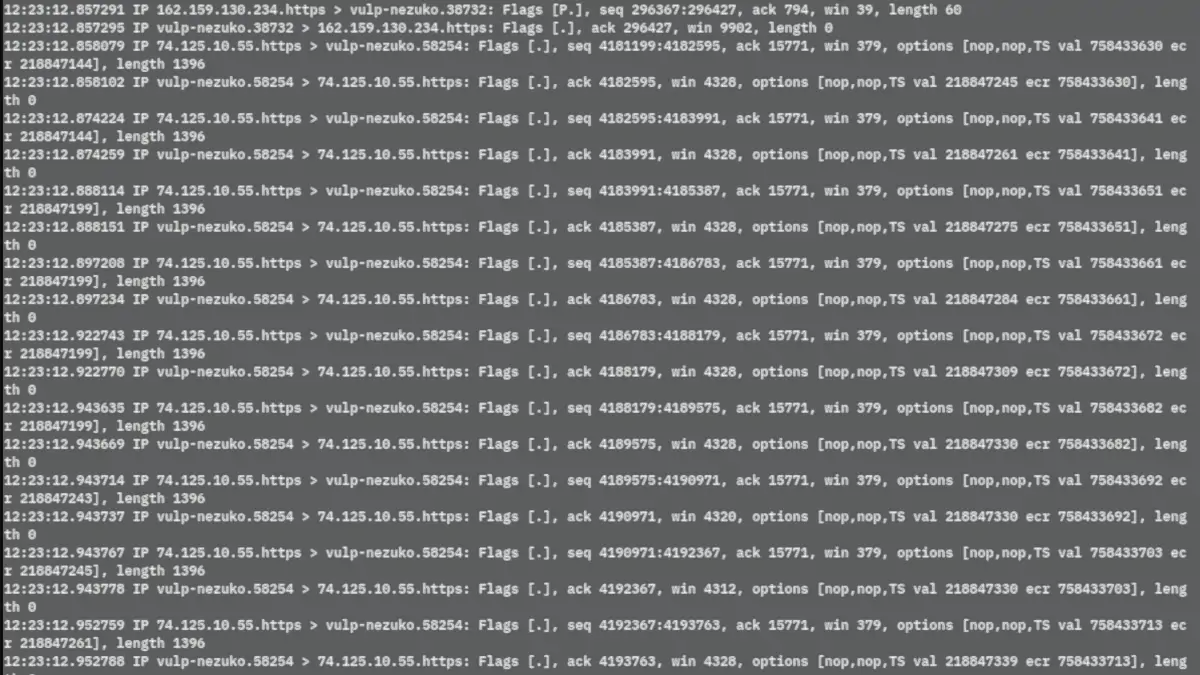
TCPdump Guide
In this article, we cover almost every aspect of the TCP packet capture and analysis tool called TCPdump. This is our TCPdump Guide.
-

What is the Role of Dynamic Address Assignment?
Over the last decades, we have witnessed tremendous growth in the size of networks. This growth has occurred in the geographic spread of the network, as well as an exponential rise in the number of nodes per network.
-

Importance of Cyber Security in the Digital Era
Cyber Security in the Digital Era: It is crucial to understand what we are exposed to online and how to protect ourselves from potential attacks.
-
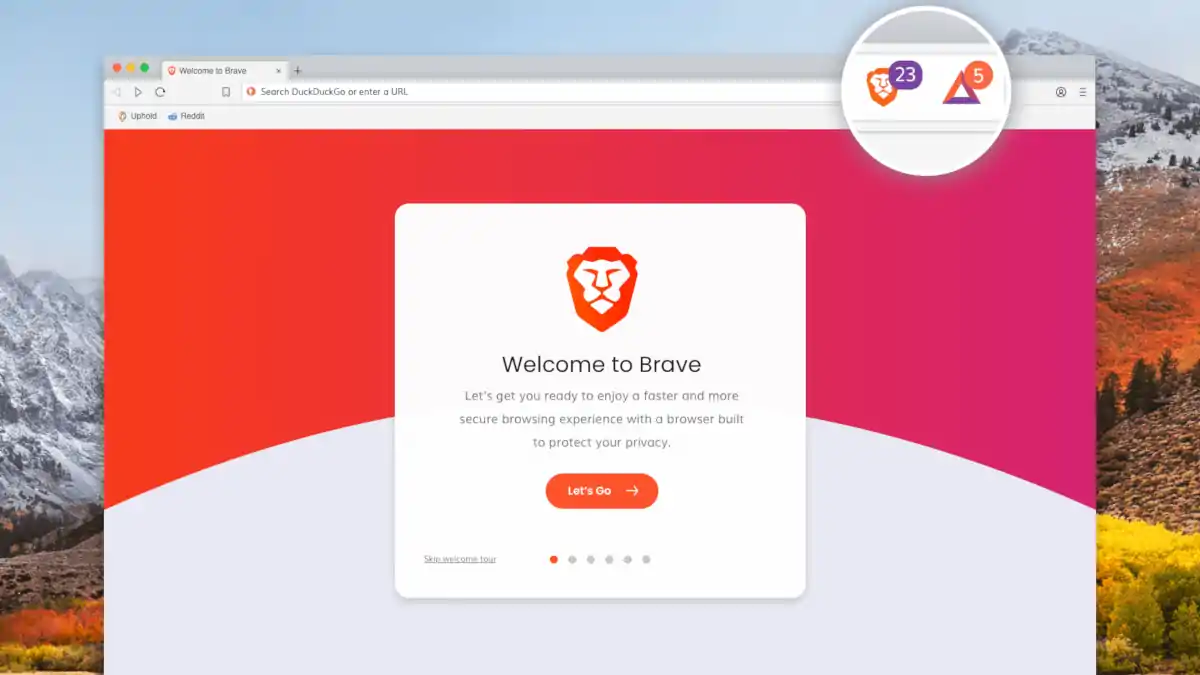
Entering the Brave (Browser) New World!
Brave browser arrived to change the way we surf the internet. In this article, we will explain what Brave browser is and how you can benefit from it.