The Editorial Team is a collective of technology enthusiasts, computer network engineers, and industry professionals dedicated to creating meticulously curated content for a diverse readership. With a combined experience spanning several decades, our team distills complex technology topics into clear, informative articles. Whether it’s networking fundamentals, cutting-edge AI insights, or in-depth guides on blockchain technology, the Editorial Team strives to provide reliable information that advances the understanding of technology for everyone from students to seasoned professionals.

Editorial Team’s mission
The Editorial Team’s mission extends beyond mere reporting; we aim to be the architects of understanding, constructing bridges over the rivers of jargon and complexity. From the foundational bricks of networking to the ever-evolving skies of cloud computing, we guide you through the technological labyrinth.
We take pride in our meticulous attention to detail and our unwavering commitment to accuracy, ensuring that each piece of information is a thread in the vast tapestry of technological knowledge. As we chart the course through the evolving landscape of technology, we invite our readers to join us on this exhilarating journey of discovery and growth. Together, we not only explore the current terrain of technology but also anticipate the horizons of tomorrow’s innovations.
Our Latest Articles
-

Common Security Threats in Computer Networks
In this article, we will explain the most common security threats in computer networks. This allows you to be aware of those threats.
-
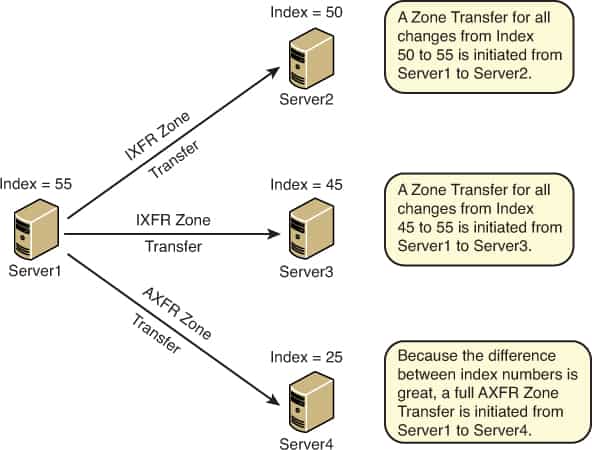
AXFR Request
AXFR Request is a type of Domain Name System (DNS) request in which a secondary DNS server requests the update of information from a master DNS server.
-
Power Over Ethernet (PoE)
Power over Ethernet (PoE) is an optional standard that provides direct current electrical power over Ethernet twisted-pair cabling. This makes it possible for an Ethernet switch port to provide both Ethernet data and the power needed to operate.
-
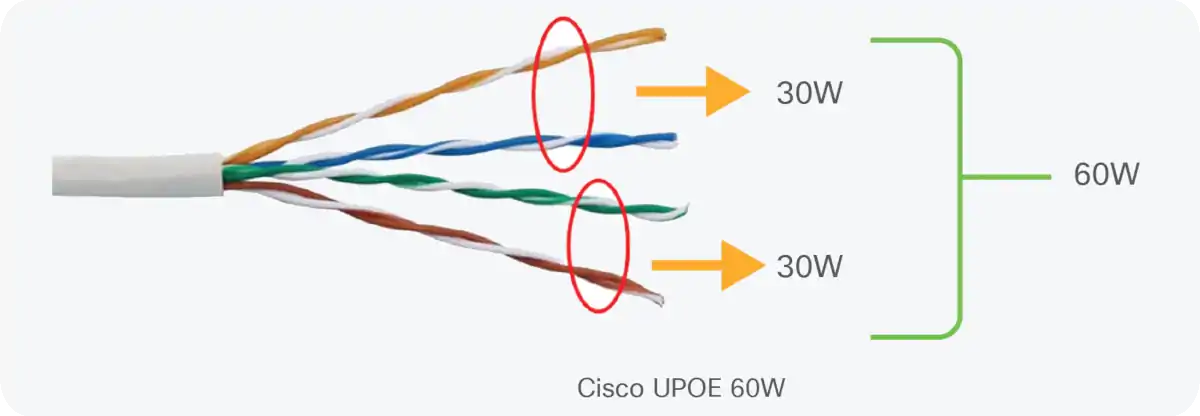
PoE Vendor Extensions to the Standard
After 802.3at made it possible to provide roughly 30 watts over two pairs of wires, it was a relatively straightforward process to extend the standard to provide power over four pairs simultaneously.
-

