In the landscape of Microsoft Windows operating systems, the Local Security Authority (LSA) plays a pivotal role in safeguarding user interactions and system integrity. This critical component, responsible for managing interactive logons, embodies the core of Windows security by verifying user credentials and enforcing policy. With the evolution of Windows through versions 10 and 11, understanding the LSA’s functionalities and its relevance in modern contexts is essential for computer science students and professionals alike.
This article aims to demystify the LSA, providing insights into its operations, updates in recent Windows iterations, and its ongoing importance in system security architecture.
Table of Contents:
- Understanding Local Security Authority (LSA)
- How it Works
- LSA in Windows 10 and 11
- Components of LSA
- LSA Security Mechanisms
- LSA and Active Directory
- Best Practices for Managing LSA Security
- References

1. Understanding Local Security Authority (LSA)
Definition and Key Responsibilities
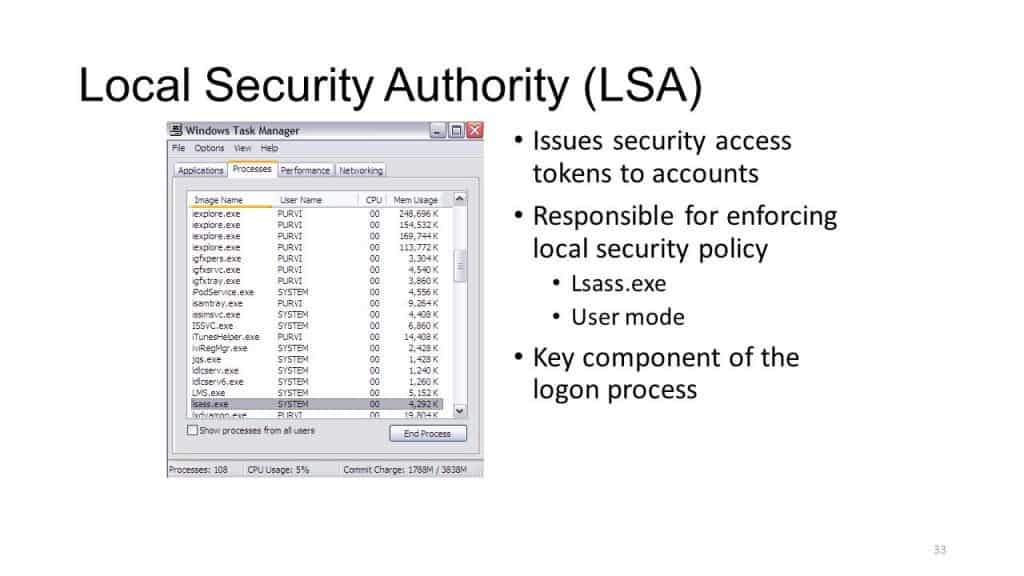
The Local Security Authority (LSA) is a critical component within the Microsoft Windows operating system, tasked with enforcing security policies on the system. It acts as the gatekeeper for accessing the computer, handling user logins, authentication, and authorization processes. The LSA is responsible for verifying user credentials when they attempt to access the system and determines whether they should be granted access based on configured policies. Additionally, it manages password changes and creates access tokens, which define the resources and operations the user can access and perform during their session.
The Local Security Authority (LSA) is responsible for managing interactive logons to the system.
Historical Context and Evolution
Historically, the LSA has been a cornerstone of Windows security since its early versions, evolving alongside the operating system to address the growing complexity and sophistication of cybersecurity threats. In earlier Windows versions, the LSA’s primary focus was on managing local and network logins using various authentication protocols. Over time, as Windows transitioned from a predominantly standalone operating system to a networked environment, the role of the LSA expanded to include more advanced security mechanisms, such as Kerberos protocol support for domain environments and integration with Active Directory.
2. How it Works
When a user attempts to log on locally to the system by entering a username and password in the logon dialog box, the logon process invokes the LSA, which passes the user’s credentials to the Security Accounts Manager (SAM), which manages the account information stored in the local SAM database.
