The Editorial Team is a collective of technology enthusiasts, computer network engineers, and industry professionals dedicated to creating meticulously curated content for a diverse readership. With a combined experience spanning several decades, our team distills complex technology topics into clear, informative articles. Whether it’s networking fundamentals, cutting-edge AI insights, or in-depth guides on blockchain technology, the Editorial Team strives to provide reliable information that advances the understanding of technology for everyone from students to seasoned professionals.

Editorial Team’s mission
The Editorial Team’s mission extends beyond mere reporting; we aim to be the architects of understanding, constructing bridges over the rivers of jargon and complexity. From the foundational bricks of networking to the ever-evolving skies of cloud computing, we guide you through the technological labyrinth.
We take pride in our meticulous attention to detail and our unwavering commitment to accuracy, ensuring that each piece of information is a thread in the vast tapestry of technological knowledge. As we chart the course through the evolving landscape of technology, we invite our readers to join us on this exhilarating journey of discovery and growth. Together, we not only explore the current terrain of technology but also anticipate the horizons of tomorrow’s innovations.
Our Latest Articles
-

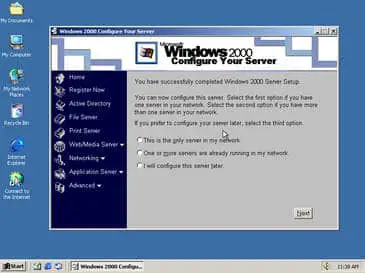
Local Security Database
Discover the Local Security Database in Windows – the core of user authentication and policy enforcement for uncompromised security.
-
Windows Workgroup
A Workgroup (in Windows Networks) is a logical grouping of networked computers that can share resources with each other. These resources might include files, printers, and other devices. A workgroup is often called a peer-to-peer network because all computers in a workgroup are equally important. In other words, no single computer “runs the network,” as in a…
-
WOW
WOW stands for “Win16 on Win32,” a component of the Microsoft Windows NT operating system that enables 16-bit Microsoft Windows applications (such as those designed to run on Windows 3.1 and Windows for Workgroups 3.11) to run properly on Windows NT’s 32-bit operating system. How WOW Works Like MS-DOS applications, 16-bit Windows applications (Win16 applications)…
-
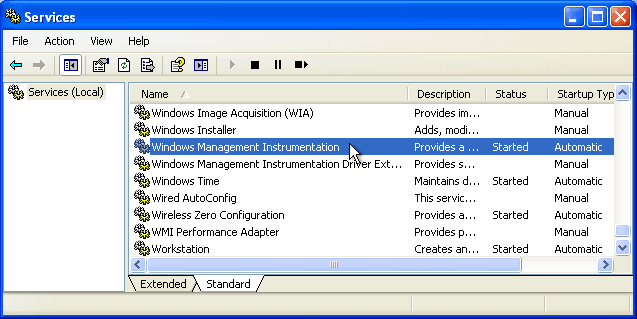
Windows Management Instrumentation (WMI)
Windows Management Instrumentation, or WMI, is Microsoft’s implementation of the Web-Based Enterprise Management (WBEM) architecture for enterprise-level network management. Administrators can use Windows Management Instrumentation (WMI) to track, monitor, and control computers, networking devices, and applications belonging to an enterprise network over the Internet by using a standard Web browser such as Microsoft Internet Explorer.…
-