PoE Port Management
To manage these power loads, vendors of switches typically program the switches to provision power one port at a time, this is PoE Port Management.
-
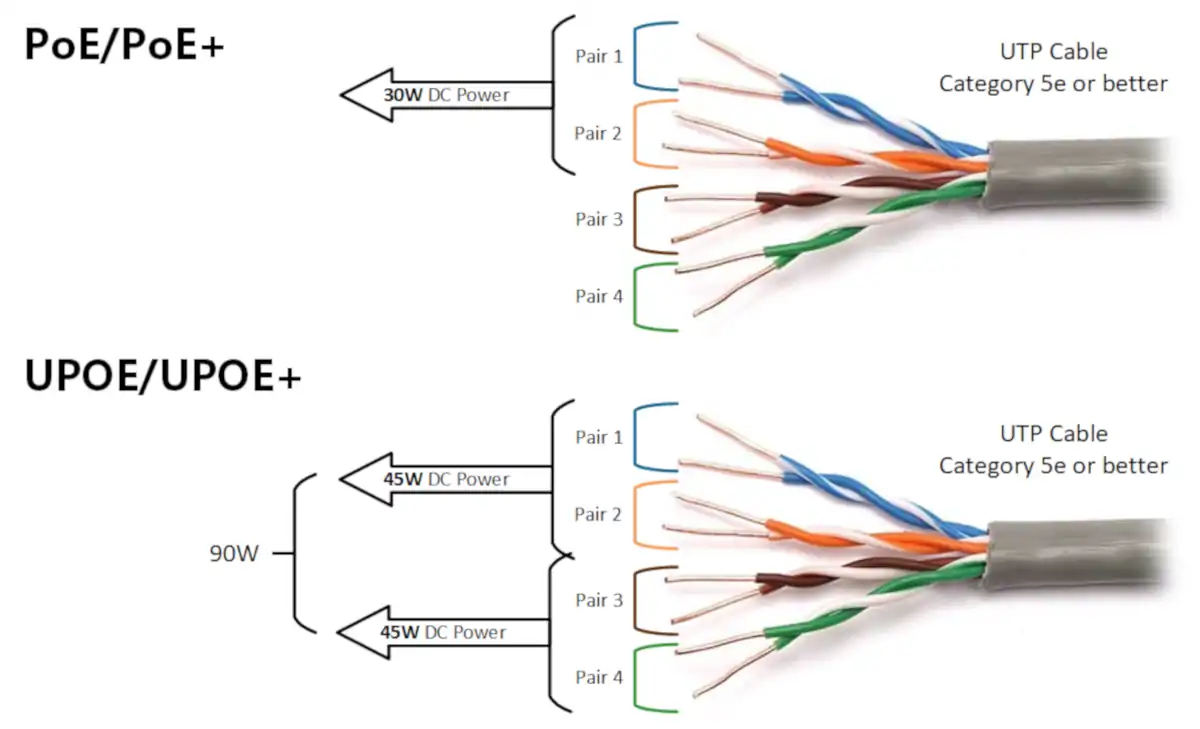
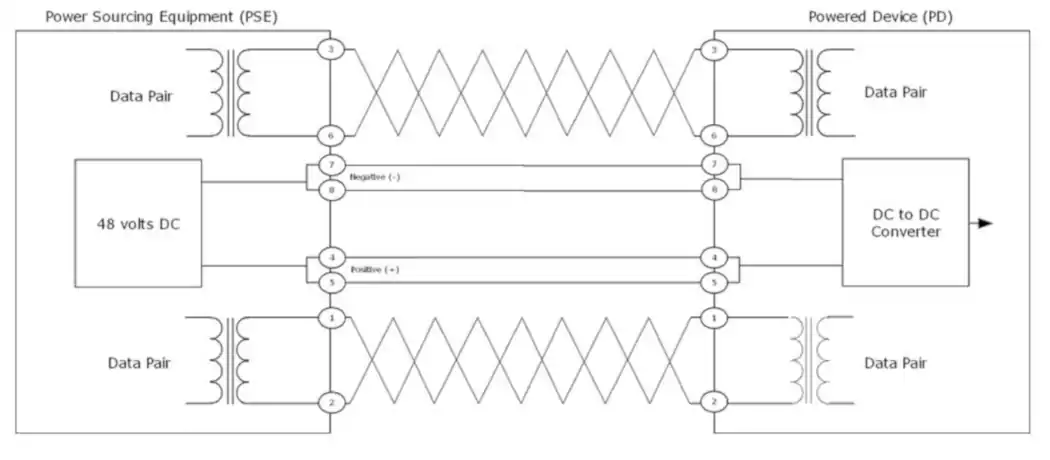
PoE and Cable Pairs
The PoE standard specifies the way that power is injected into the Ethernet cable pairs, and which pairs should be used.
-
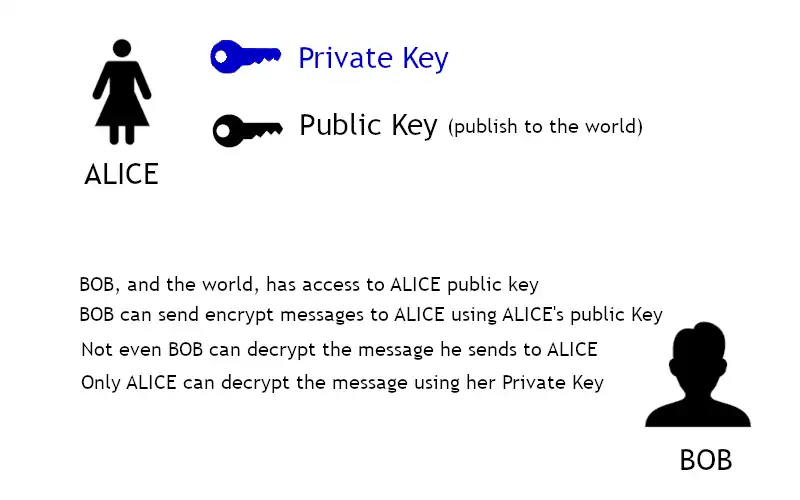
Asymmetric Encryption
Asymmetric encryption requires the use of two keys: a private key that is known only by its owner and a public key that is readily available to those who need to use it.
-
How Power Over Ethernet works – PoE Operations
Understanding how PoE works. The idle state and three operational states: detection, classification, and operation.