The SAM compares the user’s credentials with the account information in the SAM database to determine whether the user is authorized to access the system. If it finds the user account information in the SAM database, the SAM authenticates the user by creating a logon session and returning the security identifier (SID) of the user and the SIDs of global groups of which the user is a member to the LSA.
The LSA then grants the user an access token that contains the user’s individual and group SIDs and their rights; these enable the user to access resources for which he or she has permissions.
The LSA is also responsible for other security-related functions, including the following:
- Managing the local security policy on the computer, such as maximum number of logon attempts allowed and account lockout settings
- Managing the audit policy on the computer and logging any events generated by the Security Reference Monitor
- Provides interactive user authentication services.
- Generates or obtains MSFT Access Tokens.
3. LSA in Windows 10 and 11
Updates and Enhancements from Previous Versions
With the advent of Windows 10 and Windows 11, the LSA has seen significant updates and enhancements to strengthen the security posture of the operating system. These updates include improvements in credential protection and isolation, leveraging modern hardware capabilities and virtualization technologies. For instance, Credential Guard in Windows 10 and Windows 11 uses virtualization-based security to isolate secrets (such as NTLM hashes and Kerberos ticket-granting tickets) so that they are not accessible to the rest of the system, effectively mitigating certain types of pass-the-hash and pass-the-ticket attacks.
How LSA Integrates with Modern Security Features
The integration of the LSA with modern security features in Windows 10 and Windows 11 demonstrates Microsoft’s commitment to elevating system security. The LSA works in conjunction with features like Windows Hello, which provides a more personal and secure way for users to log into their Windows devices using biometrics or a PIN. This integration ensures that the authentication process is not only more secure but also more user-friendly.
Furthermore, the LSA’s role in supporting Azure Active Directory and cloud-based identities showcases its adaptability to modern, cloud-centric computing environments. By supporting single sign-on (SSO) capabilities for applications and services both on-premises and in the cloud, the LSA facilitates a seamless and secure user experience across various platforms and devices.
In summary, the evolution of the LSA in Windows 10 and Windows 11 reflects a strategic adaptation to the changing landscape of IT security, incorporating advanced protection mechanisms and embracing cloud integration to meet the needs of today’s users and organizations. This evolution ensures that the LSA remains a fundamental pillar of Windows security, capable of addressing both traditional and emerging threats.
4. Components of LSA
Breakdown of LSA Architecture
The architecture of the Local Security Authority (LSA) in Windows is designed to be both robust and flexible, enabling it to manage various security-related functionalities efficiently. At its core, the LSA consists of the Local Security Authority Subsystem Service (LSASS), which runs as a process on Windows systems. This service is responsible for enforcing security policies, handling authentication and authorization processes, and managing credentials and access tokens.
The LSA architecture is modular, comprising several components that interact with each other to provide comprehensive security services:
- LSA Server: Acts as the central authority for managing all security policy-related activities on the system.
- Security Support Provider Interface (SSPI): A set of APIs that allow for secure communication between applications and security support providers.
- Security Support Providers (SSPs): These are dynamic-link libraries (DLLs) that implement specific authentication protocols, such as NTLM or Kerberos.
- Authentication Packages: Responsible for authenticating users based on credentials, like passwords or smart card PINs, and for creating access tokens upon successful authentication.
Role of Security Support Provider (SSP) and Authentication Packages
Security Support Providers play a crucial role in the LSA architecture by implementing specific authentication protocols needed for secure communications. For example, the Kerberos SSP implements the Kerberos authentication protocol, while the NTLM SSP provides support for NTLM authentication. These SSPs are invoked by the SSPI to facilitate authentication, integrity, and confidentiality services for user and application data.
Authentication Packages, on the other hand, are components that directly interact with the LSASS process to authenticate users logging onto the system. They validate the credentials provided by the user against the security database (which could be the local security database or Active Directory in a domain environment) and create access tokens that define the user’s identity, privileges, and access rights on the system.