Telco
Explore the transformation of Telcos from basic telephone service providers to all-in-one communications giants. Learn about their evolving roles, services, and impacts on our daily lives.
-
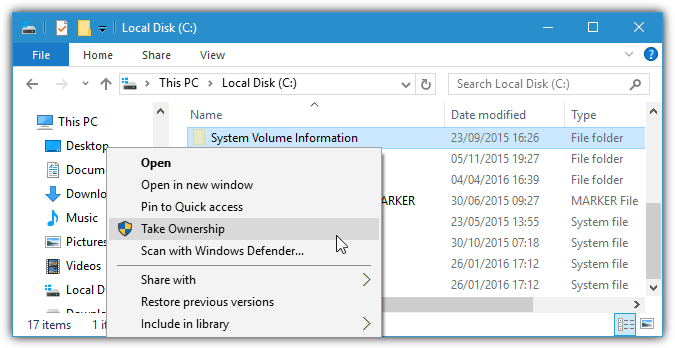
Taking Ownership (NTFS)
Taking Ownership is assuming ownership of an object – usually a file or a folder – on an NTFS volume and thereby gaining the right to share the object and assign permissions to it. The user who creates a file or folder on an NTFS volume is the owner.
-
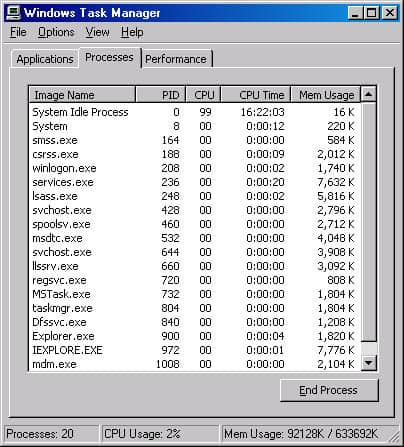
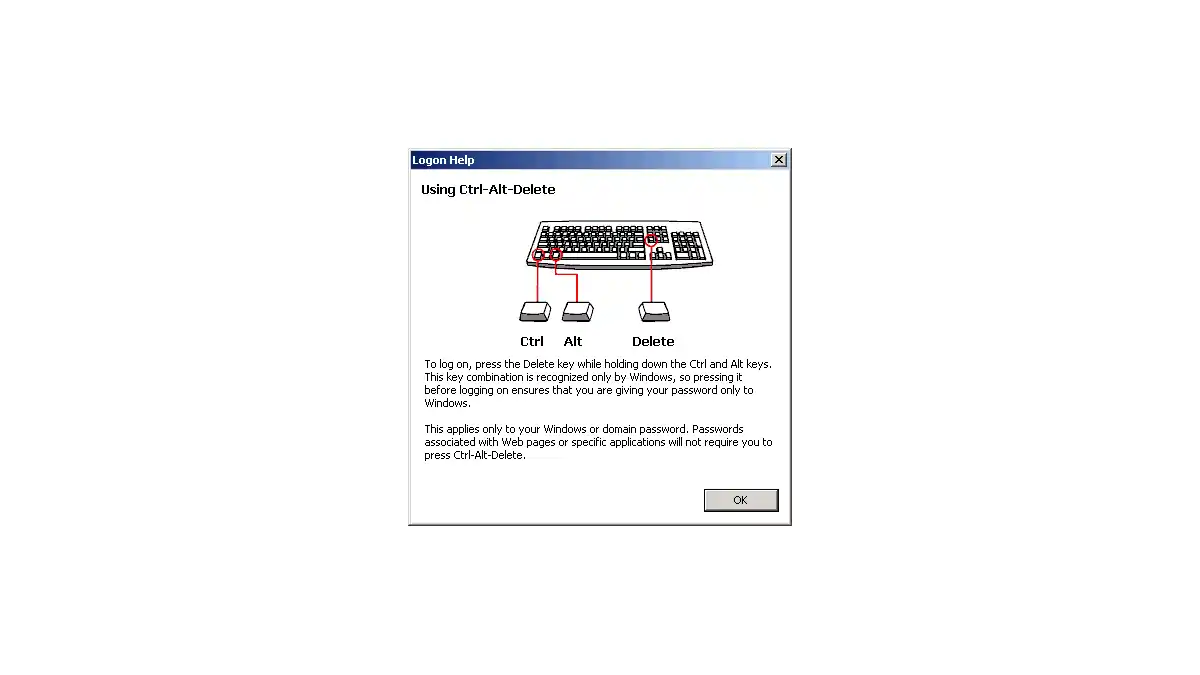
Task Manager
The Task Manager is a tool created by Microsoft for Windows NT and Windows 2000 that you can invoke by clicking the Task Manager button in the Windows Security dialog box. You access the dialog box by pressing Ctrl+Alt+Del, the secure attention sequence (SAS) keystroke combination. You can use Task Manager to: Start, view, change…
-
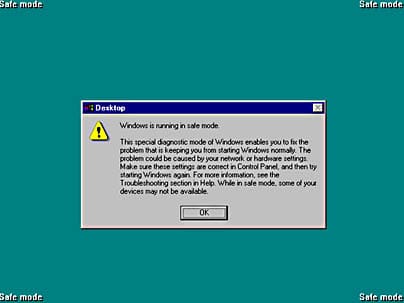
Safe Mode
Safe Mode in Microsoft ecosystem is a mode of starting Microsoft Windows 95, Windows 98, Windows 2000 and above that bypasses startup files and runs a basic set of files and drivers including mouse, keyboard, video, mass storage, and basic system services.