-
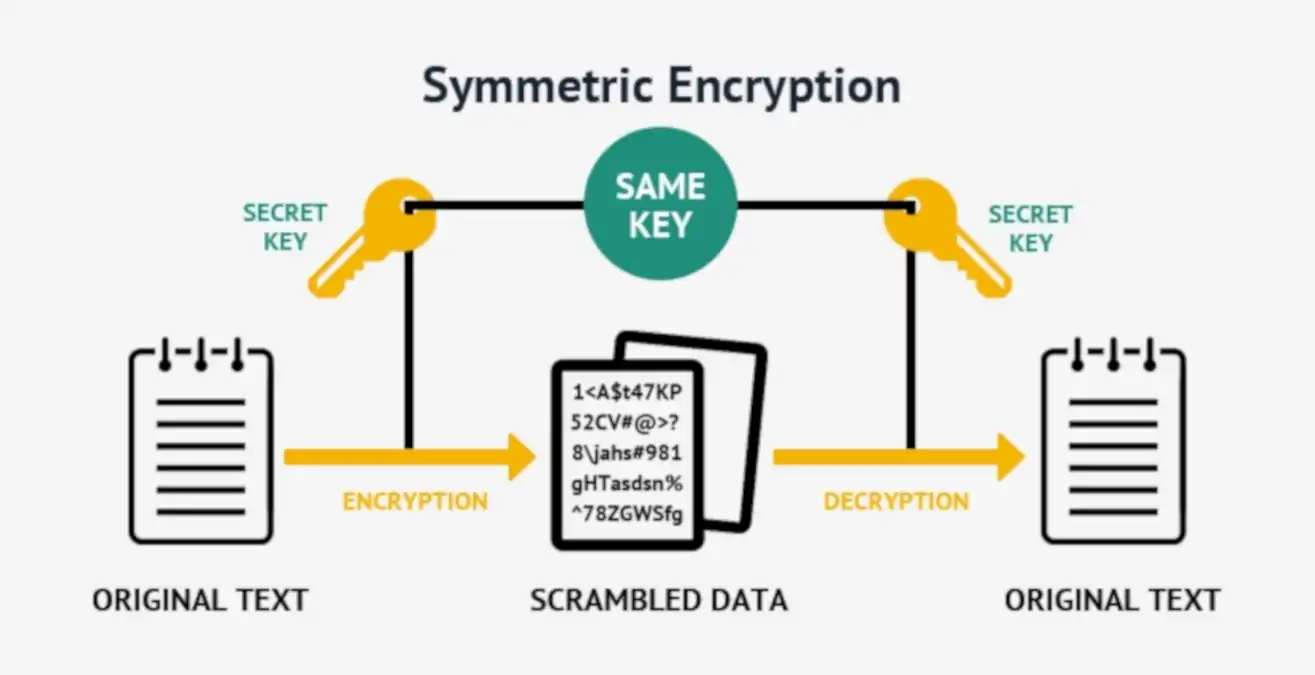
Symmetric Encryption
Symmetric encryption, or single-key encryption, is the most well-understood cryptography primitive.
-

PoE Device Roles and Type Parameters
For those who want to delve into the details of the Power over Ethernet technology, here we discuss PoE devices roles and type parameters.
-

History of Fiber Optics
It’s important to study the history of fiber optics to understand that the technology as it exists today is new and still evolving.
-
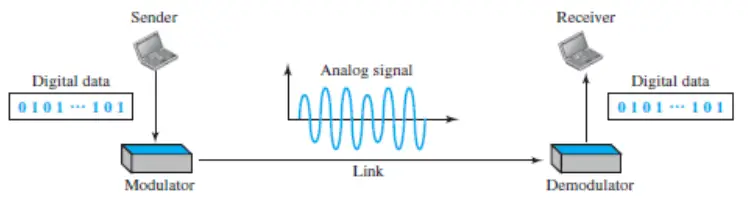
Digital-to-analog conversion
Digital-to-analog conversion is the process of changing one of the characteristics of an analog signal based on the information in digital data. Learn more…