When you’re steering a large-scale Microsoft Windows network, the role of an Account Operator isn’t just helpful—it’s vital. These are the individuals who take care of the nitty-gritty details of user and group accounts, freeing up network administrators to focus on bigger tasks. Intrigued? Let’s delve deeper into what an Account Operator in Microsoft Windows truly entails.
In this article:
- What is an Account Operator?
- What Powers Do They Hold?
- Why Do You Need an Account Operator?
- The Account Operator Role in an Active Directory Environment: What Changes?
- The Final Word
- References
What is an Account Operator?
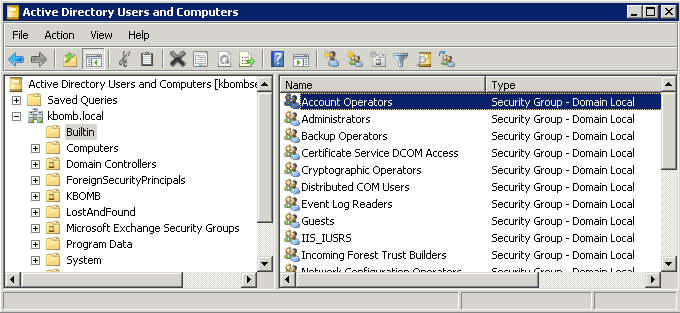
In Microsoft Windows systems, an Account Operator is designated to manage user and group accounts within a network. They are specifically authorized to function on domain controllers. To make a user an Account Operator, they need to be a member of the Account Operators Group.
Core Responsibilities:
- User Account Management: They create, delete, and modify user accounts as per organizational policies.
- Global Group Maintenance: They oversee the creation and management of global groups, streamlining permissions and roles.
- Local Group Oversight: They have the authority to handle local group accounts, customizing access and privileges.
- Local Profiles: Account Operators also manage local user profiles, ensuring optimal configurations for end-users.
2. What Powers Do They Hold?
Preassigned Rights:
- Local Login: Account Operators can log in locally to a domain controller.
- System Shutdown: They have the ability to shut down the system when required.
Limitations:
- No Member Server Access: Their reach is limited to domain controllers; member servers and workstations are beyond their jurisdiction.
Caution:
Due to the extensive rights given to Account Operators, it’s recommended to assign this role only in large enterprise environments. For smaller networks, these tasks are usually the responsibility of the network administrator.
3. Why Do You Need an Account Operator?
Efficiency:
Managing accounts can be a time-consuming affair. Account Operators streamline the process, making it easier and faster.
Specialization:
With Account Operators focused on accounts, network administrators can direct their attention to more intricate and large-scale issues.
Compliance:
Their role is essential for ensuring that user accounts and groups align with compliance standards, minimizing risks and vulnerabilities.
4. The Account Operator Role in an Active Directory Environment: What Changes?
If your network is already employing the capabilities of Microsoft’s Active Directory (AD), you might wonder how the role of an Account Operator differs. The introduction of Active Directory into your Windows environment does bring some nuances to this crucial role. Let’s explore these subtle yet significant changes.
What Stays the Same?
First and foremost, the core responsibilities remain largely unchanged. Account Operators still manage user accounts, global and local groups, and maintain local profiles. However, in an Active Directory environment, the scope and limitations of their abilities do see some modifications.
Core Functions in Active Directory:
- Organizational Unit (OU) Management: In addition to basic account management, Account Operators can create, delete, or modify OUs, which is not possible in a non-AD environment.
- Group Policy Association: They can associate Group Policies with OUs but cannot create or modify the Group Policies themselves.
What Changes?
Limitations:
- Domain-Wide Operations: In a native Active Directory setup, Account Operators cannot manage accounts that are members of the Domain Admins or Administrators group. This is a critical security feature.
- Schema Modifications: While they can interact with OUs, Account Operators can’t modify the Active Directory schema, an action reserved for administrators.
Extended Capabilities:
- Fine-Grained Permissions: AD allows for more precise delegation of responsibilities. You can customize the Account Operator’s permissions to a granular level using the Delegation of Control wizard.
- Attribute Management: With AD, Account Operators can also manage additional attributes of user accounts, such as login scripts and home folder locations.
Security Concerns:
- Privilege Escalation Risks: In AD environments, be cautious when delegating permissions to Account Operators. Poorly configured permissions could lead to unintentional privilege escalation.
Best Practices in Active Directory
- Least Privilege Policy: Always follow the principle of least privilege when setting up Account Operator roles in an AD environment.
- Audit & Monitor: Regularly audit Account Operator activities. Active Directory’s built-in auditing features make this task easier and more efficient.
- Use Role-Based Access Control (RBAC): Utilize AD’s RBAC features to clearly define what Account Operators can and cannot do, ensuring both functionality and security.
- Credential Management: Implement strong password policies and multi-factor authentication (MFA) to ensure that Account Operators’ credentials are as secure as possible.
- Regular Training: Conduct regular training sessions for Account Operators to keep them updated about security protocols, compliance requirements, and best practices.
- Disaster Recovery Plans: Always have a fallback strategy. In case an Account Operator makes an error or there is a system failure, ensure that recovery plans are both up-to-date and tested.
Wrapping Up
In an Active Directory environment, the role of an Account Operator gains additional layers of complexity and security. Understanding these differences will help you leverage the full benefits of having Account Operators in an AD setup while mitigating potential risks.
For further insights into Active Directory roles and permissions, stick with Network Encyclopedia. We’ve got you covered with comprehensive, authoritative guides.
5. The Final Word
An Account Operator plays a crucial role in fine-tuning your Microsoft Windows network. They relieve network administrators from routine tasks and contribute to a smoother, more secure operational flow. Therefore, understanding their role, powers, and limitations is essential for anyone involved in network administration.
6. References
- “Active Directory: Designing, Deploying, and Running Active Directory” by Brian Desmond and Joe Richards
- “Windows Server 2019 Inside Out” by Orin Thomas
- Microsoft Docs – Account Operators
- TechNet Magazine – Best Practices for Delegating Active Directory Administration