5. LSA Security Mechanisms
Credential Validation Process
The credential validation process is a critical function of the LSA, ensuring that only authorized users can access the system. When a user attempts to log in, their credentials are passed to the appropriate Authentication Package by the LSASS. The Authentication Package then verifies these credentials against the security database. For password-based authentication, this typically involves comparing a hashed version of the provided password against the hash stored in the database.
If the credentials are valid, the Authentication Package notifies the LSASS, which then generates an access token for the user. This token contains the user’s security identifiers (SIDs), user rights, and group memberships, and it is used to establish the user’s session and enforce security policies throughout their interaction with the system.
Policy Enforcement and Access Control
The LSA is also responsible for enforcing security policies and access control on the system. This involves determining which resources a user can access and what actions they can perform. Policy enforcement is achieved through the use of access tokens, group policies, and security descriptors associated with resources.
Access tokens, generated after successful authentication, contain information about the user’s privileges and group memberships. These tokens are used by the operating system to make access control decisions, ensuring that users can only interact with resources for which they have the appropriate rights.
Group policies, configured by administrators, define security settings and permissions for users and computers within an organization. The LSA applies these policies to control access to system resources, configure security options, and manage user environments.
Security descriptors associated with files, folders, and other objects define the specific permissions granted to users and groups. The LSA evaluates these descriptors in conjunction with access tokens to enforce access controls, ensuring that operations like reading, writing, or executing are permitted only for authorized users.
Together, these mechanisms enable the LSA to maintain a secure environment on Windows systems, validating credentials, enforcing policies, and controlling access to ensure that only authorized users and processes can access sensitive resources.
6. LSA and Active Directory
Interaction with Active Directory for Network Logons
In a domain environment, the Local Security Authority (LSA) plays a crucial role in facilitating network logons through its interaction with Active Directory (AD). When a user attempts to log onto a domain-joined computer, the LSA communicates with a domain controller to authenticate the user’s credentials against the Active Directory database. This process typically involves the use of the Kerberos authentication protocol, where the LSA acts as a client requesting access on behalf of the user.
The LSA sends a request to the Key Distribution Center (KDC) service running on the domain controller, including a Ticket Granting Ticket (TGT) request encrypted with the user’s password hash. If the credentials are verified, the KDC issues a TGT and session keys to the user’s system. The LSA then uses this TGT to request access tokens for accessing resources within the domain, effectively managing the user’s session and enforcing security policies as defined in Active Directory.
LSA’s Role in Domain Environments
Within domain environments, the LSA’s role extends beyond just processing logon requests. It is integral in implementing security policies, managing user rights, and controlling access to resources across the network. The LSA ensures that security principles and policies defined in Active Directory, such as password policies, user rights assignments, and access control lists (ACLs), are enforced on each domain-joined computer. This centralized approach to security management allows for consistent policy enforcement, streamlined user access management, and enhanced overall security posture within the domain.
7. Best Practices for Managing LSA Security
Recommendations for System Administrators
System administrators can take several steps to enhance the security of the LSA and protect against potential vulnerabilities:
- Implement Least Privilege Principle: Ensure that users operate with the minimum level of access required for their roles to limit the potential impact of compromised credentials.
- Enable LSA Protection: Configure LSA Protection to run the LSASS process in a protected mode, preventing unauthorized access and modification by malware or other malicious actors.
- Regularly Update Systems: Keep Windows systems updated with the latest security patches to protect against known vulnerabilities that could be exploited to compromise the LSA.
Tools and Techniques for Securing LSA
Several tools and techniques can be employed to help secure the LSA:
- Security Configuration Wizard (SCW): Use SCW to simplify the configuration of security policies, including those related to LSA, on Windows servers.
- Windows Defender Credential Guard: Enable Credential Guard to use virtualization-based security to isolate and protect LSA secrets against pass-the-hash attacks.
- Audit and Monitor LSA Operations: Use Windows Event Logging and other monitoring tools to track LSA operations and detect suspicious activities that could indicate a security breach.
8. References
- “LSA Authentication“, by Microsoft Learn
- Microsoft Security Blog
- “Windows Internals, Part 1” by Mark Russinovich, David A. Solomon, and Alex Ionescu
- “Securing Windows Server 2016” by Timothy Warner